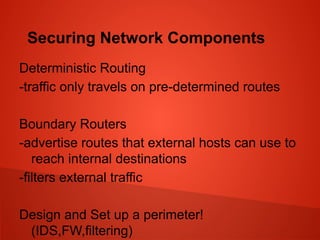
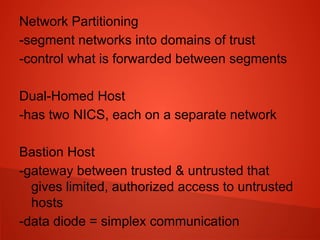
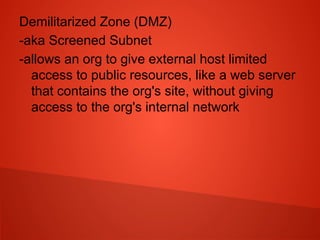
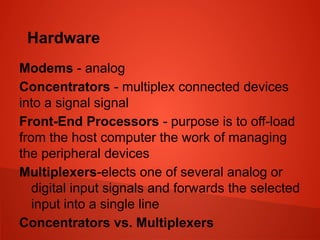
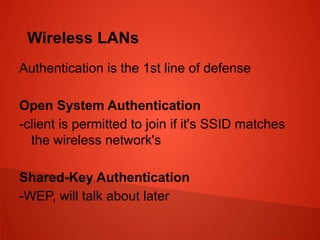
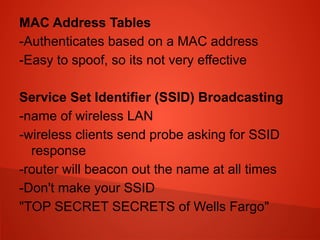
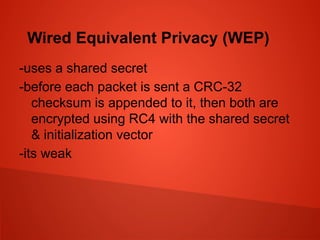
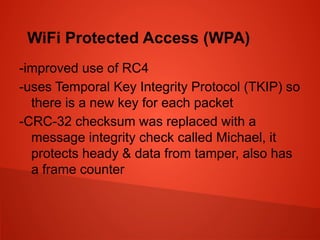
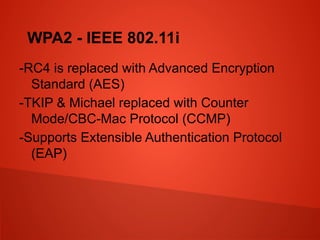
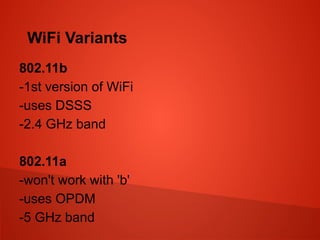
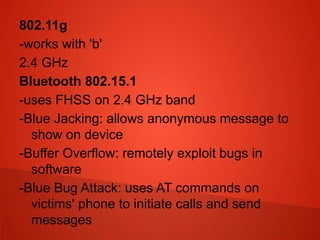
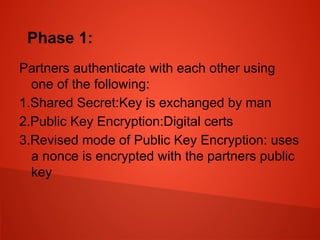
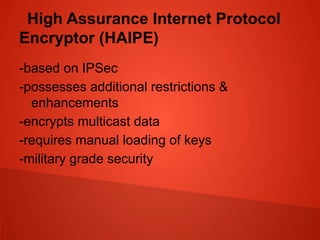
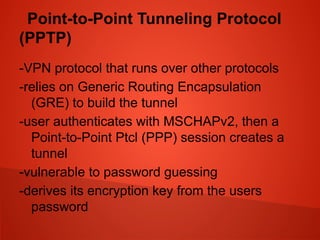
This document summarizes network components and security techniques. It discusses network segmentation, demilitarized zones, firewalls, routers, switches, wireless networking, encryption, and VPNs. It also covers securing communication channels, voice over IP, multimedia collaboration, and instant messaging protocols. The key topics covered are network design principles, routing, wireless standards, encryption methods, and virtual private networks.