This document discusses different numeral systems including binary, decimal, and hexadecimal. It provides details on:
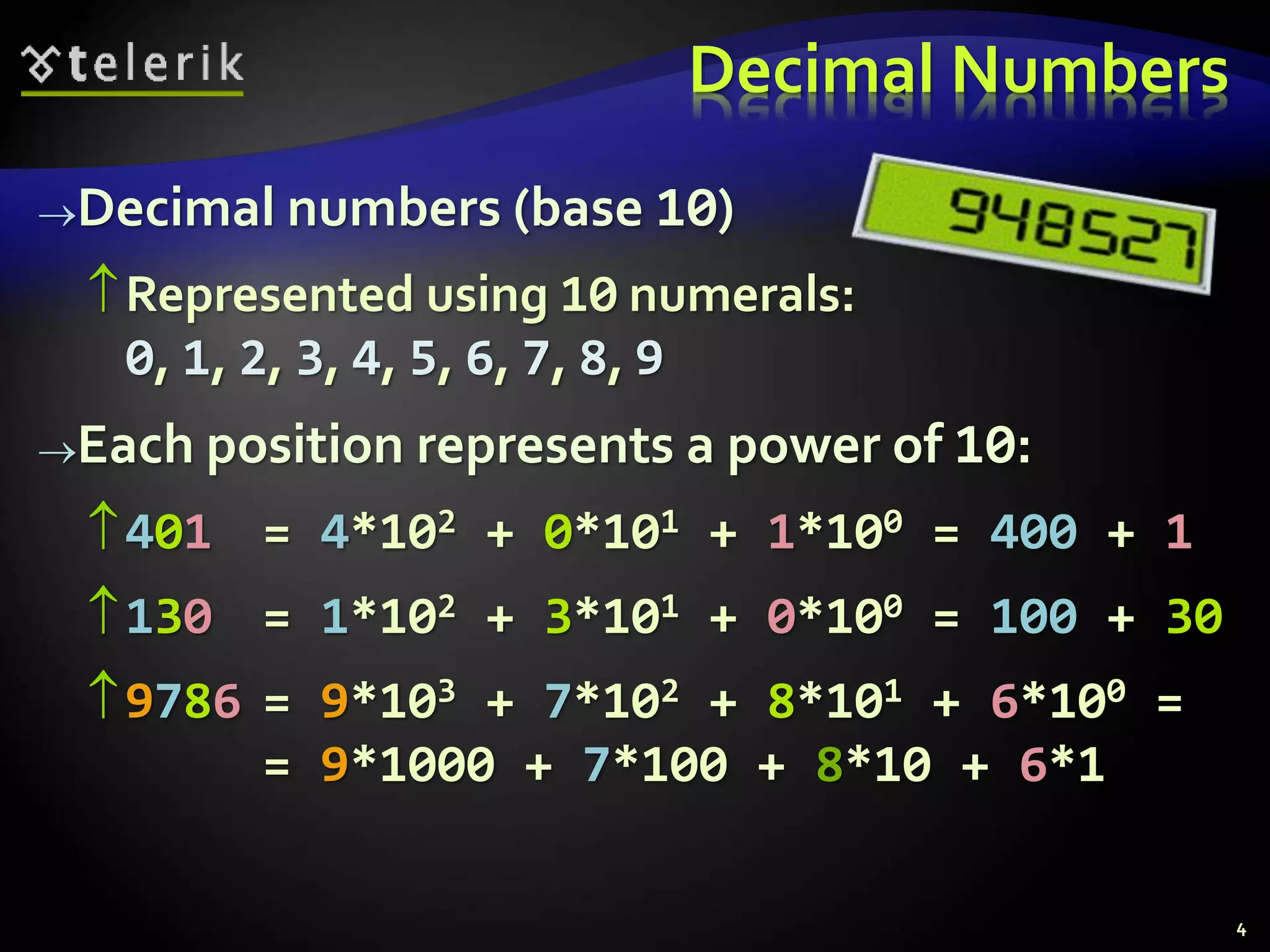
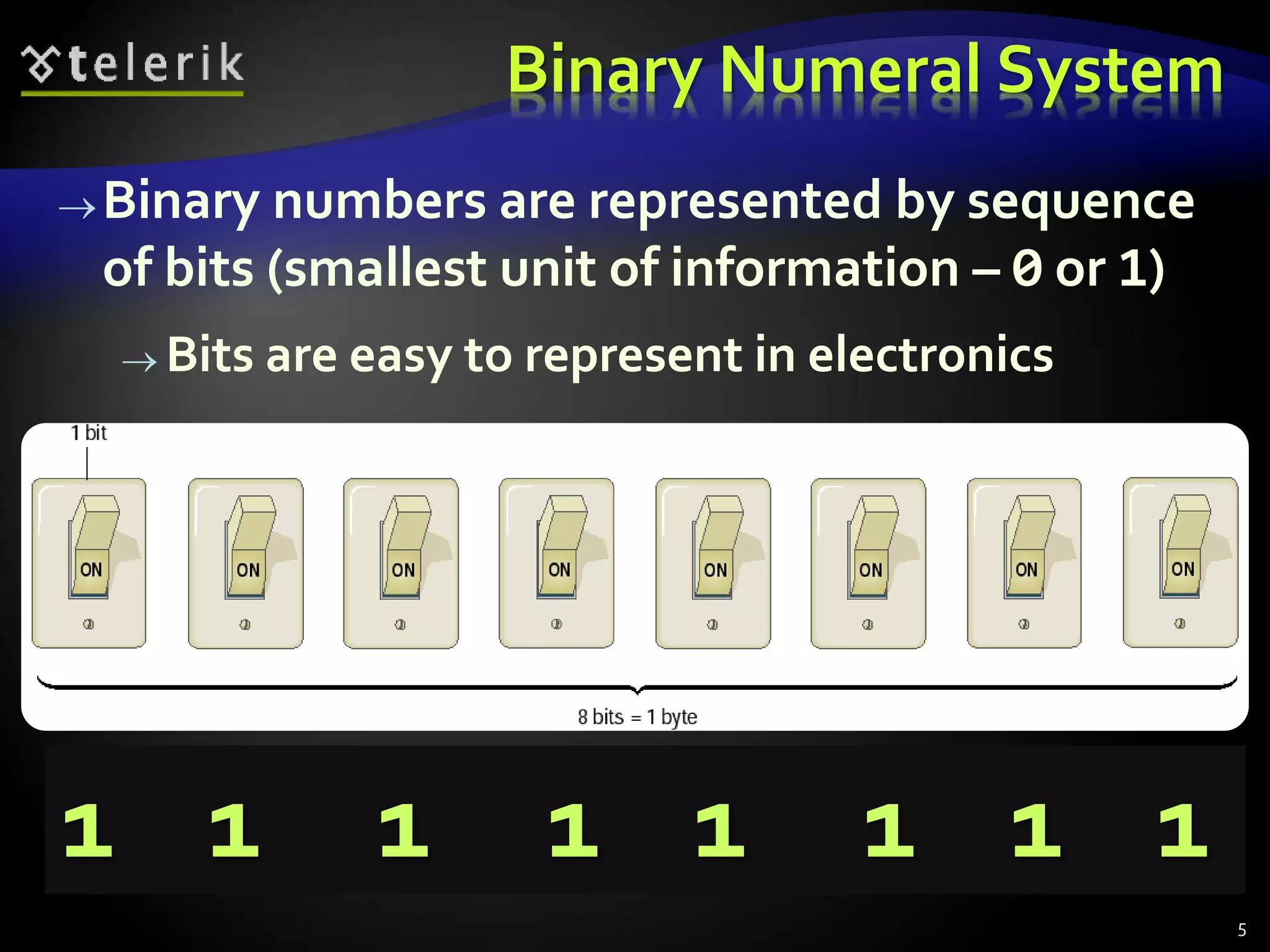
