WIMAX Network Dimensioning Course
•
2 likes•574 views
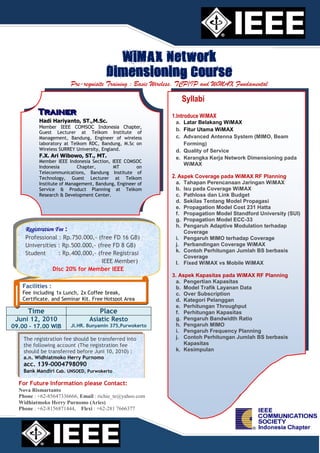
WiMAX Network Dimensioning Course will be held on Purwokerto, 12 June 2010
Report
Share
Report
Share
Download to read offline
Recommended
Microstrip-Fed Monopole Antenna Design)

A novel internal printed monopole antenna for modern mobile devices, which has a compact size, lightweight, low cost, wide impedance bandwidth, and omnidirectional radiation pattern, is proposed in this thesis.
Singlemode vs Multimode Fiber Optic Cable

One of the most desirable transmission medium in a data center environment is the fiber optic cable due to a series of advantages regarding the bandwidth capacity, distance run, immunity to interferences, and security of communication. The general structure of a fiber optic cable.
Mimo ofdm in cellular sysytem

To learn the MIMO OFDM system model and to overcome from the drawback of this system the future work on 4G and 5G scope.
Recommended
Microstrip-Fed Monopole Antenna Design)

A novel internal printed monopole antenna for modern mobile devices, which has a compact size, lightweight, low cost, wide impedance bandwidth, and omnidirectional radiation pattern, is proposed in this thesis.
Singlemode vs Multimode Fiber Optic Cable

One of the most desirable transmission medium in a data center environment is the fiber optic cable due to a series of advantages regarding the bandwidth capacity, distance run, immunity to interferences, and security of communication. The general structure of a fiber optic cable.
Mimo ofdm in cellular sysytem

To learn the MIMO OFDM system model and to overcome from the drawback of this system the future work on 4G and 5G scope.
Massive MIMO: Opportunities & Challenges

An overview of Massive MIMO technology and it's scope for the next generations of wireless communications. Presented at a seminar in Ulm University in the department of Communications Engineering.
Digital Signal Processing Techniques for High-Speed Optical Communications Links

Dario Pilori PhD defense - PhD program in Electrical Electronic and Communications Engineering @ Politecnico di Torino, Italy - 22 March 2019
Optical fiber Communication training report

This is the complete report of my summer training done in optical fiber installation and technician. You will find all the stuff related to optical fiber installation.
MIMO-OFDM SYSTEM IN RAYLEIGH FADDING CHANNEL

MIMO-OFDM (Multi Input Multi Output- Orthogonal Frequency Division Multiplexing) system is very popular technique for mobile communication. We found that Ergodic channel capacity has some limitation in MIMO-OFDM system. So Ergodic channel capacity optimization is necessary to improve the performance of MIMO-OFDM System.
Questions about Understanding benefits of mimo technology (article)

Questions about Understanding benefits of mimo technology (article)
Massive information on Massive MIMO

All of us have lofty expectations for 5G wireless technology.
Massive growth in demand for mobile data...
Massive growth in the number of connected devices...
Massive change in data transfer rates and latency...
Massive explosion in the diversity of mobile applications...
Massive....Massive....Massive....this word is frequently used like never before.
Delivering all these expectations depends on the evolution of existing technologies and revolution in new technologies.
One such revolutionary change is the use of massive multiple-input/multiple-output (MIMO) antenna systems in 5G for different frequency ranges.
Interested to understand and learn what mMIMO means?!
If yes, here is some massive theoretical information on Massive MIMO.
Doubly-Massive MIMO Systems at mmWave Frequencies: Opportunities and Research...

