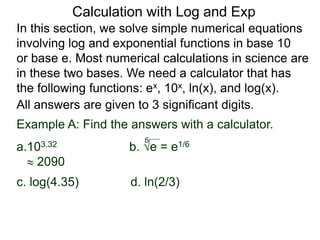
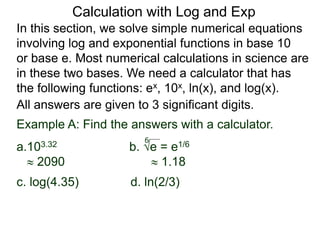
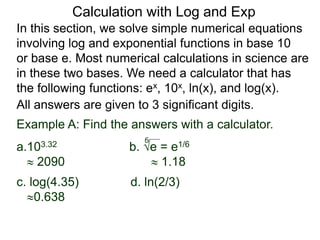
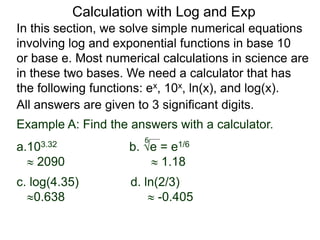
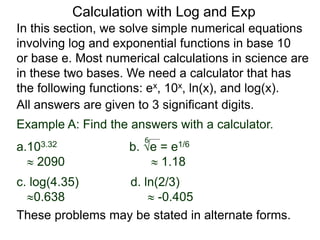
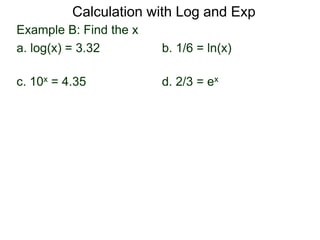
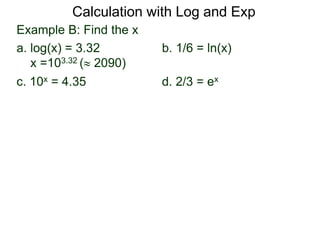
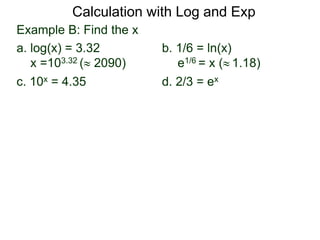
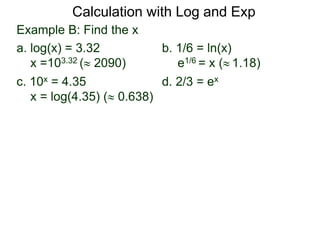
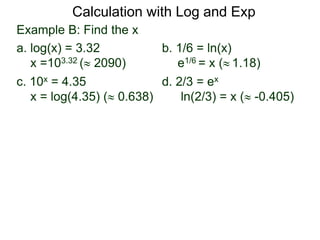
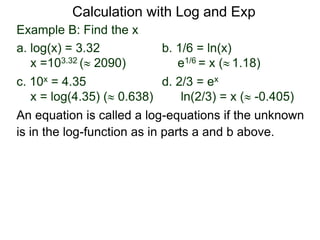
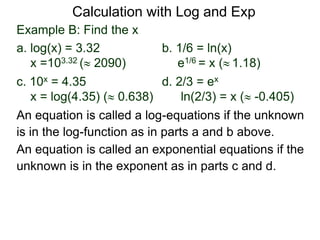
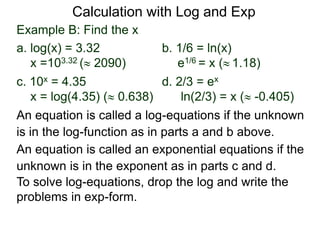
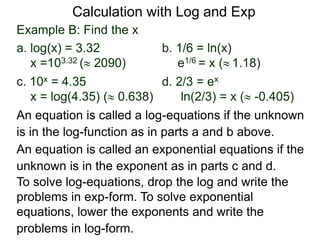
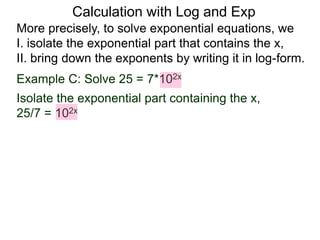
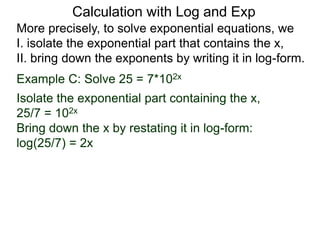
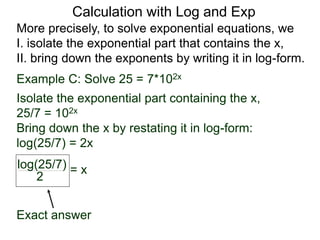
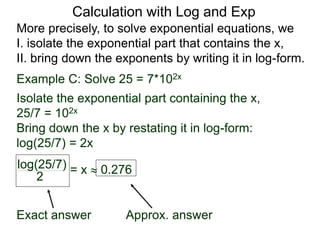
