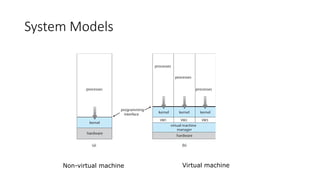
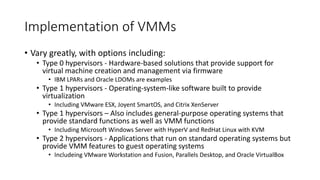
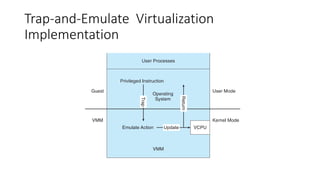
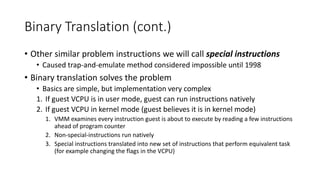
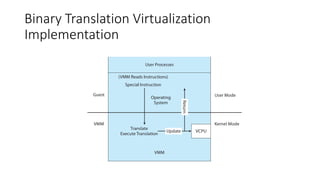
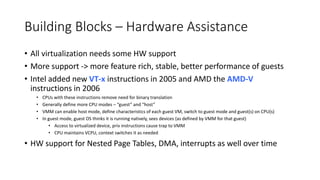
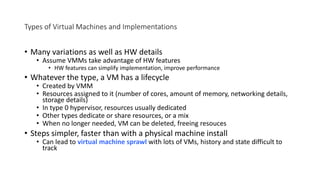
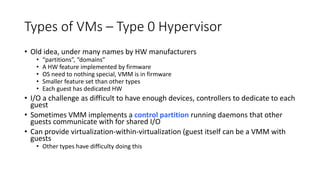
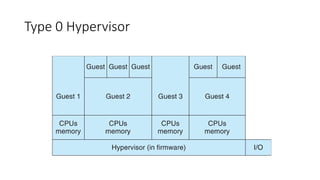
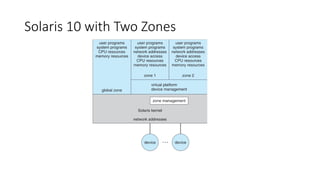
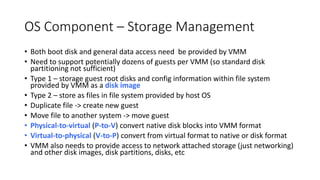
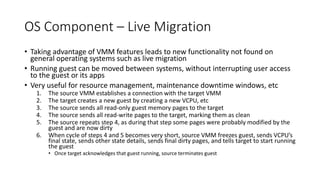
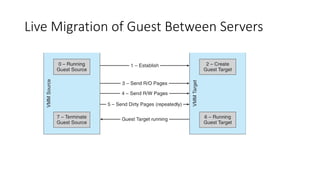
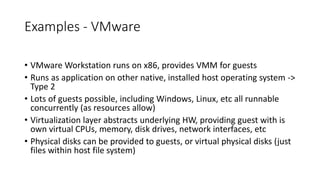
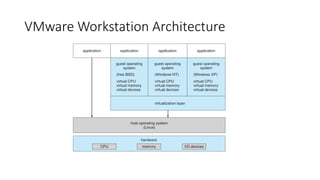
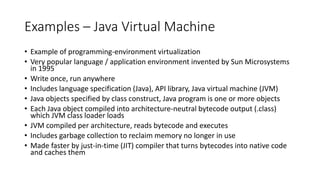
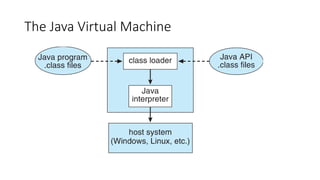
This document discusses virtual machines and their implementation. It begins with an overview of virtual machines, including the key components of a host, virtual machine manager/hypervisor, and guest. It then covers different system models and types of virtual machine managers from hardware-based to software-based. The document discusses the history, benefits, and building blocks of virtual machines like trap-and-emulate and binary translation techniques. It also covers hardware assistance for virtualization and the lifecycle of virtual machines.