Keynote talk delivered at the IEEE WCNC'2016 Workshop on Green and Sustainable Wireless Networks (GRASNET), Doha, Qatar, April 3, 2016
More Related Content
What's hot
Massive MIMO: Opportunities & Challenges

An overview of Massive MIMO technology and it's scope for the next generations of wireless communications. Presented at a seminar in Ulm University in the department of Communications Engineering.
Digital Signal Processing Techniques for High-Speed Optical Communications Links

Dario Pilori PhD defense - PhD program in Electrical Electronic and Communications Engineering @ Politecnico di Torino, Italy - 22 March 2019
Optical fiber Communication training report

This is the complete report of my summer training done in optical fiber installation and technician. You will find all the stuff related to optical fiber installation.
MIMO-OFDM SYSTEM IN RAYLEIGH FADDING CHANNEL

MIMO-OFDM (Multi Input Multi Output- Orthogonal Frequency Division Multiplexing) system is very popular technique for mobile communication. We found that Ergodic channel capacity has some limitation in MIMO-OFDM system. So Ergodic channel capacity optimization is necessary to improve the performance of MIMO-OFDM System.
Questions about Understanding benefits of mimo technology (article)

Questions about Understanding benefits of mimo technology (article)
Massive information on Massive MIMO

All of us have lofty expectations for 5G wireless technology.
Massive growth in demand for mobile data...
Massive growth in the number of connected devices...
Massive change in data transfer rates and latency...
Massive explosion in the diversity of mobile applications...
Massive....Massive....Massive....this word is frequently used like never before.
Delivering all these expectations depends on the evolution of existing technologies and revolution in new technologies.
One such revolutionary change is the use of massive multiple-input/multiple-output (MIMO) antenna systems in 5G for different frequency ranges.
Interested to understand and learn what mMIMO means?!
If yes, here is some massive theoretical information on Massive MIMO.
Doubly-Massive MIMO Systems at mmWave Frequencies: Opportunities and Research...

Keynote talk delivered at the IEEE WCNC'2016 Workshop on Green and Sustainable Wireless Networks (GRASNET), Doha, Qatar, April 3, 2016
What's hot (18)
Digital Signal Processing Techniques for High-Speed Optical Communications Links

Digital Signal Processing Techniques for High-Speed Optical Communications Links
Questions about Understanding benefits of mimo technology (article)

Questions about Understanding benefits of mimo technology (article)
The Capacity Limit of Single-Mode Fibers and Technologies Enabling High Capac...

The Capacity Limit of Single-Mode Fibers and Technologies Enabling High Capac...
Doubly-Massive MIMO Systems at mmWave Frequencies: Opportunities and Research...

Doubly-Massive MIMO Systems at mmWave Frequencies: Opportunities and Research...
Expanding the Boundaries of Optical Communications

Expanding the Boundaries of Optical Communications
Viewers also liked
Nghiên cứu cơ chế routing của Cisco, mô phỏng trên nền GNS3

Nghiên cứu cơ chế routing của Cisco, mô phỏng trên nền GNS3
Viewers also liked (7)
Nghiên cứu cơ chế routing của Cisco, mô phỏng trên nền GNS3

Nghiên cứu cơ chế routing của Cisco, mô phỏng trên nền GNS3
Báo cáo cuối kỳ - đề tài "nghiên cứu cơ chế routing của cisco mô phỏng trên ...

Báo cáo cuối kỳ - đề tài "nghiên cứu cơ chế routing của cisco mô phỏng trên ...
Similar to WIMAX Network Dimensioning Course
Thesis on Wimax

The relay stations are widely used in major wireless technologies such as WiMAX (Worldwide Interoperability for Microwave Access) and LTE (Long term evolution) which provide cost effective service to the operators and end users. It is quite challenging to provide guaranteed Quality of Service (QoS) in WiMAX networks in cost effective manner.
IRJET- Different Technique over 5G LTE Wireless Network: A Survey

https://irjet.net/archives/V7/i2/IRJET-V7I2229.pdf
Deep Learning for 5G Innovation Insights from Patents

Patents are a good information resource for obtaining the state of the art of deep learning for 5G wireless telecommunications technology innovation insights.
I.Deep Learning for 5G Technology Innovation Status
Patents that specifically describe the major deep learning applications in 5G are a good indicator of the deep learning for 5G innovations in a specific innovation entity. To find the deep learning for 5G technology innovation status, patent applications in the USPTO as of June 5, 2020 that specifically describe the major deep learning applications in 5G are searched and reviewed. 24 published patent applications that are related to the key deep learning for 5G technology innovation are selected for detail analysis.
II. Deep Learning for 5G Technology Innovation Details
Patent information can provide many valuable insights that can be exploited for developing and implementing new technologies. Patents can also be exploited to identify new product/service development opportunities.
MIMO Adaptive Antenna/Samsung Electronics
MIMO Communication Channel/ Parallel Wireless
Radio Access Network (RAN)/Beijing University of Posts and Telecommunications
Wireless communication and Network 

Email: chanaka.lasantha@gmail.com
Social : https://www.linkedin.com/in/chanaka-lasantha-nanayakkara-220615a0/
Efficiency and effectiveness video on demand over worldwide interoperability ...