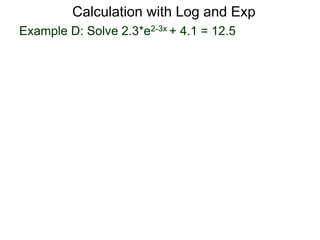
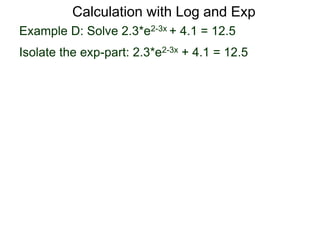
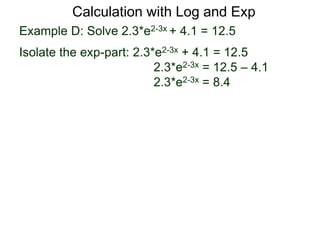
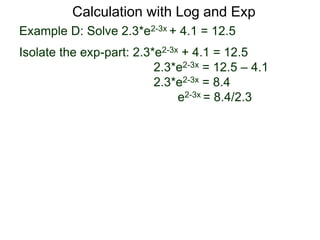
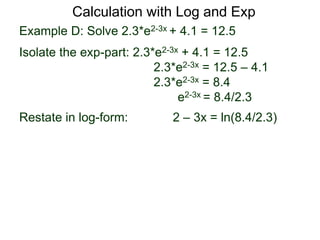
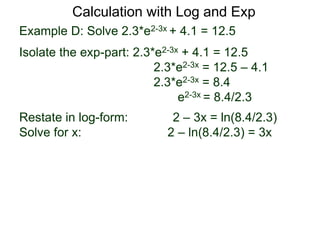
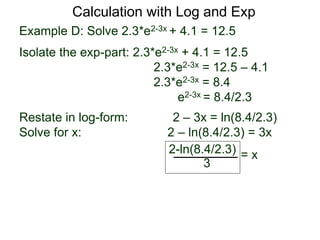
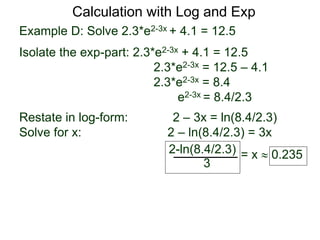
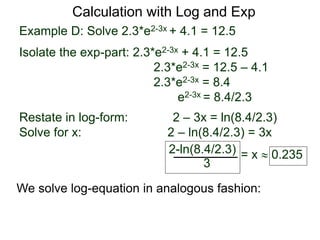
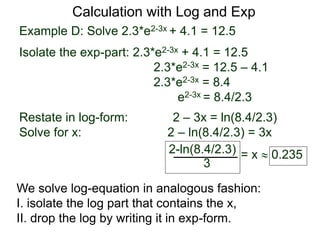
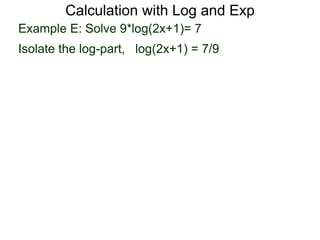
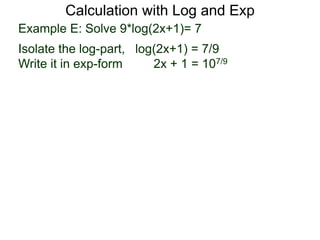
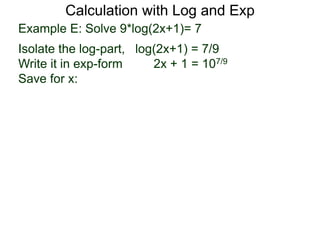
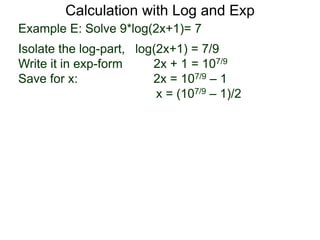
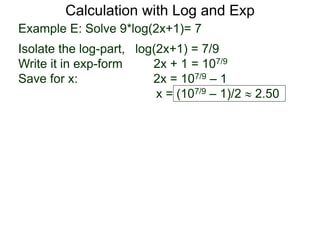
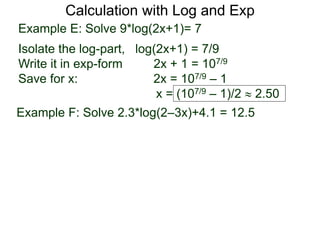
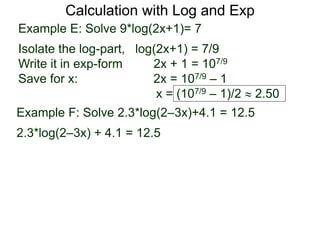
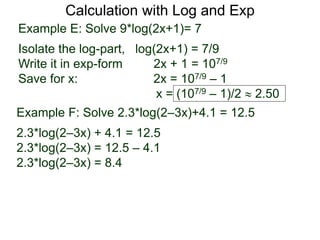
