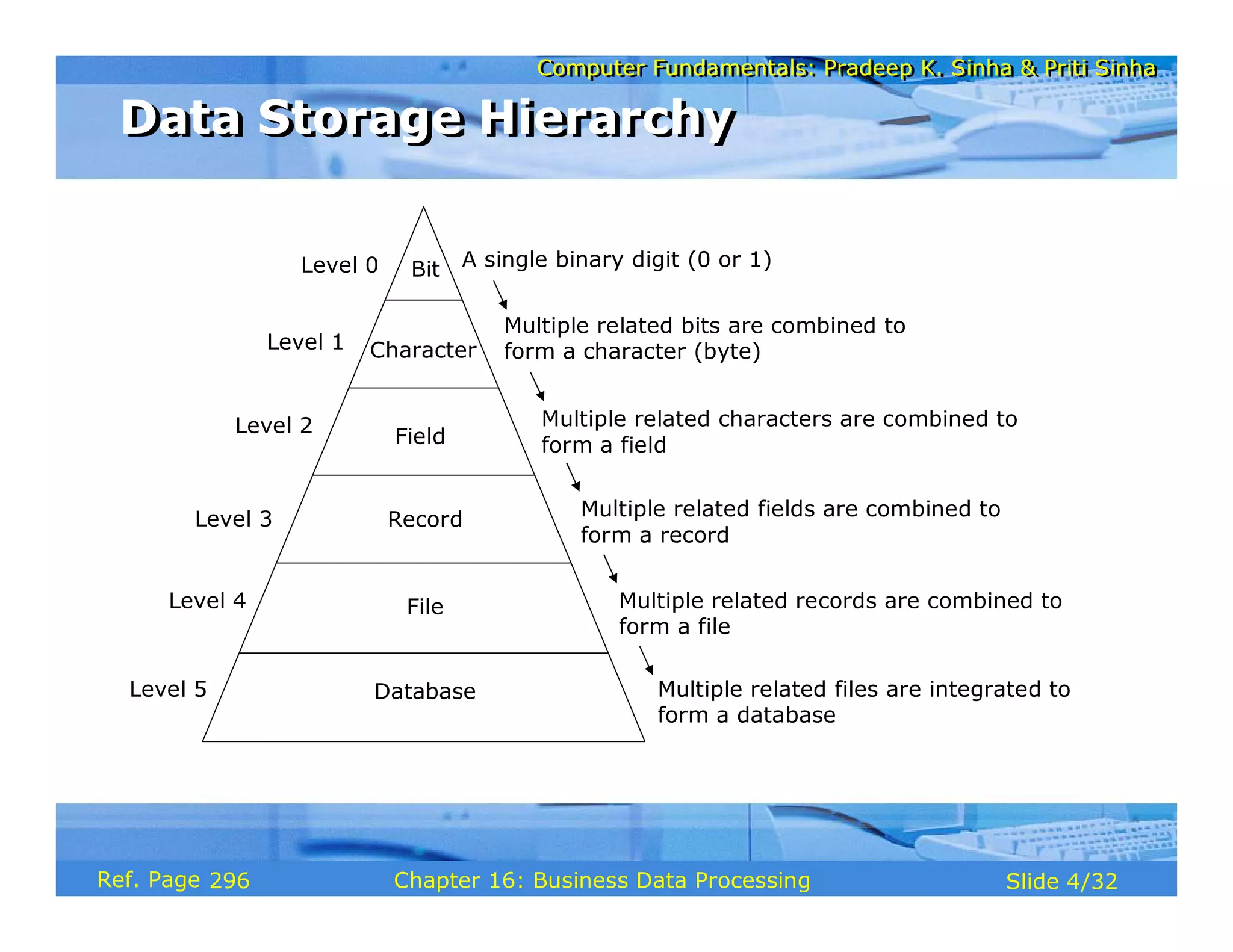
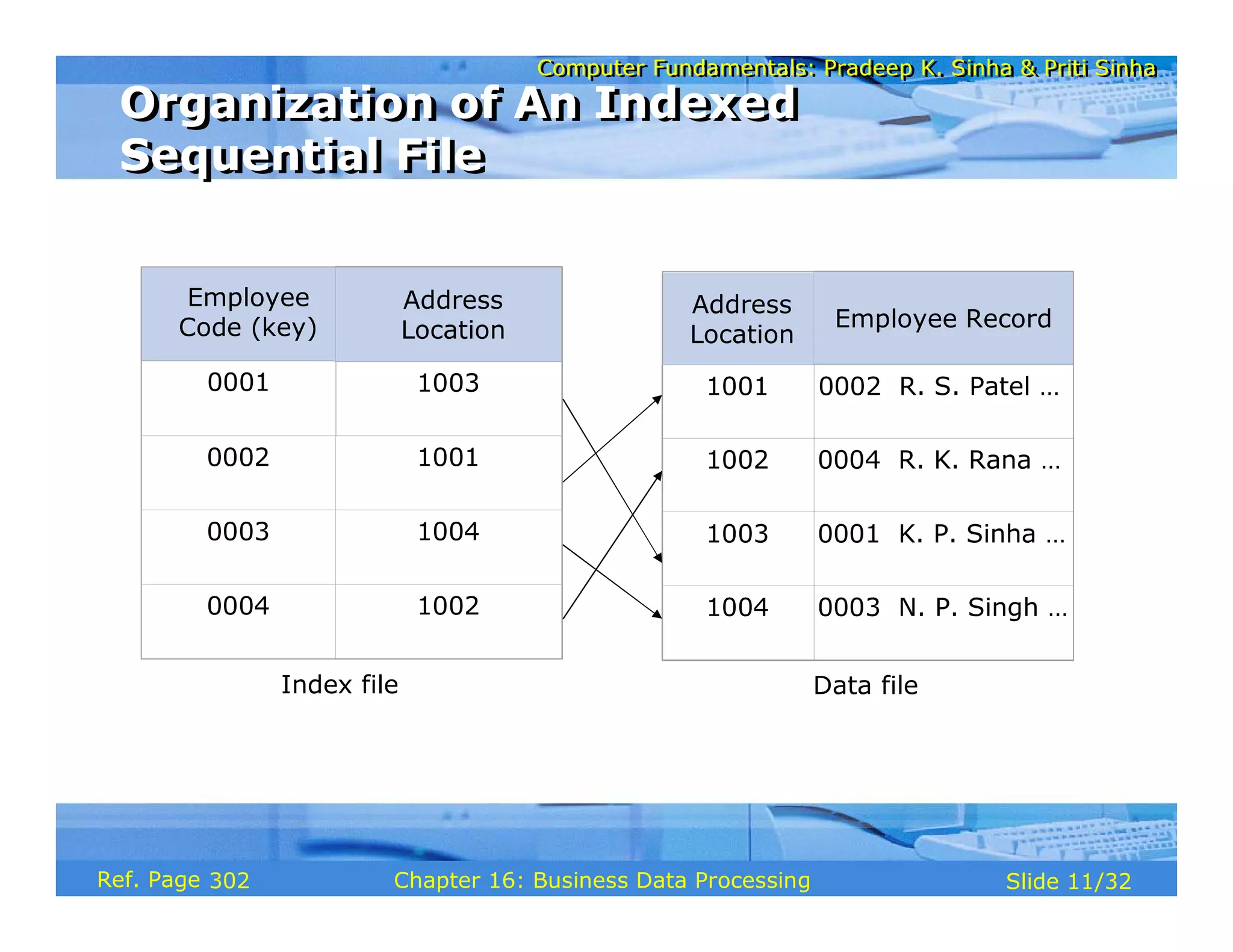
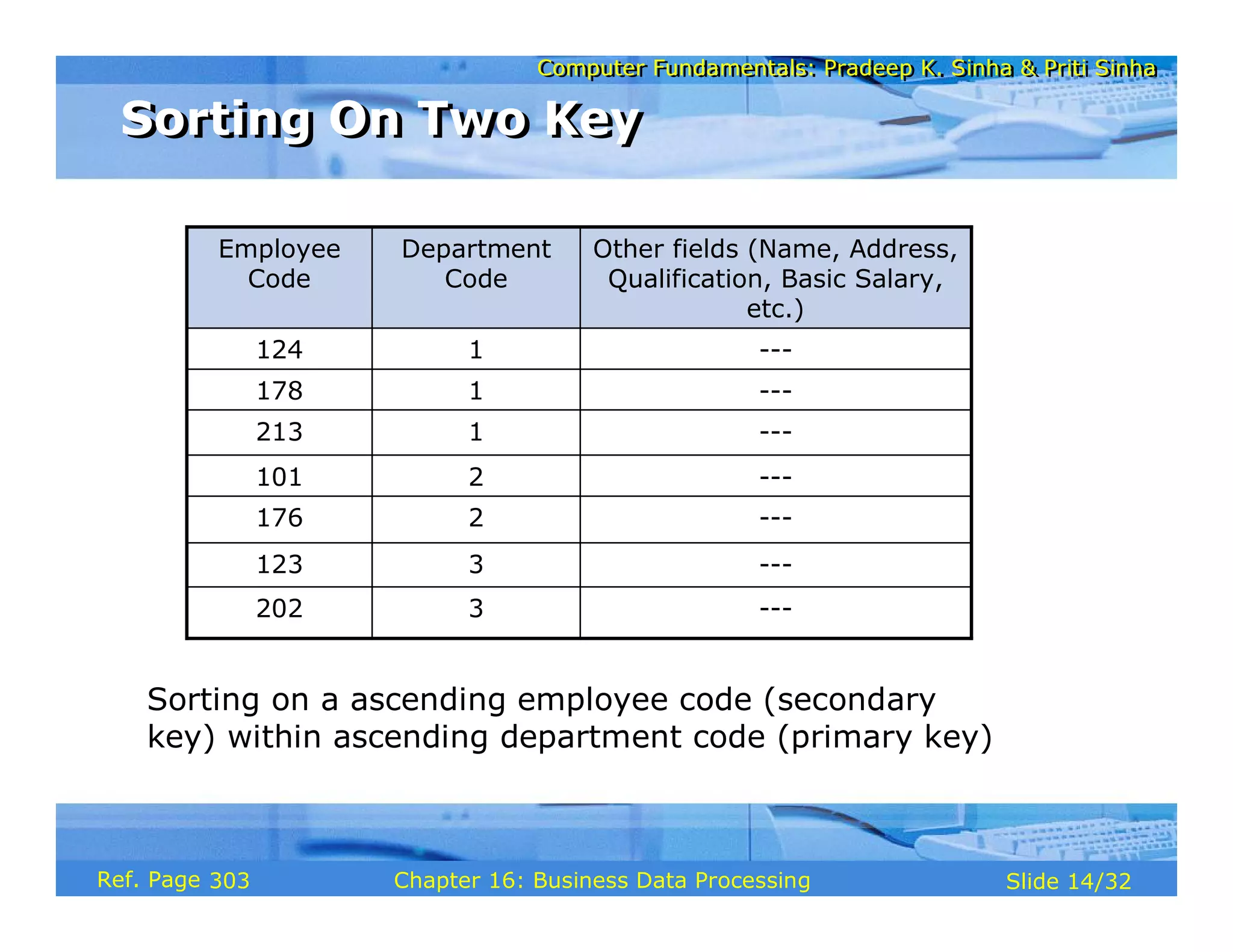