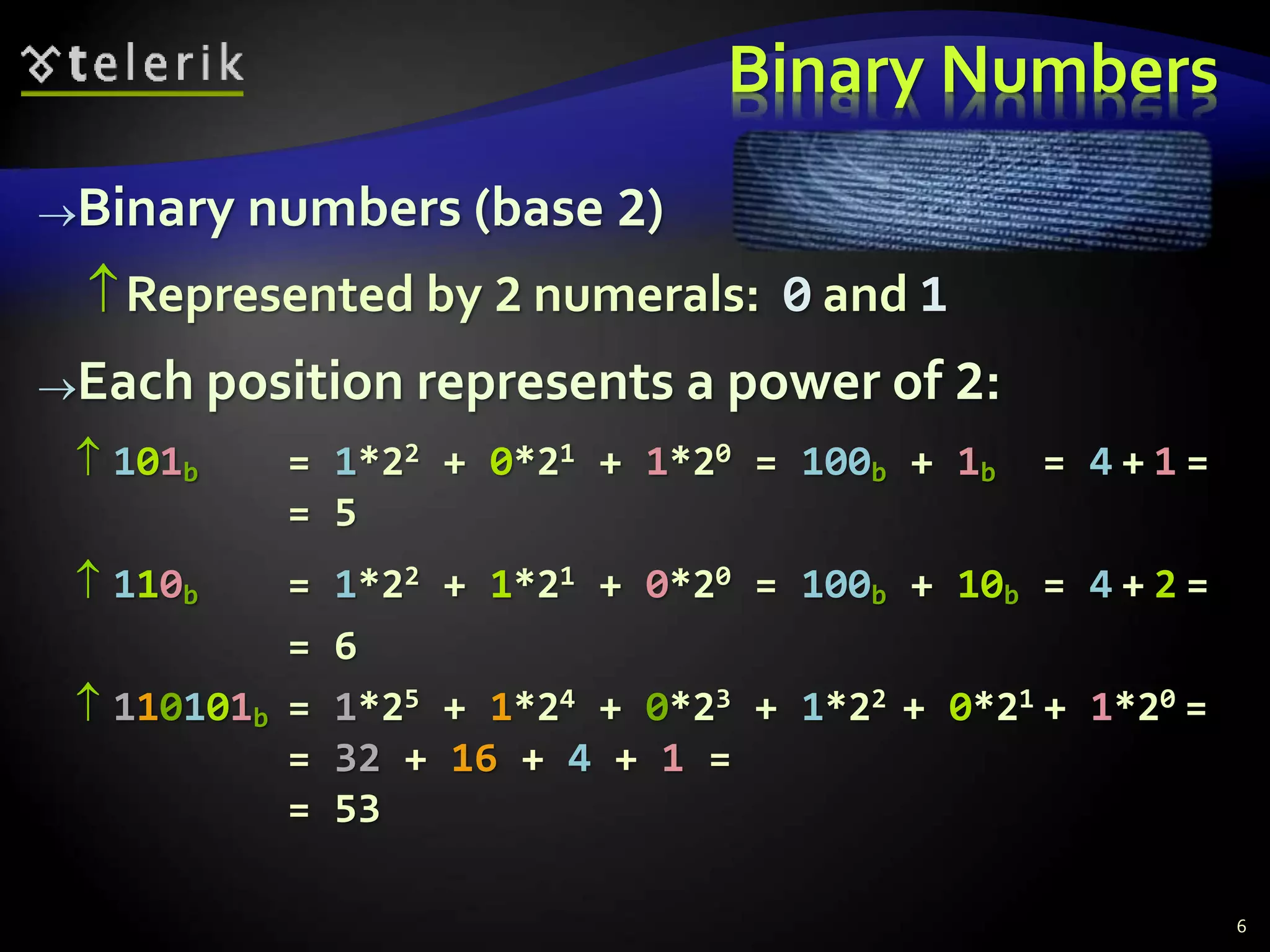
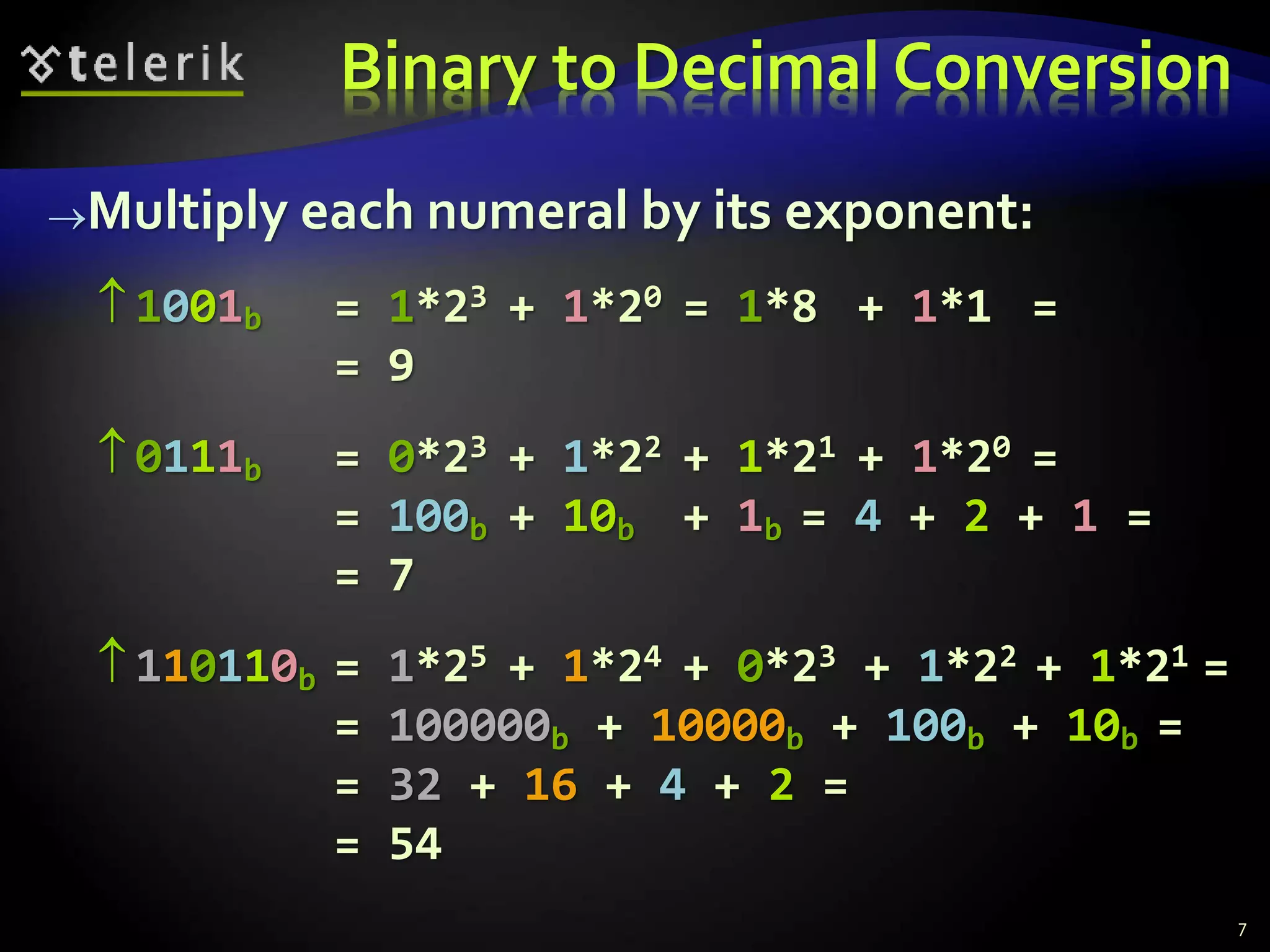
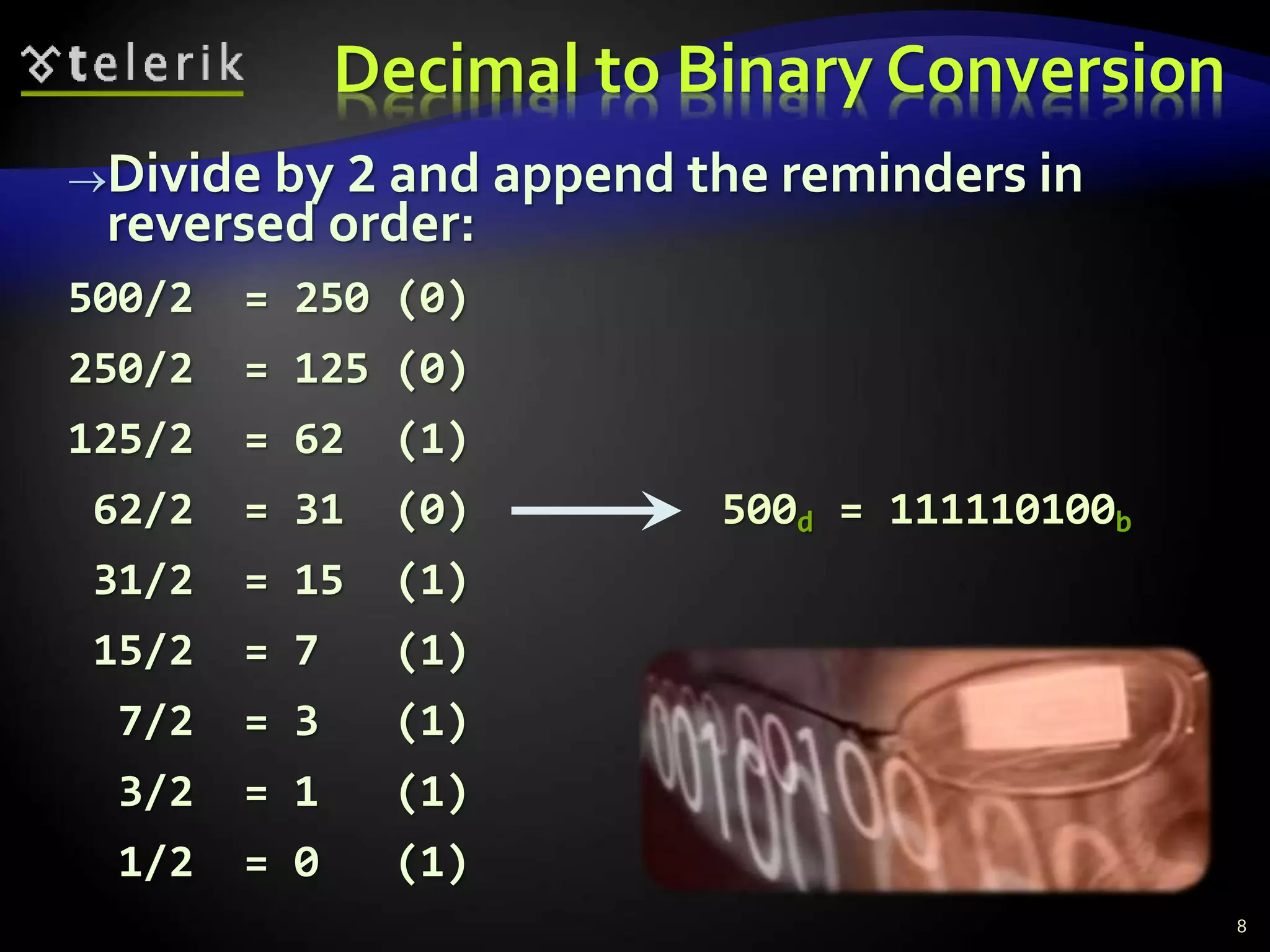
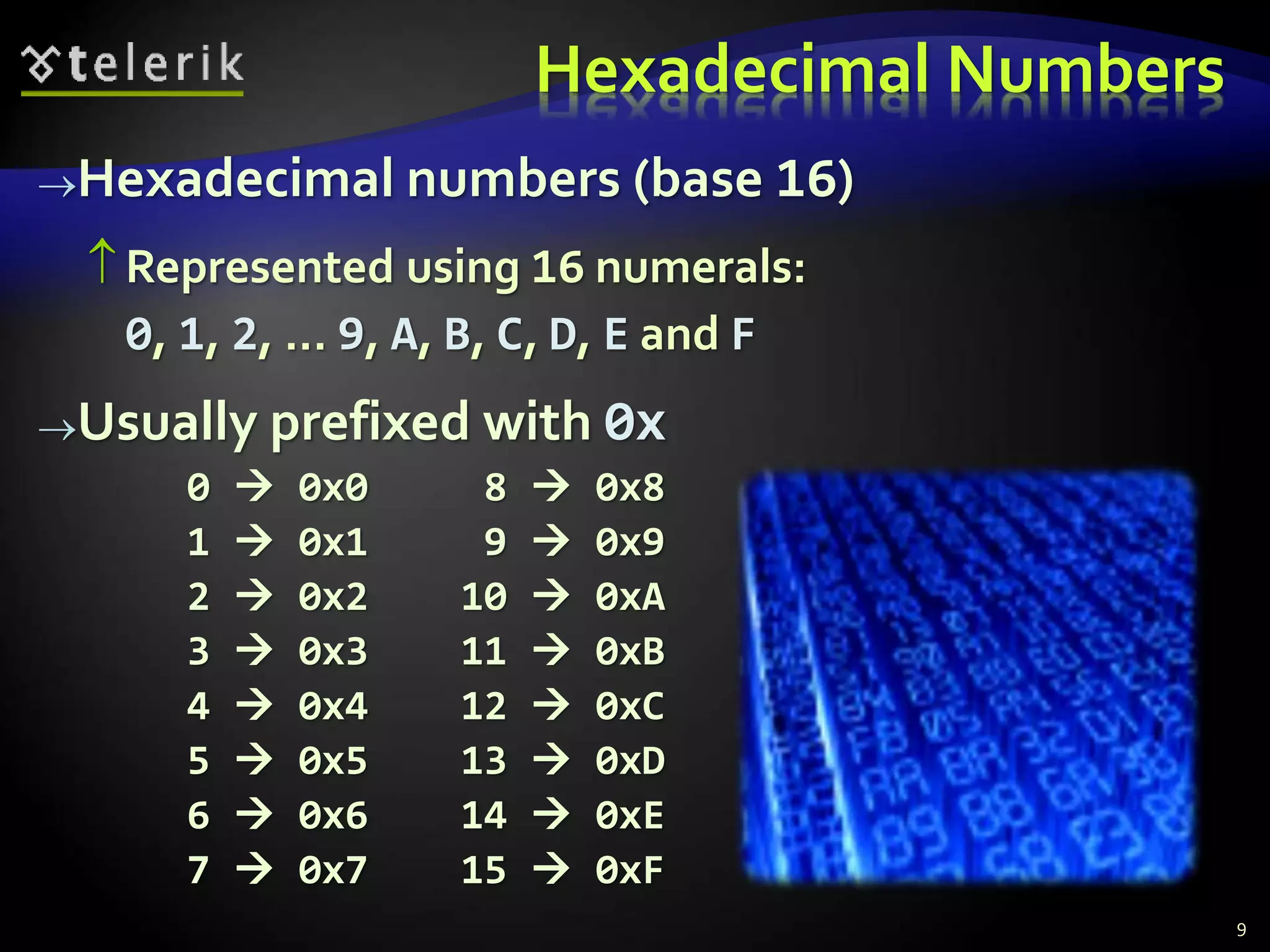
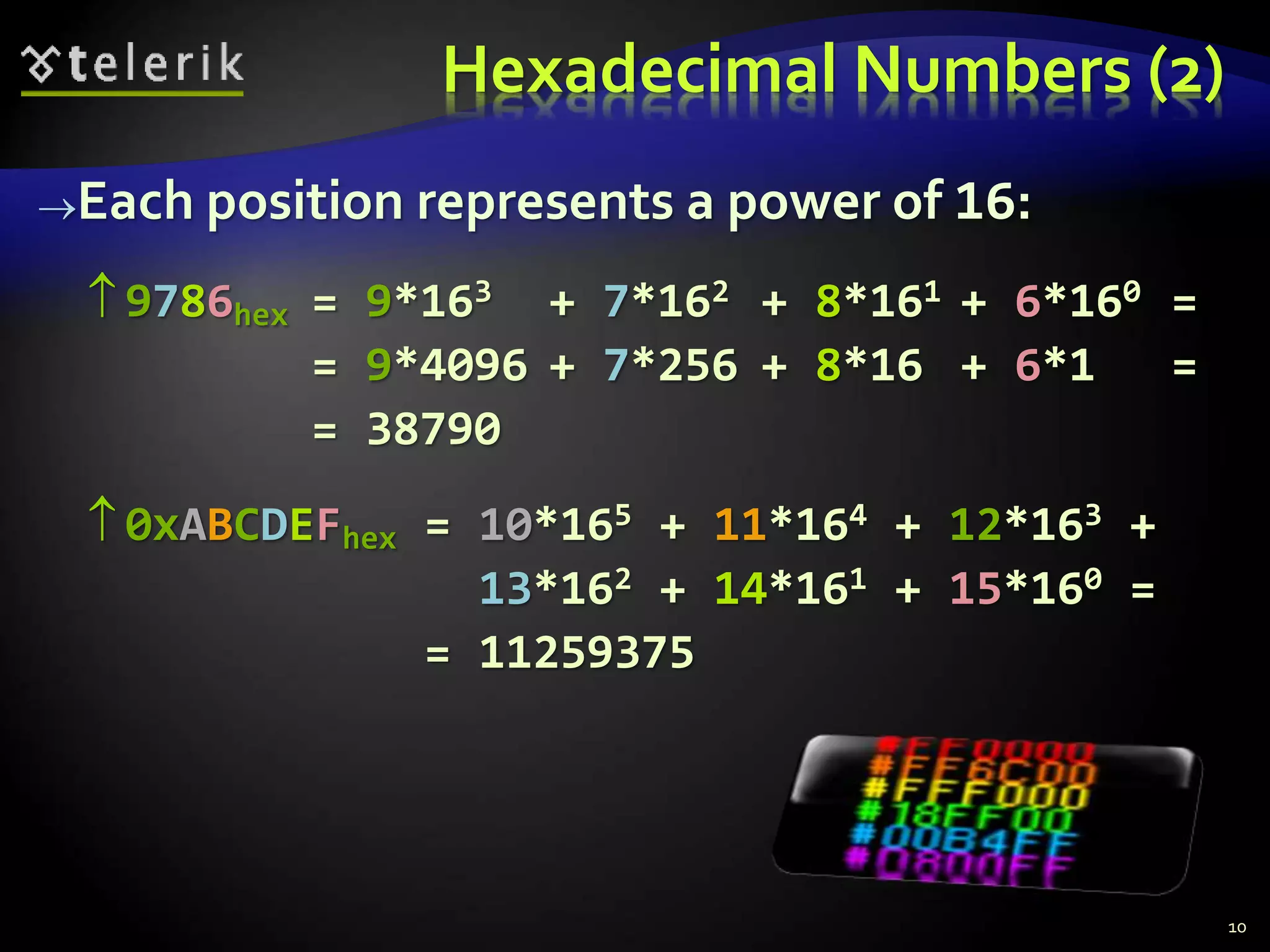
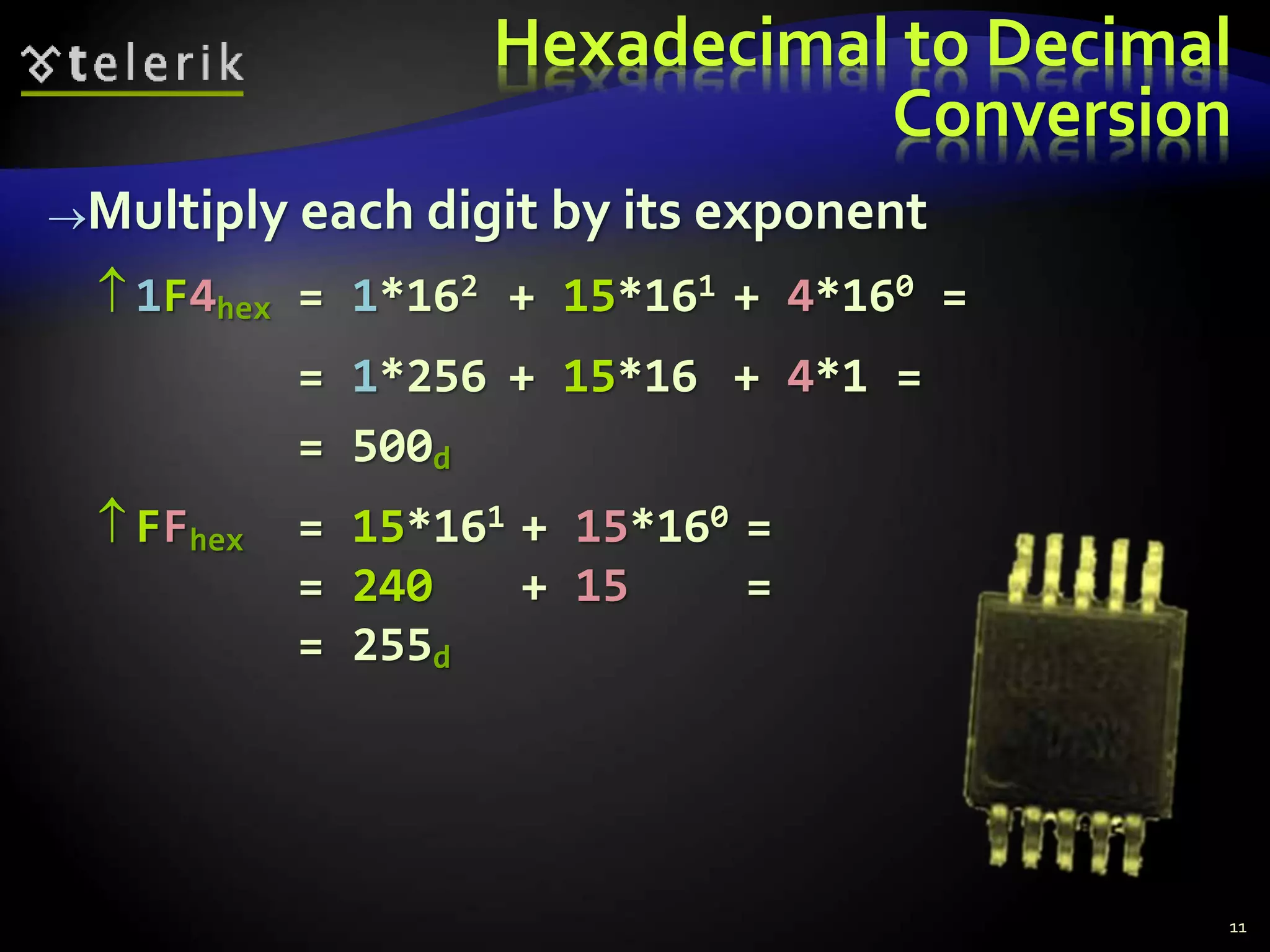