(WiMAX) is another solution for readiness broadband networks inside the region, covered or not, by alternative technologies like (ADSL) or cable through this paper by deploying many mobility patterns such as static, random and path for Video on Demand (VoD) over (WiMAX) Network. The performance of varied (QPSK) and (QAM) modulation techniques, by applying the (OPNET) simulator version 17.5. This work is finished in terms of the transmitted traffic and received traffic. Simulation result indicates that once nodes are moving by (SVC) code schema in (WiMAX). The result is an effective and attainable overall performance of (QPSK) which is better than (QAM) modulation technique.
Ew31992997

IJERA (International journal of Engineering Research and Applications) is International online, ... peer reviewed journal. For more detail or submit your article, please visit www.ijera.com
IRJET- Analysis of 5G Mobile Technologies and DDOS Defense

https://www.irjet.net/archives/V6/i6/IRJET-V6I6605.pdf
Performance comparison of Wireless IEEE 802.11 a, b, g and n used for Ad-Hoc ...

Performance comparison of Wireless IEEE 802.11 a, b, g and n used for Ad-Hoc ...IJCSIS Research Publications
This paper presents a comparative study of IEEE 802.11 a/b/g/n wireless LAN standards in an ELearning classroom network using adhoc networks as communication support. The evaluation is performed through a series of scenarios schematizing communication between students and practitioners in an educational context. The first objective is to plan the physical layer via the choice of the suitable transmission standard that satisfy the implementation specifications. Given the real-time traffic considered, a good traffic transmission must be ensured.IRJET- Isolation Enhancement of Miniaturized Mimo Antenna with Slotted Gr...

https://www.irjet.net/archives/V6/i4/IRJET-V6I4828.pdf
IRJET- Synthesis and Simulation for MIMO Antennas with Two Port for Wide Band...

https://www.irjet.net/archives/V6/i4/IRJET-V6I4778.pdf
A Novel Resource Allocation Method For Multicasting Network Using Call Admiss...

Abstract— WiMAX relay networks make resource allocation decisions once per frame. An IEEE 802.16j frame consists of a downlink sub frame and an uplink sub frame. This study focuses on the downlink multicast problems. The downlink sub frame can be divided into an access zone and a relay zone. In the access zone, the BS transmits the video data to its served RSs and SSs. In the relay zone, the RSs further relay the video data to their served SSs. To determine the data transmissions within each frame, the BS should make a scheduling decision at the beginning of each frame using an appropriate resource allocation scheme. WiMAX is generally used to reduce the delays and packet loss. It a wireless standard designed to provide data transfer. In this paper mainly focuses on implementing BGWA based algorithm in order to avoid unwanted intrusion occurrences in handoff time. The Mobile Motion Prediction algorithm generally keeps track of the positions of the mobile stations and their relevant connections. The task of motion prediction is to track the motion of the mobile station in different gateways. Then different prediction methods are applied according to the sensitivity of the range to gain high precision. CAC Approach can be used to the worldwide interoperability for microwave access (WiMAX) is a promising technology for last-mile Internet access, particularly in the areas where wired infrastructures are not available. Mainly this approach is used to transmitting the video/Audio sending from base station to relay station with transmitting or secretes code.
Similar to WIMAX Network Dimensioning Course (20)
Wireless Presentation for UT in Silicon Valley 2013

Wireless Presentation for UT in Silicon Valley 2013
IRJET- Different Technique over 5G LTE Wireless Network: A Survey

IRJET- Different Technique over 5G LTE Wireless Network: A Survey
Deep Learning for 5G Innovation Insights from Patents

Deep Learning for 5G Innovation Insights from Patents
Efficiency and effectiveness video on demand over worldwide interoperability ...

Efficiency and effectiveness video on demand over worldwide interoperability ...
IRJET- Analysis of 5G Mobile Technologies and DDOS Defense

IRJET- Analysis of 5G Mobile Technologies and DDOS Defense
Performance comparison of Wireless IEEE 802.11 a, b, g and n used for Ad-Hoc ...

Performance comparison of Wireless IEEE 802.11 a, b, g and n used for Ad-Hoc ...
IRJET- Isolation Enhancement of Miniaturized Mimo Antenna with Slotted Gr...

