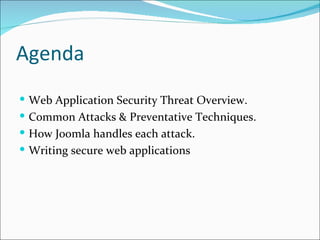
The document discusses common web application security threats like cross-site request forgery (CSRF), cross-site scripting (XSS), and SQL injections. It provides examples of each threat and explains how Joomla handles them, such as by adding tokens for CSRF protection and escaping user input. The document also covers other attacks like direct code access, register globals being on, and outlines best practices for secure web development like input sanitization and validation.




![XSS Cross Site Scripting (XSS) means executing script code (e.g. JavaScript) in a visitors browser. Conclusion: Use mosGetParam() for retrieving user input from a request, it does strip out a pretty good amount of insecure stuff. But don't rely on it, also take a good look at places where you echo out things to the webbrowser. Apply $value = htmlspecialchars( $value ); to strings before you echo them out to the browser. Note: Be carefull not to echo out any unvalidated input to a user. Code like this is dangerous for your visitors: echo $_REQUEST['value'];](https://image.slidesharecdn.com/joomlasecuritynuggets-100427042127-phpapp01/85/Joomla-security-nuggets-7-320.jpg)
![SQL Injections SQL injections make it possible for attackers to modify certain unsafe SQL queries, your script executes, in such a way that it could alter data in your database or give out sensible data to the attacker. That is because of unvalidated user input. For Example: $value = $_GET['value']; $database->setQuery( "SELECT * FROM #__mytable WHERE id = $value" ); An attacker could hand over a string like '1 OR 1', the query results in "SELECT * FROM #__mytable WHERE id = 1 OR 1" , thus returning all rows from jos_mytable. I'm not going more into detail here, as SQL injections are covered quite good on the web. Please take a look at the resources listed at the bottom of this post.](https://image.slidesharecdn.com/joomlasecuritynuggets-100427042127-phpapp01/85/Joomla-security-nuggets-8-320.jpg)

![Direct access to folders/code Instead of calling your component by http:/ /www.example.com/index.php?option=com_yourcomponent , crackers also might try to use// // http:/ /www.example.com/components/com_yourcomponent/yourcomponent.php As you can see, the PHP file will be executed directly, without Joomla! as a wrapper around it. Now, if your file only contains some classes or functions, but does not execute any code, there is nothing wrong about that: <?php class myClass { [SomeFunctionsHere] } function myFunction() {[SomeCodeHere] } ?> Conclusion: To make your component secure against direct access, insert this code line into the beginning of every PHP file that executes code: // no direct access defined( '_VALID_MOS' ) or die( 'Restricted access' ); // no direct access defined('_JEXEC') or die('Restricted access');](https://image.slidesharecdn.com/joomlasecuritynuggets-100427042127-phpapp01/85/Joomla-security-nuggets-10-320.jpg)