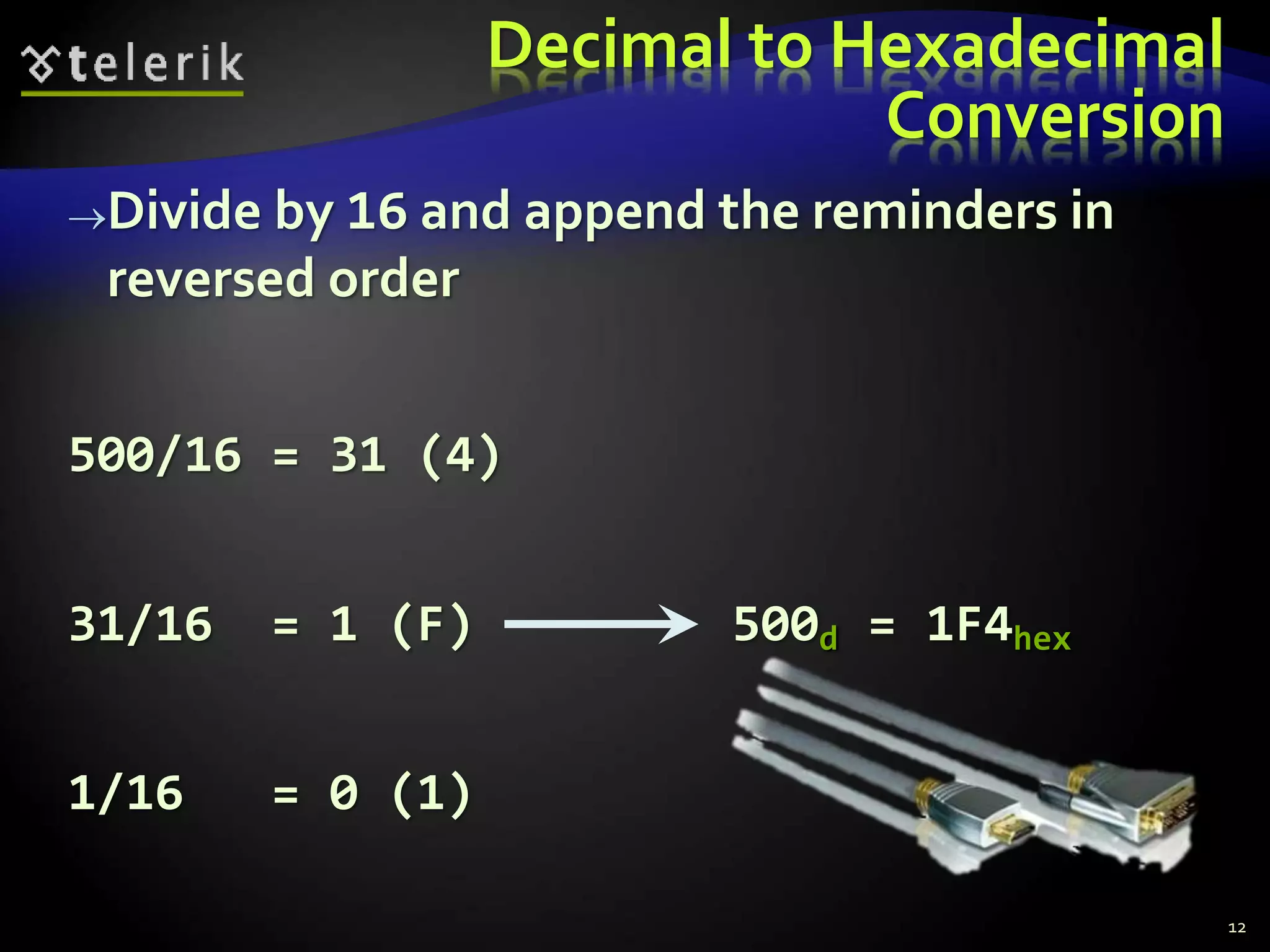
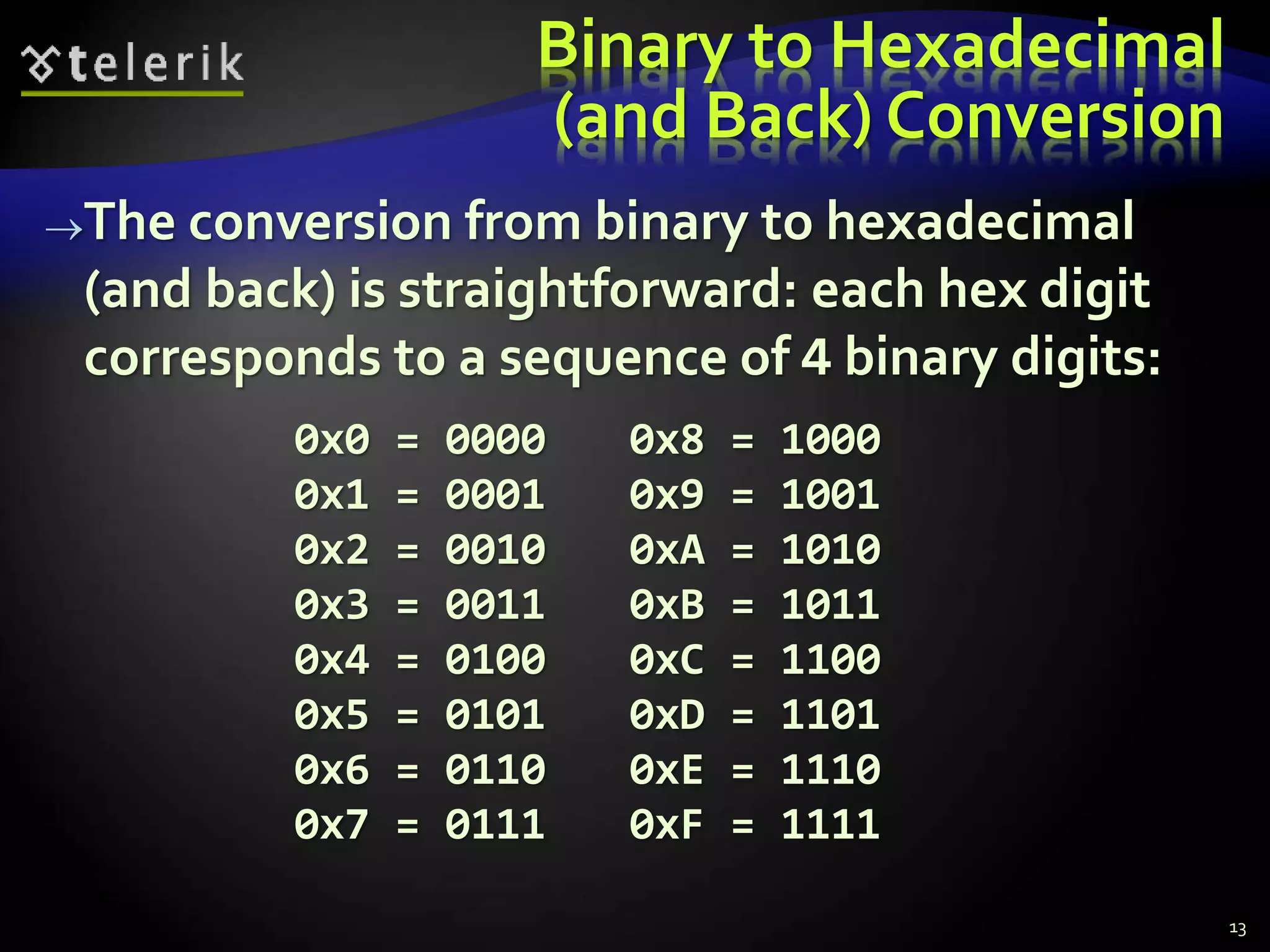
- How each system represents numbers using different bases and numerals
- Converting between the numeral systems