IRJET- Isolation Enhancement of Miniaturized Mimo Antenna with Slotted Gr...
IRJET- Synthesis and Simulation for MIMO Antennas with Two Port for Wide Band...

IRJET- Synthesis and Simulation for MIMO Antennas with Two Port for Wide Band...
A Novel Resource Allocation Method For Multicasting Network Using Call Admiss...

A Novel Resource Allocation Method For Multicasting Network Using Call Admiss...
More from Arief Gunawan
Metaverse - Let's learn to understand when business becomes virtual and when ...

https://www.youtube.com/watch?v=G1GsJPqRCww
This session will dissect the main architecture of the Metaverse. This will provide enlightenment for participants to understand when business becomes virtual and when virtual becomes business. This session will begin to discuss the transition to the Metaverse, how the Metaverse world itself is, and how business is in the Metaverse.
Technology Disruptions

Technology Disruptions that Change Our Behavior, Universitas Pelita Harapan, 26 Februari 2021
https://www.youtube.com/watch?v=7JWcRCQn6aA&t=1s
APWiMob 2014 (Bali, 28-30 August 2014) CFP

About APWiMob
APWiMob is international event in Asia Pacific designed for audience working in the wireless communications and mobile technology communities. As the Asia Pacific conference focusing on wireless and mobile technologies, APWiMob is very suitable for wireless communications researchers, industry professionals, and academics interested in the latest development and design of wireless systems and mobile technologies.
Sponsored by the IEEE Communications Society Indonesia Chapter, APWiMob has a strong foundation of bringing together industry and academia. In 2014, Bali will become the wireless foundation by hosting APWiMob 2014. The conference will include technical sessions, tutorials, and technology and business panels. You are invited to submit papers in all areas of wireless communications and mobile technologies, networks, services, and applications.
Prof Ekram Hossain on DLT 2013 in Indonesia

IEEE Communications Society (COMSOC) Indonesia Chapter proudly presest Prof Ekram Hossain on DLT 2013 in Bandung, Jakarta, Yogyakarta and Banten.
Institut Teknologi Telkom, Bandung, 27 August.
Universitas Mercu Buana, Jakarta, 28 August.
Universitas Gadjah Mada, Yogyakarta, 29 August.
Universitas Multimedia Nusantara, Banten, 30 August.
Lectures:
"Radio Resource Management in Multi-tier Cellular Wireless Networks"
and
"Modeling, Analysis, and Design of Multi-tier and Cognitive Cellular Wireless Networks"
M2M Day Two

M2M Optimizations in Public Mobile Networks
M2M Over a Telecommunications Network
Network Optimizations for M2M
The Role of IP in M2M
IPv6 for M2M
6LoWPAN
Routing Protocol for Low-Power and Lossy Networks (RPL) CoRE
M2M Security
Trust Relationships in the M2M Ecosystem
Security Requirements
Which Types of Solutions are Suitable?
Standardization Efforts on Securing M2M and MTC Communications
M2M Terminals and Modules
M2M Module Categorization
Hardware Interfaces
Temperature and Durability Services
Software Interface
Cellular Certification
M2M Day One

Introduction to M2M
What is M2M?
The Business of M2M
Accelerating M2M Maturity
M2M Standards
The Business of M2M
The M2M Market
The M2M Market Adoption: Drivers and Barriers
The M2M Value Chain
Market Size Projections
Business Models
M2M Business Metrics
Market Evolution
Early M2M Deployments
M2M Requirements and High-Level Architectural Principles
Use-Case-Driven Approach to M2M Requirements
Smart Metering Approach in ETSI M2M
eHealth Approach in ETSI M2M
High-Level Architecture Principles for M2M Communication
ETSI M2M Services Architecture
High-Level System Architecture
ETSI TC M2M Service Capabilities Framework
ETSI TC M2M Release 1 Scenarios
ETSI M2M Service Capabilities
Introducing REST Architectural Style for M2M
ETSI TC M2M Resource-Based M2M Communication and Procedures
Cloud Ecosystem

Cloud Ecosystem presented by Satriyo Dharmanto at IEEE Cloud Computing One Day Course, Institut Teknologi Telkom, Bandung, 11 August 201
Cloud and Ubiquitous Computing in Today's Era of Tera

Disampaikan pada 3 Agustus 2012 di ITB, Bandung
Cloud Computing: Peluang Bisnis dan Tantangan Regulasi

Disampaikan pada 3 Agustus 2012 di ITB, Bandung
More from Arief Gunawan (20)
Metaverse - Let's learn to understand when business becomes virtual and when ...