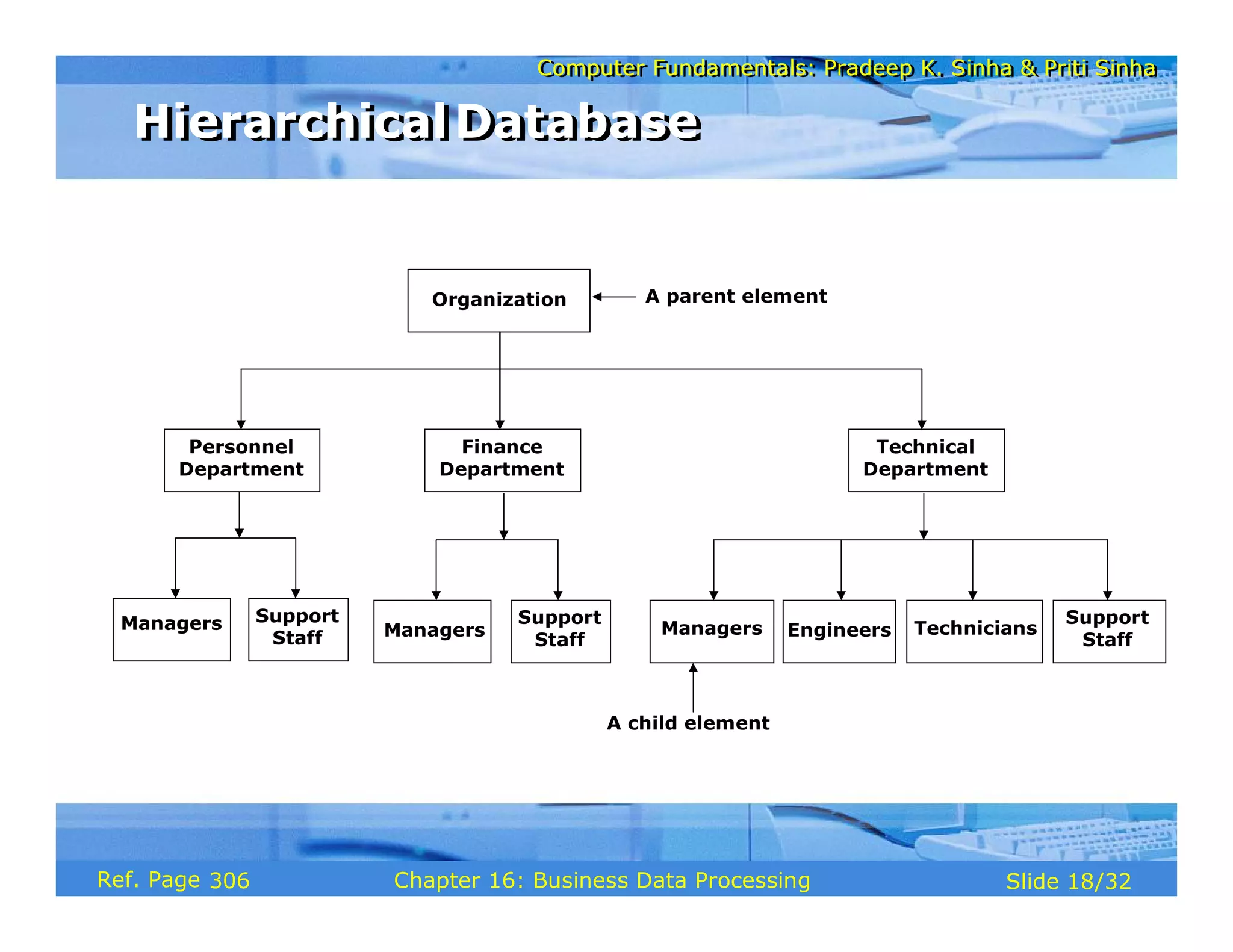
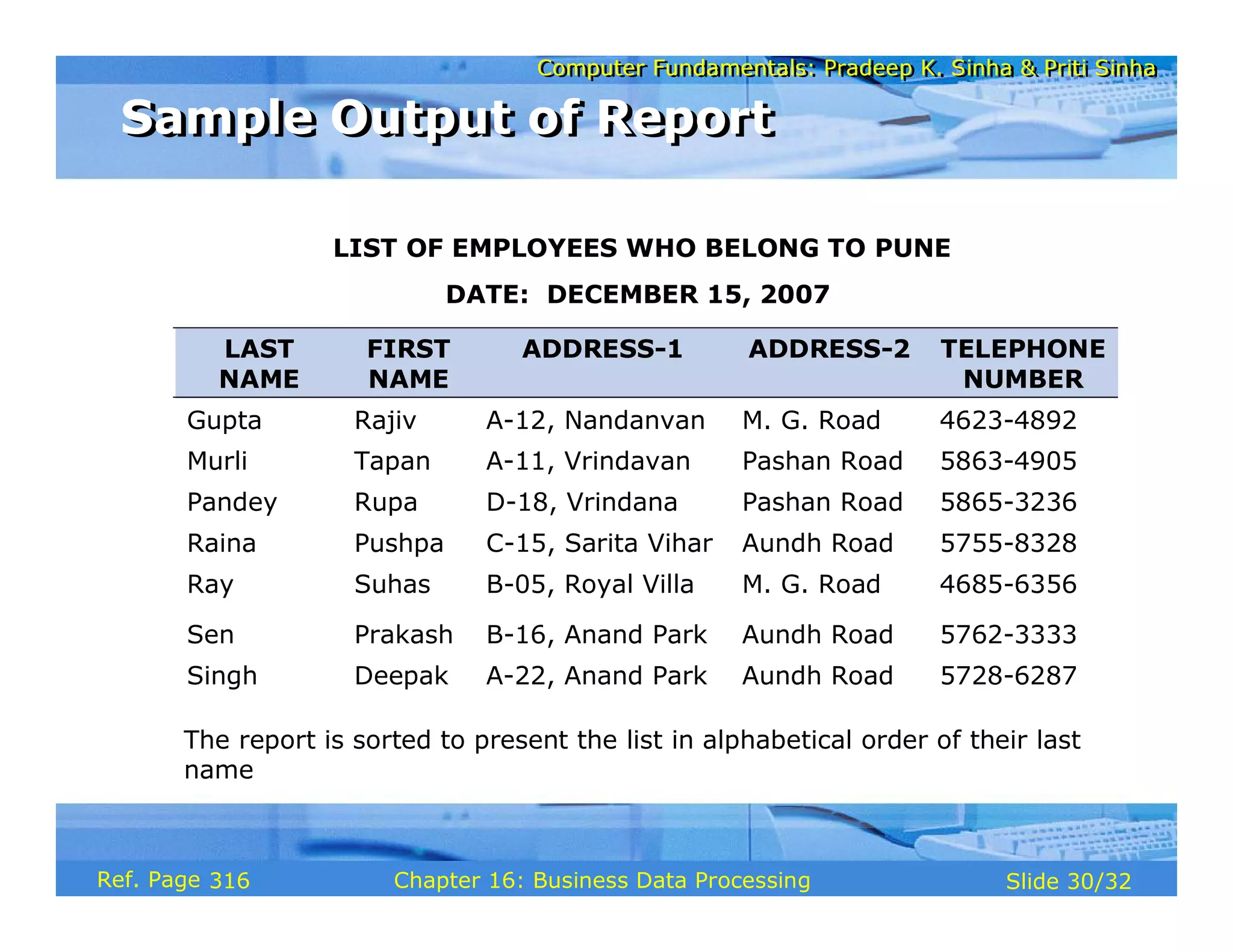
The document discusses business data processing and database systems. It describes how data is converted into useful information through data processing. It then explains the data storage hierarchy from bits to databases. Different methods for organizing data are covered, including file-oriented and database-oriented approaches. Key concepts in database systems like models, languages and components are also summarized.