by multiplying digits by their place value or dividing and taking remainders
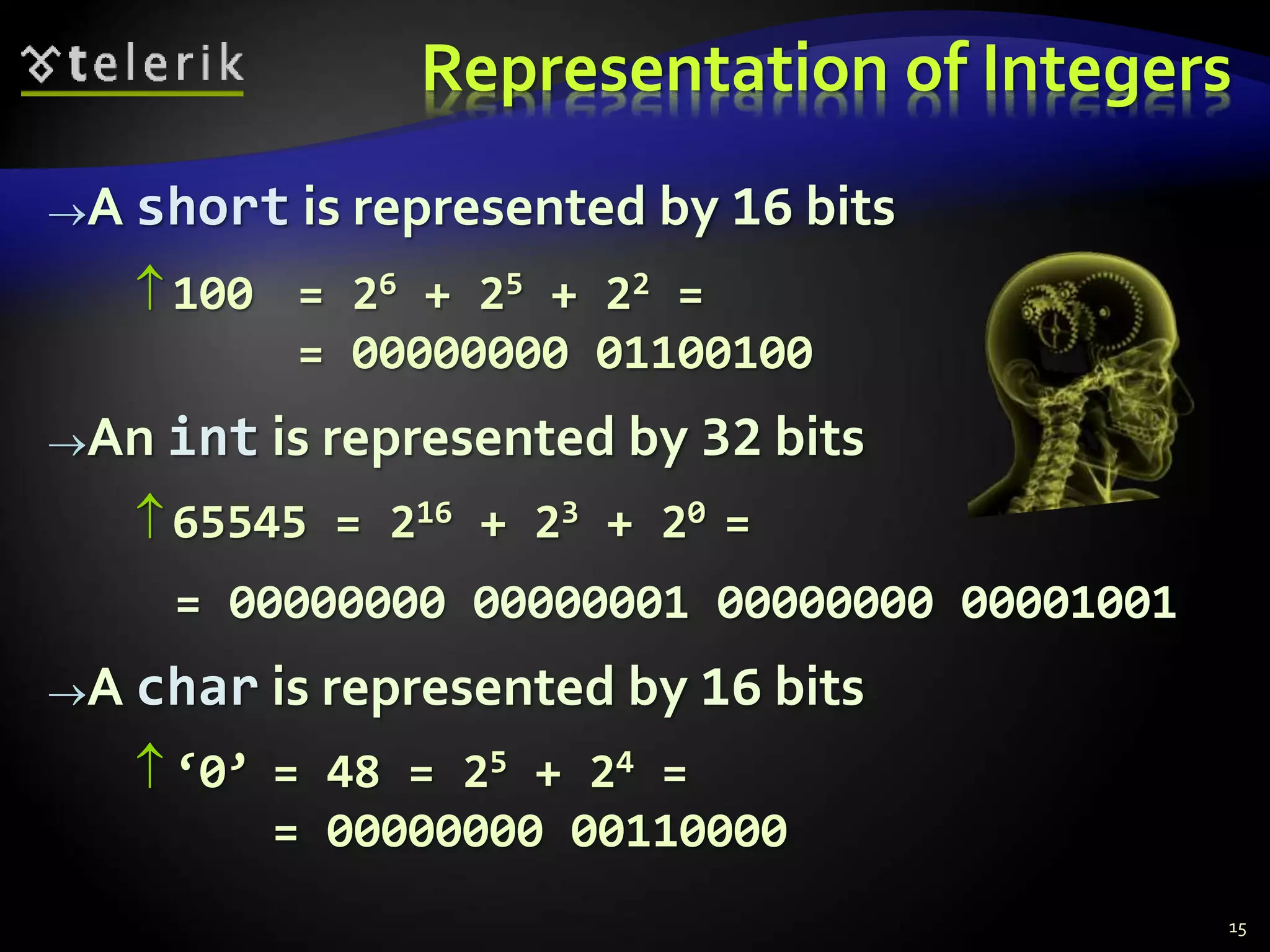
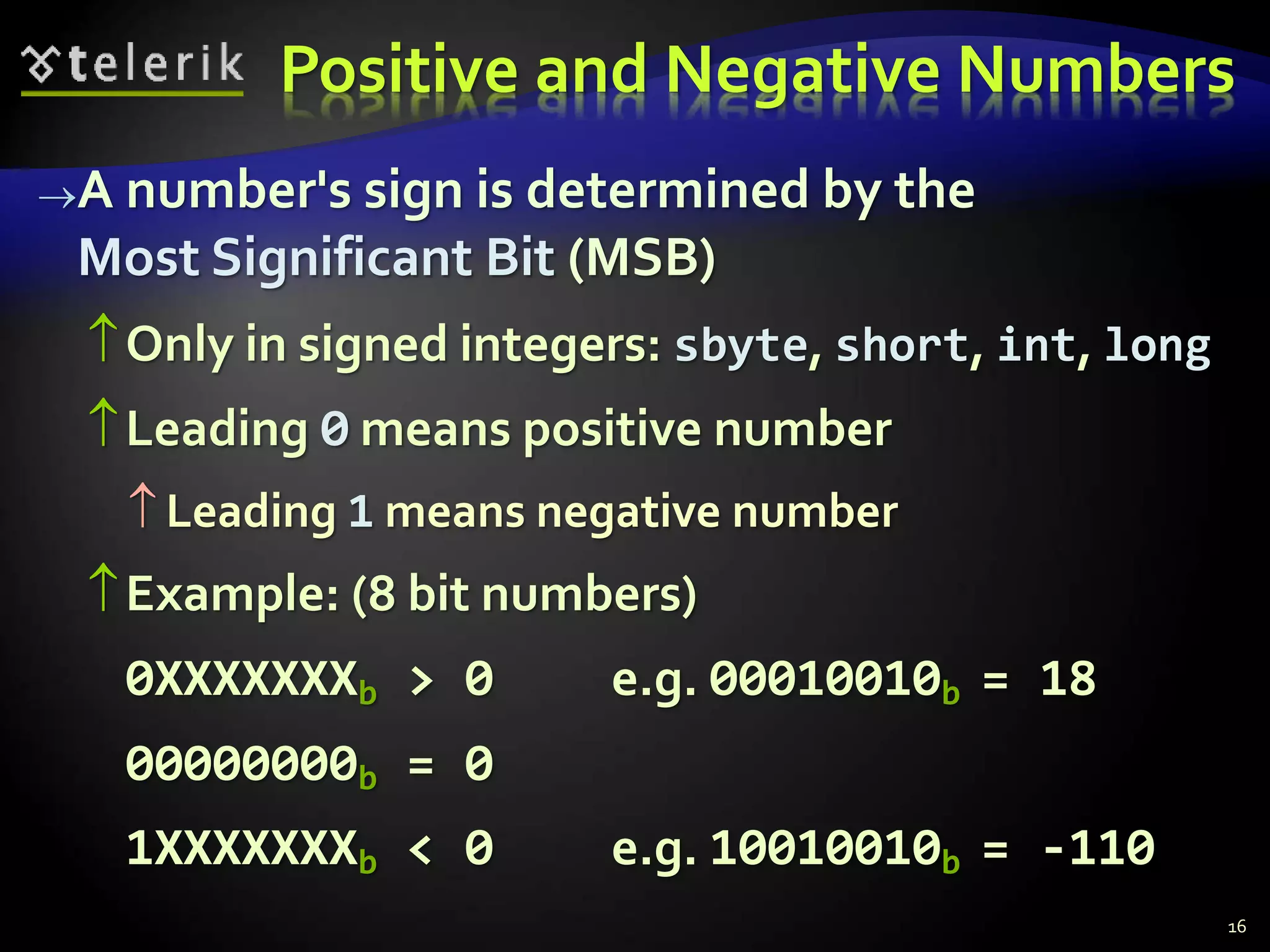
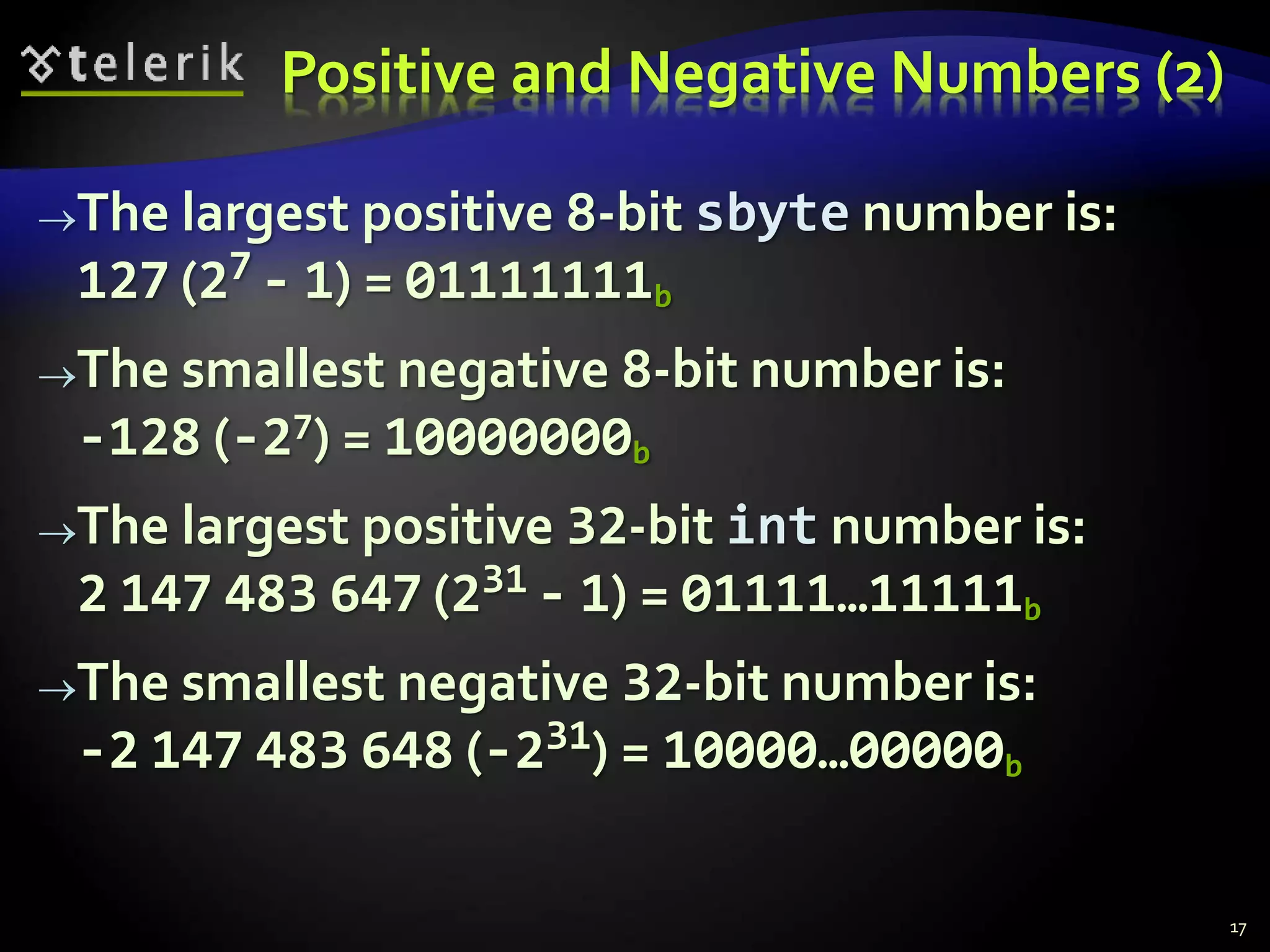