Metaverse - Let's learn to understand when business becomes virtual and when ...
Tutorial on Network Management and Security in Wireless Communications (Bandu...

Tutorial on Network Management and Security in Wireless Communications (Bandu...
Cloud and Ubiquitous Computing in Today's Era of Tera

Cloud and Ubiquitous Computing in Today's Era of Tera
Cloud Computing: Peluang Bisnis dan Tantangan Regulasi

Cloud Computing: Peluang Bisnis dan Tantangan Regulasi
Recently uploaded
Climate Impact of Software Testing at Nordic Testing Days

My slides at Nordic Testing Days 6.6.2024
Climate impact / sustainability of software testing discussed on the talk. ICT and testing must carry their part of global responsibility to help with the climat warming. We can minimize the carbon footprint but we can also have a carbon handprint, a positive impact on the climate. Quality characteristics can be added with sustainability, and then measured continuously. Test environments can be used less, and in smaller scale and on demand. Test techniques can be used in optimizing or minimizing number of tests. Test automation can be used to speed up testing.
Le nuove frontiere dell'AI nell'RPA con UiPath Autopilot™

In questo evento online gratuito, organizzato dalla Community Italiana di UiPath, potrai esplorare le nuove funzionalità di Autopilot, il tool che integra l'Intelligenza Artificiale nei processi di sviluppo e utilizzo delle Automazioni.
📕 Vedremo insieme alcuni esempi dell'utilizzo di Autopilot in diversi tool della Suite UiPath:
Autopilot per Studio Web
Autopilot per Studio
Autopilot per Apps
Clipboard AI
GenAI applicata alla Document Understanding
👨🏫👨💻 Speakers:
Stefano Negro, UiPath MVPx3, RPA Tech Lead @ BSP Consultant
Flavio Martinelli, UiPath MVP 2023, Technical Account Manager @UiPath
Andrei Tasca, RPA Solutions Team Lead @NTT Data
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar
Removing Uninteresting Bytes in Software Fuzzing

Imagine a world where software fuzzing, the process of mutating bytes in test seeds to uncover hidden and erroneous program behaviors, becomes faster and more effective. A lot depends on the initial seeds, which can significantly dictate the trajectory of a fuzzing campaign, particularly in terms of how long it takes to uncover interesting behaviour in your code. We introduce DIAR, a technique designed to speedup fuzzing campaigns by pinpointing and eliminating those uninteresting bytes in the seeds. Picture this: instead of wasting valuable resources on meaningless mutations in large, bloated seeds, DIAR removes the unnecessary bytes, streamlining the entire process.
In this work, we equipped AFL, a popular fuzzer, with DIAR and examined two critical Linux libraries -- Libxml's xmllint, a tool for parsing xml documents, and Binutil's readelf, an essential debugging and security analysis command-line tool used to display detailed information about ELF (Executable and Linkable Format). Our preliminary results show that AFL+DIAR does not only discover new paths more quickly but also achieves higher coverage overall. This work thus showcases how starting with lean and optimized seeds can lead to faster, more comprehensive fuzzing campaigns -- and DIAR helps you find such seeds.
- These are slides of the talk given at IEEE International Conference on Software Testing Verification and Validation Workshop, ICSTW 2022.
SAP Sapphire 2024 - ASUG301 building better apps with SAP Fiori.pdf

Building better applications for business users with SAP Fiori.
• What is SAP Fiori and why it matters to you
• How a better user experience drives measurable business benefits
• How to get started with SAP Fiori today
• How SAP Fiori elements accelerates application development
• How SAP Build Code includes SAP Fiori tools and other generative artificial intelligence capabilities
• How SAP Fiori paves the way for using AI in SAP apps
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

In this session I delve into the encryption technology used in Microsoft 365 and Microsoft Purview. Including the concepts of Customer Key and Double Key Encryption.
A tale of scale & speed: How the US Navy is enabling software delivery from l...

