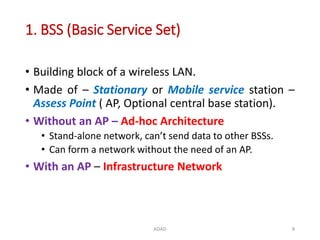
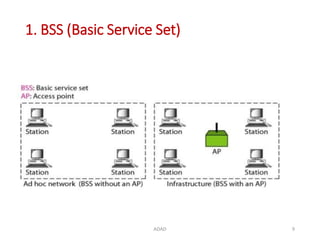
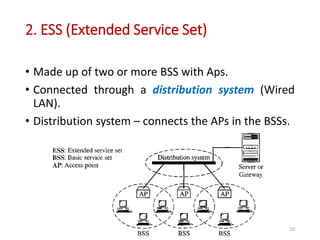
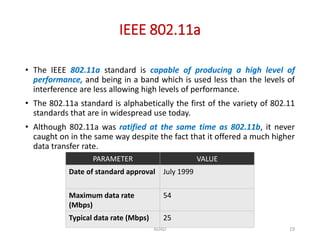
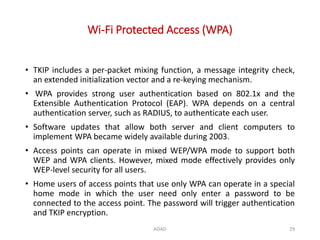
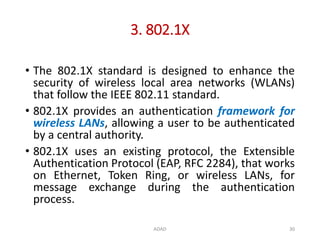
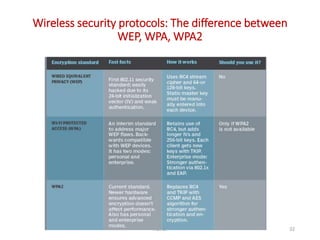
The document provides an overview of wireless networking, including its technology, benefits, types, components, and standards. It discusses the IEEE 802.11 standards for wireless LANs, detailing the specifications and performance characteristics of 802.11a, 802.11b, and 802.11g. Additionally, it covers various wireless security protocols, such as WEP, WPA, and 802.1x, outlining their functions and security features.