This document provides an overview of cloud architecture and cloud computing reference architecture. It discusses:
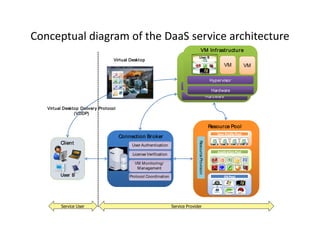
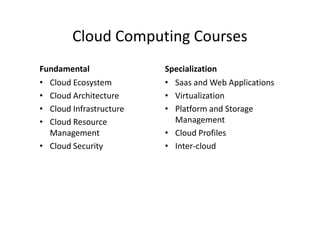
1. The scope covers defining functional requirements and reference architecture for cloud computing, including functional layers, blocks, and service architectures.
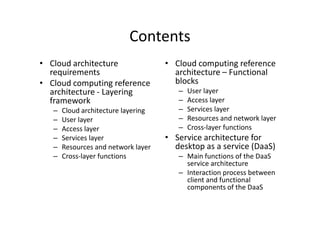
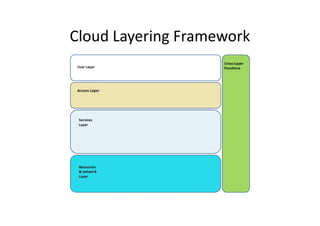
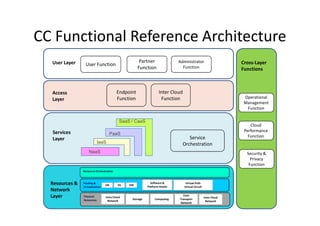
2. The cloud computing reference architecture includes layers like the user layer, access layer, services layer, resources and network layer, and cross-layer functions. It also describes functional blocks within these layers.
3. Requirements for cloud architecture are outlined, such as supporting standards, deployment models, and enabling services to appear like intranet services.