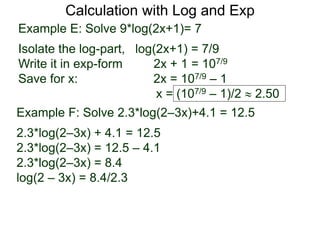
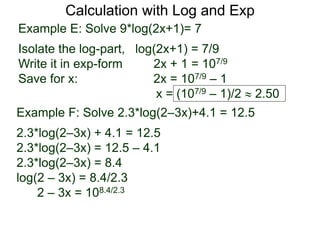
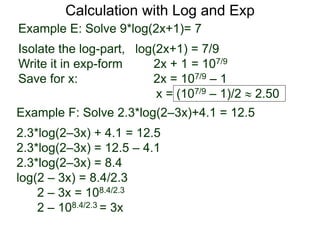
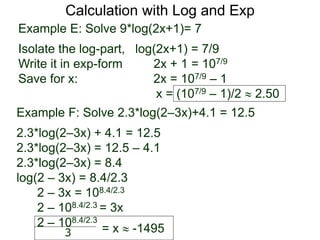
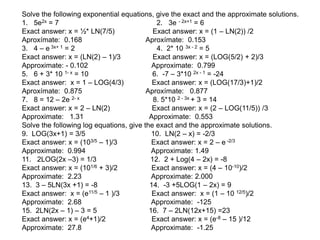
The document discusses solving numerical equations involving logarithmic and exponential functions in base 10 or base e. It provides examples of solving log and exponential equations by isolating the part containing the unknown, then rewriting the equation in the opposite form (log to exponential or exponential to log). The key steps outlined are: 1) isolate the exponential/log part containing the unknown, 2) rewrite the equation by "bringing down" exponents as logarithms or vice versa. Several examples are worked through demonstrating these steps.