Rapid and secure feature delivery is a goal across every application team and every branch of the DoD. The Navy’s DevSecOps platform, Party Barge, has achieved:
- Reduction in onboarding time from 5 weeks to 1 day
- Improved developer experience and productivity through actionable findings and reduction of false positives
- Maintenance of superior security standards and inherent policy enforcement with Authorization to Operate (ATO)
Development teams can ship efficiently and ensure applications are cyber ready for Navy Authorizing Officials (AOs). In this webinar, Sigma Defense and Anchore will give attendees a look behind the scenes and demo secure pipeline automation and security artifacts that speed up application ATO and time to production.
We will cover:
- How to remove silos in DevSecOps
- How to build efficient development pipeline roles and component templates
- How to deliver security artifacts that matter for ATO’s (SBOMs, vulnerability reports, and policy evidence)
- How to streamline operations with automated policy checks on container images
Video Streaming: Then, Now, and in the Future

In his public lecture, Christian Timmerer provides insights into the fascinating history of video streaming, starting from its humble beginnings before YouTube to the groundbreaking technologies that now dominate platforms like Netflix and ORF ON. Timmerer also presents provocative contributions of his own that have significantly influenced the industry. He concludes by looking at future challenges and invites the audience to join in a discussion.
Generative AI Deep Dive: Advancing from Proof of Concept to Production

Join Maher Hanafi, VP of Engineering at Betterworks, in this new session where he'll share a practical framework to transform Gen AI prototypes into impactful products! He'll delve into the complexities of data collection and management, model selection and optimization, and ensuring security, scalability, and responsible use.
Observability Concepts EVERY Developer Should Know -- DeveloperWeek Europe.pdf

Monitoring and observability aren’t traditionally found in software curriculums and many of us cobble this knowledge together from whatever vendor or ecosystem we were first introduced to and whatever is a part of your current company’s observability stack.
While the dev and ops silo continues to crumble….many organizations still relegate monitoring & observability as the purview of ops, infra and SRE teams. This is a mistake - achieving a highly observable system requires collaboration up and down the stack.
I, a former op, would like to extend an invitation to all application developers to join the observability party will share these foundational concepts to build on:
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
GraphRAG is All You need? LLM & Knowledge Graph

Guy Korland, CEO and Co-founder of FalkorDB, will review two articles on the integration of language models with knowledge graphs.
1. Unifying Large Language Models and Knowledge Graphs: A Roadmap.
https://arxiv.org/abs/2306.08302
2. Microsoft Research's GraphRAG paper and a review paper on various uses of knowledge graphs:
https://www.microsoft.com/en-us/research/blog/graphrag-unlocking-llm-discovery-on-narrative-private-data/
Essentials of Automations: The Art of Triggers and Actions in FME

In this second installment of our Essentials of Automations webinar series, we’ll explore the landscape of triggers and actions, guiding you through the nuances of authoring and adapting workspaces for seamless automations. Gain an understanding of the full spectrum of triggers and actions available in FME, empowering you to enhance your workspaces for efficient automation.
We’ll kick things off by showcasing the most commonly used event-based triggers, introducing you to various automation workflows like manual triggers, schedules, directory watchers, and more. Plus, see how these elements play out in real scenarios.
Whether you’re tweaking your current setup or building from the ground up, this session will arm you with the tools and insights needed to transform your FME usage into a powerhouse of productivity. Join us to discover effective strategies that simplify complex processes, enhancing your productivity and transforming your data management practices with FME. Let’s turn complexity into clarity and make your workspaces work wonders!
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

Do you want to learn how to model and simulate an electrical network from scratch in under an hour?
Then welcome to this PowSyBl workshop, hosted by Rte, the French Transmission System Operator (TSO)!
During the webinar, you will discover the PowSyBl ecosystem as well as handle and study an electrical network through an interactive Python notebook.
PowSyBl is an open source project hosted by LF Energy, which offers a comprehensive set of features for electrical grid modelling and simulation. Among other advanced features, PowSyBl provides:
- A fully editable and extendable library for grid component modelling;
- Visualization tools to display your network;
- Grid simulation tools, such as power flows, security analyses (with or without remedial actions) and sensitivity analyses;
The framework is mostly written in Java, with a Python binding so that Python developers can access PowSyBl functionalities as well.
What you will learn during the webinar:
- For beginners: discover PowSyBl's functionalities through a quick general presentation and the notebook, without needing any expert coding skills;
- For advanced developers: master the skills to efficiently apply PowSyBl functionalities to your real-world scenarios.
Recently uploaded (20)
Climate Impact of Software Testing at Nordic Testing Days

Climate Impact of Software Testing at Nordic Testing Days
Le nuove frontiere dell'AI nell'RPA con UiPath Autopilot™

Le nuove frontiere dell'AI nell'RPA con UiPath Autopilot™
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf
SAP Sapphire 2024 - ASUG301 building better apps with SAP Fiori.pdf

SAP Sapphire 2024 - ASUG301 building better apps with SAP Fiori.pdf
Free Complete Python - A step towards Data Science

Free Complete Python - A step towards Data Science
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

Encryption in Microsoft 365 - ExpertsLive Netherlands 2024
A tale of scale & speed: How the US Navy is enabling software delivery from l...

