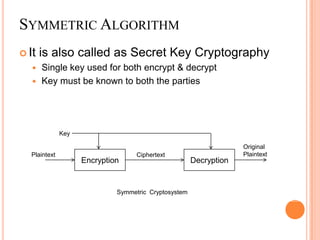
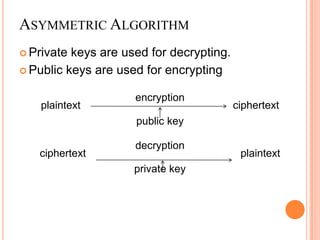
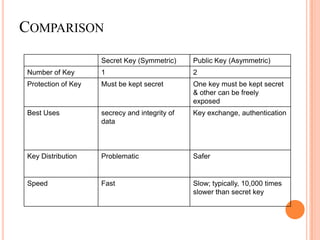
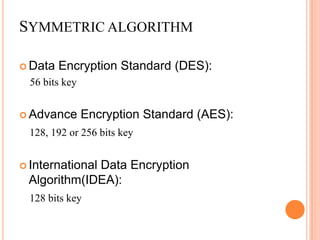
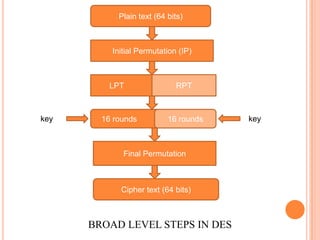
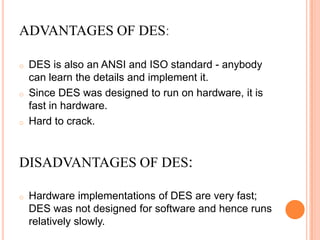
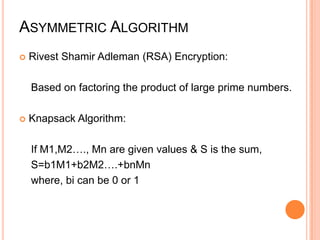
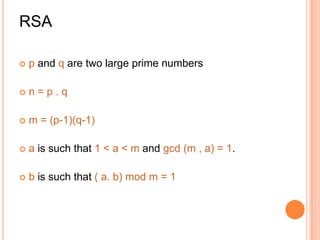
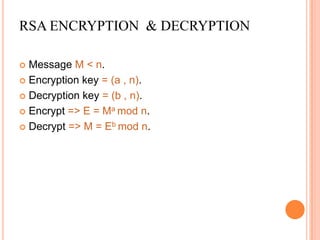
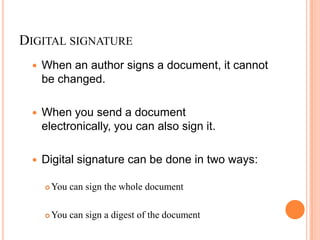
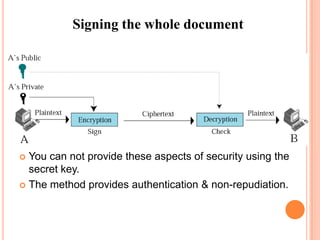
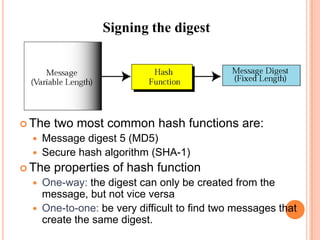
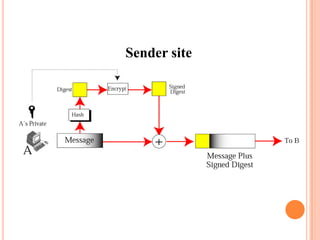
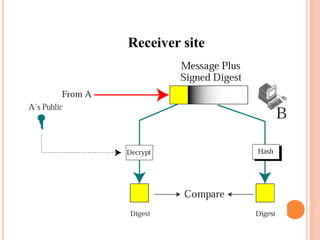
The document discusses various topics in cryptography including symmetric and asymmetric encryption algorithms. Symmetric algorithms like DES use a shared key for encryption and decryption while asymmetric algorithms like RSA use public-private key pairs. Digital signatures can be generated by encrypting a document hash with a private key and verified using the corresponding public key. Cryptography ensures security goals like confidentiality, integrity, authentication and non-repudiation of digital communications.