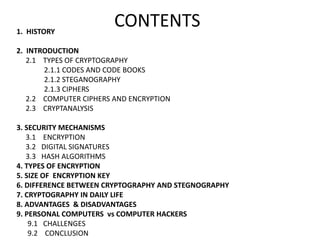
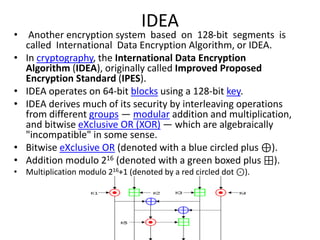
This document provides an overview of cryptography. It begins with a brief history of cryptography from ancient times to modern computer cryptography. It then defines basic concepts like encryption, decryption, plaintext and ciphertext. It describes different types of cryptography including codes, ciphers, steganography and computer ciphers. It also discusses cryptanalysis, security mechanisms like encryption, digital signatures and hash algorithms. It concludes by explaining applications of cryptography in daily life like emails and secured communication between family members.