A tale of scale & speed: How the US Navy is enabling software delivery from l...
Generative AI Deep Dive: Advancing from Proof of Concept to Production

Generative AI Deep Dive: Advancing from Proof of Concept to Production
Monitoring Java Application Security with JDK Tools and JFR Events

Monitoring Java Application Security with JDK Tools and JFR Events
Observability Concepts EVERY Developer Should Know -- DeveloperWeek Europe.pdf

Observability Concepts EVERY Developer Should Know -- DeveloperWeek Europe.pdf
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
Essentials of Automations: The Art of Triggers and Actions in FME

Essentials of Automations: The Art of Triggers and Actions in FME
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...
WIMAX Network Dimensioning Course
- 1. WiMAX Network Dimensioning Course Pre-requisite Training : Basic Wireless, TCP/IP and WiMAX Fundamental Syllabi Traiiner Tra ner 1.Introduce WiMAX Hadi Hariyanto, ST.,M.Sc. a. Latar Belakang WiMAX Member IEEE COMSOC Indonesia Chapter, b. Fitur Utama WiMAX Guest Lecturer at Telkom Institute of Management, Bandung, Engineer of wireless c. Advanced Antenna System (MIMO, Beam laboratory at Telkom RDC, Bandung, M.Sc on Forming) Wireless SURREY University, England. d. Quality of Service F.X. Ari Wibowo, ST., MT. e. Kerangka Kerja Network Dimensioning pada Member IEEE Indonesia Section, IEEE COMSOC WiMAX Indonesia Chapter, MT on Telecommunications, Bandung Institute of Technology, Guest Lecturer at Telkom 2. Aspek Coverage pada WiMAX RF Planning Institute of Management, Bandung, Engineer of a. Tahapan Perencanaan Jaringan WiMAX Service & Product Planning at Telkom b. Isu pada Coverage WiMAX Research & Development Center. c. Pathloss dan Link Budget d. Sekilas Tentang Model Propagasi e. Propagation Model Cost 231 Hatta f. Propagation Model Standford University (SUI) g. Propagation Model ECC-33 h. Pengaruh Adaptive Modulation terhadap Registration Fee : Coverage Professional : Rp.750.000,- (free FD 16 GB) i. Pengaruh MIMO terhadap Coverage Universities : Rp.500.000,- (free FD 8 GB) j. Perbandingan Coverage WiMAX k. Contoh Perhitungan Jumlah BS berbasis Student : Rp.400.000,- (free Registrasi Coverage IEEE Member) l. Fixed WiMAX vs Mobile WiMAX Disc 20% for Member IEEE 3. Aspek Kapasitas pada WiMAX RF Planning a. Pengertian Kapasitas Facilities : b. Model Trafik Layanan Data Fee including 1x Lunch, 2x Coffee break, c. Over Subscription Certificate, and Seminar Kit, Free Hotspot Area d. Kategori Pelanggan e. Perhitungan Throughput Time Place f. Perhitungan Kapasitas Juni 12, 2010 Asiatic Resto g. Pengaruh Bandwidth Ratio 09.00 – 17.00 WIB Jl.HR. Bunyamin 375,Purwokerto h. Pengaruh MIMO i. Pengaruh Frequency Planning The registration fee should be transferred into j. Contoh Perhitungan Jumlah BS berbasis the following account (The registration fee Kapasitas should be transferred before Juni 10, 2010) : k. Kesimpulan a.n. Widhiatmoko Herry Purnomo acc. 139-0004798090 Bank Mandiri Cab. UNSOED, Purwokerto For Future Information please Contact: Nova Rismartanto Phone : +62-85647336666, Email : richie_te@yahoo.com Widhiatmoko Herry Purnomo (Aries) Phone : +62-8156871444, Flexi : +62-281 7666377
