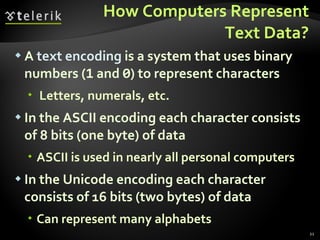
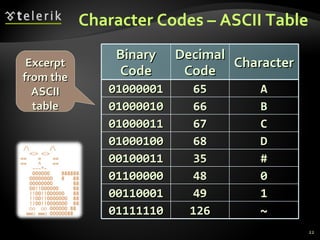
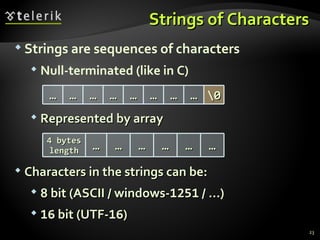
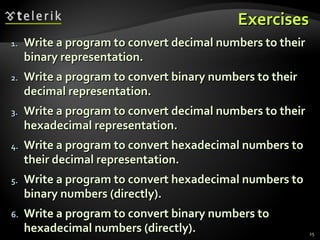
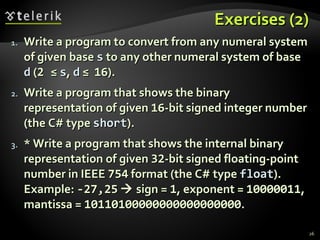
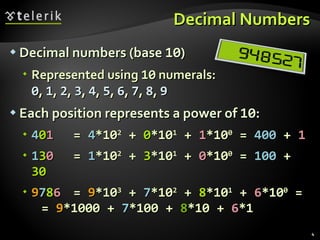
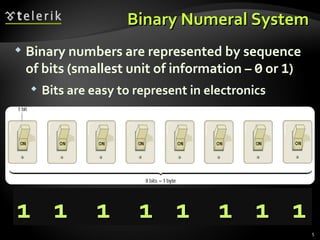
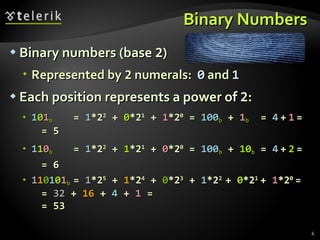
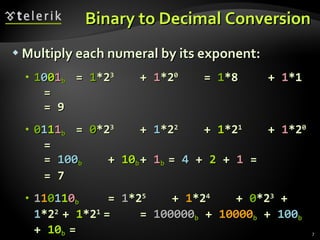
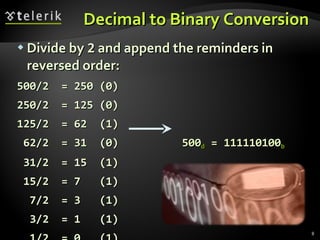
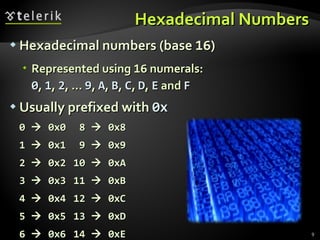
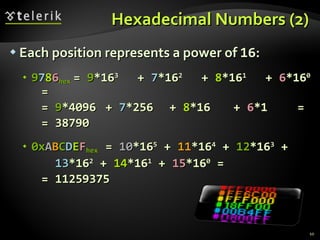
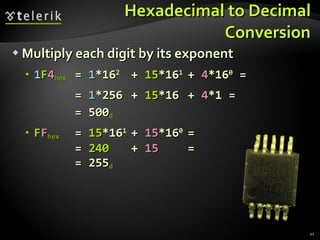
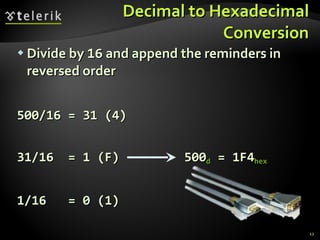
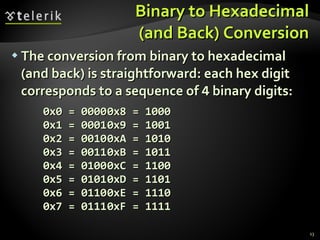
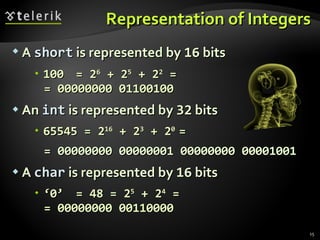
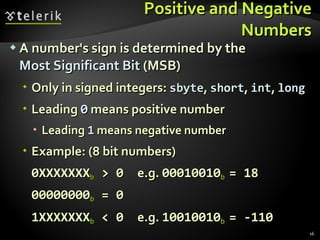
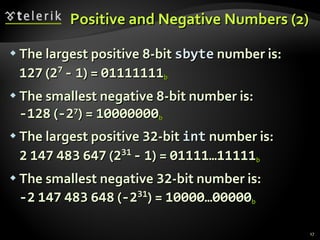
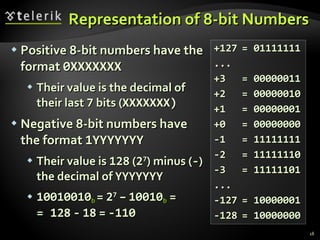
The document covers numeral systems including binary, decimal, and hexadecimal, explaining their representations, conversions, and calculations. It details how numbers are represented in computers, including positive and negative integers, and floating-point numbers per the IEEE 754 standard. Additionally, it provides exercises for programmatically converting between these numeral systems.
![Floating-Point Numbers Floating-point numbers representation (according to the IEEE 754 standard*): Example: 1 10000011 01010010100000000000000 Mantissa = 1,3222656 25 Exponent = 4 Sign = - 1 Bits [2 2 … 0 ] Bits [3 0 … 23 ] Bit 31 * See http://en.wikipedia.org/wiki/Floating_point 2 k - 1 2 0 2 - 1 2 - 2 2 - n S P 0 ... P k - 1 M 0 M 1 ... M n - 1 Sign Exponent Mantissa](https://image.slidesharecdn.com/08-numeral-systems-110627100141-phpapp02/85/08-Numeral-Systems-19-320.jpg)