- How computers internally represent integer and floating-point numbers, including sign representation and IEEE 754 standard
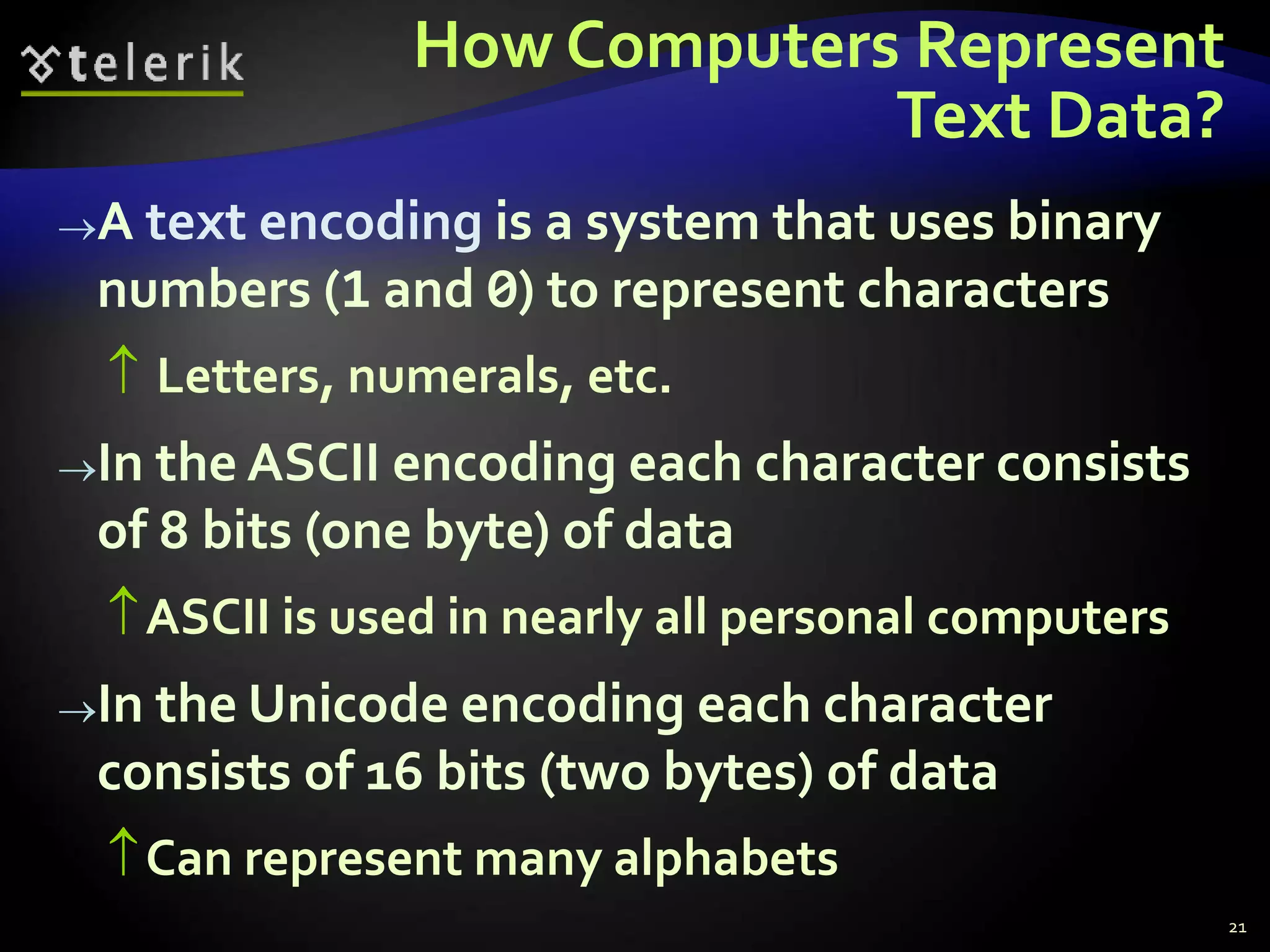
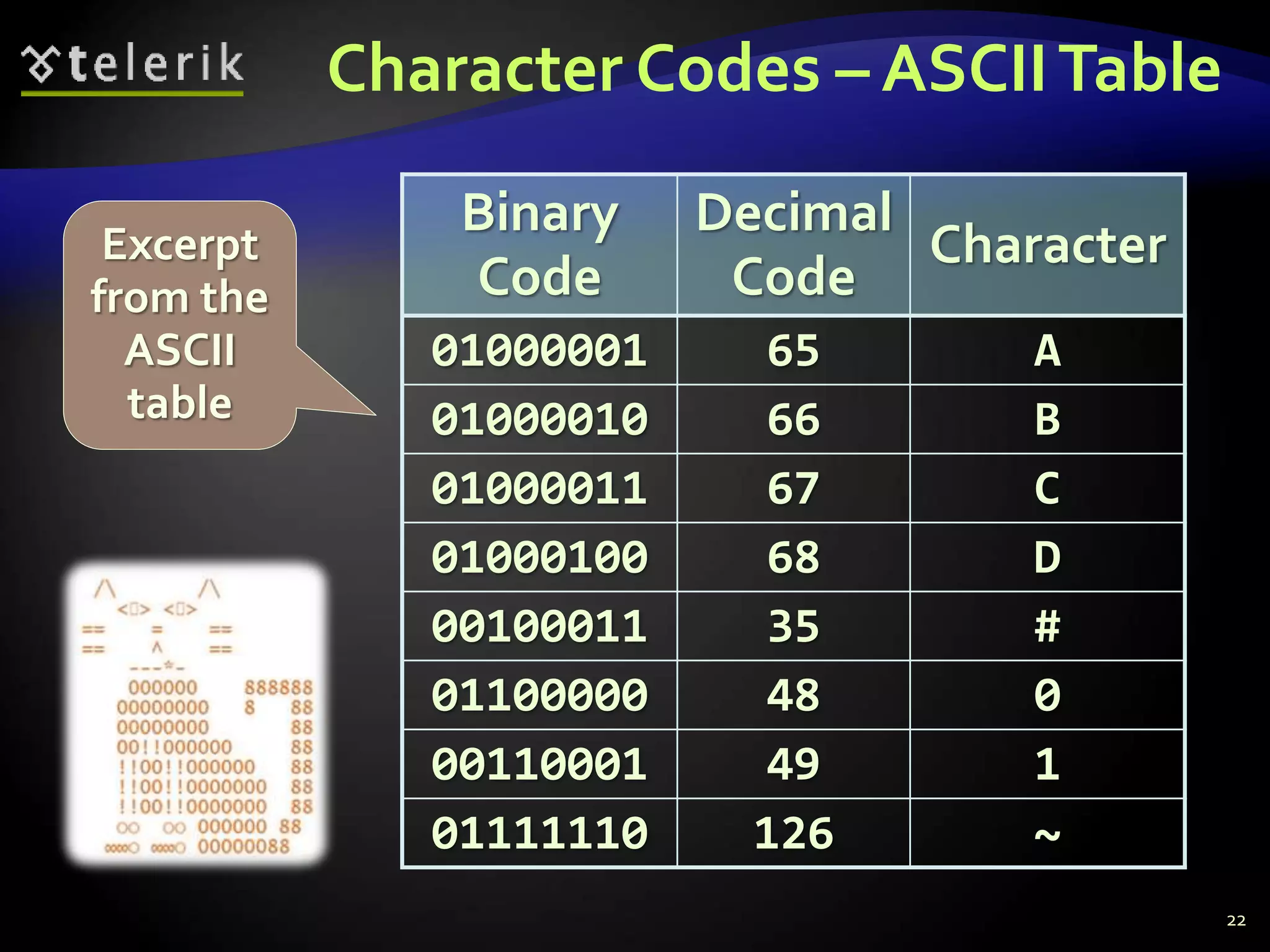
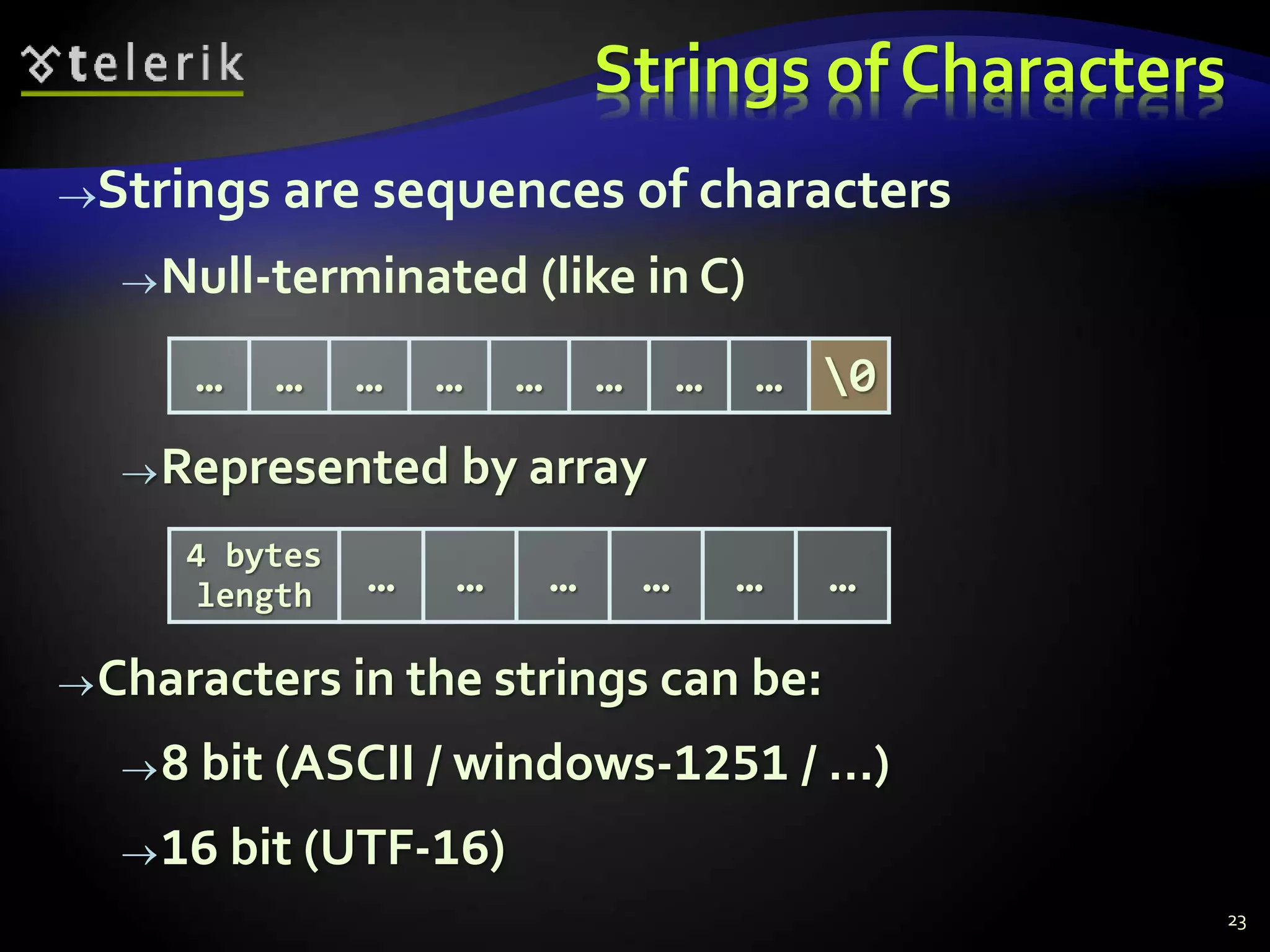
- How text is encoded using character codes like ASCII and stored as strings with null terminators
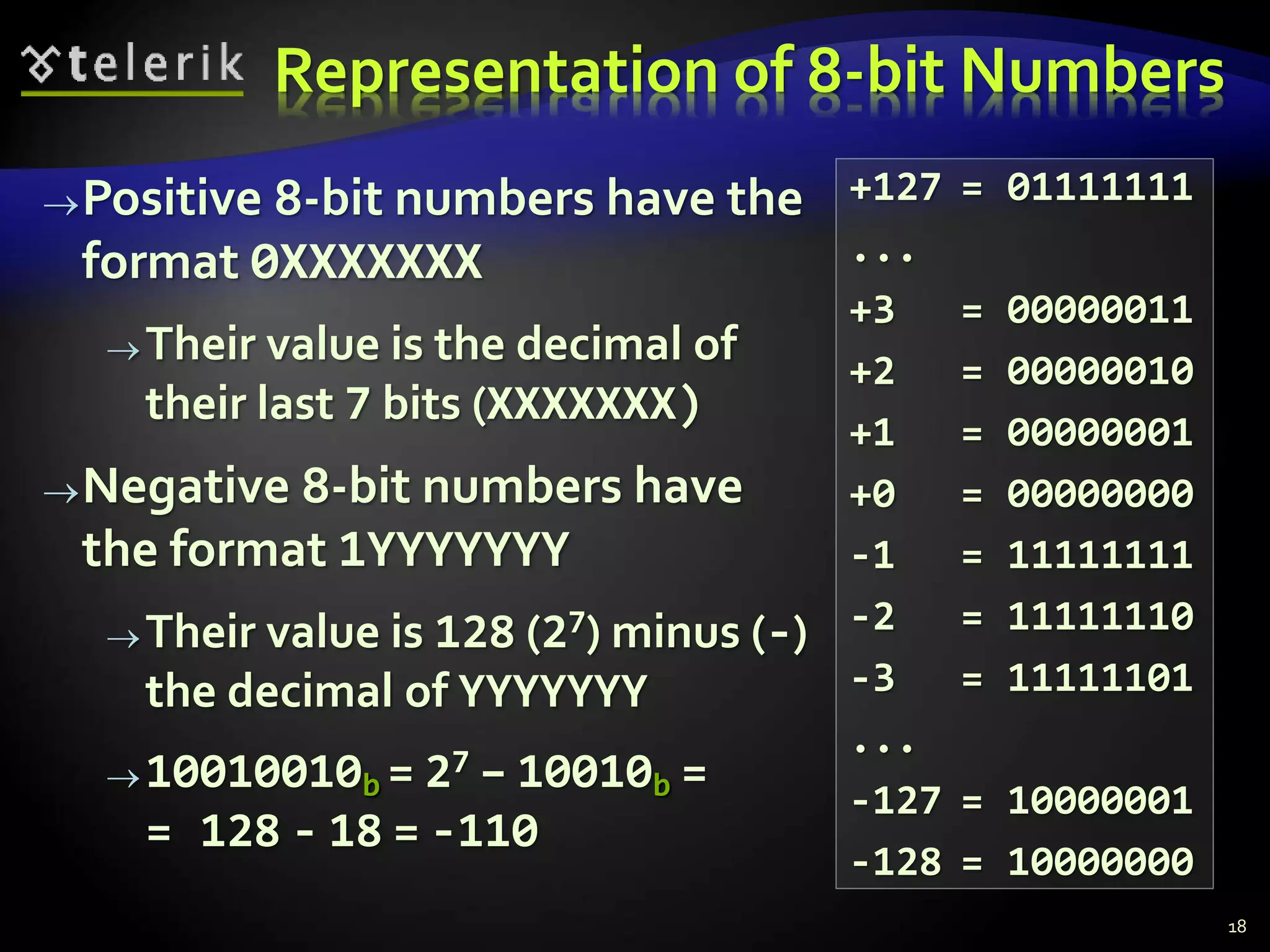
![Floating-Point Numbers
Floating-point numbers representation
(according to the IEEE 754 standard*):
Example:
19
2k-1 20 2-1 2-2 2-n
S P0 ... Pk-1 M0 M1 ... Mn-1
Sign Exponent Mantissa
1 10000011 01010010100000000000000
Mantissa = 1,322265625Exponent = 4Sign = -1
Bits [22…0]Bits [30…23]Bit 31
* See http://en.wikipedia.org/wiki/Floating_point](https://image.slidesharecdn.com/08-numeral-systems-110627100141-phpapp02-140828071650-phpapp01/75/08-Numeral-systems-19-2048.jpg)