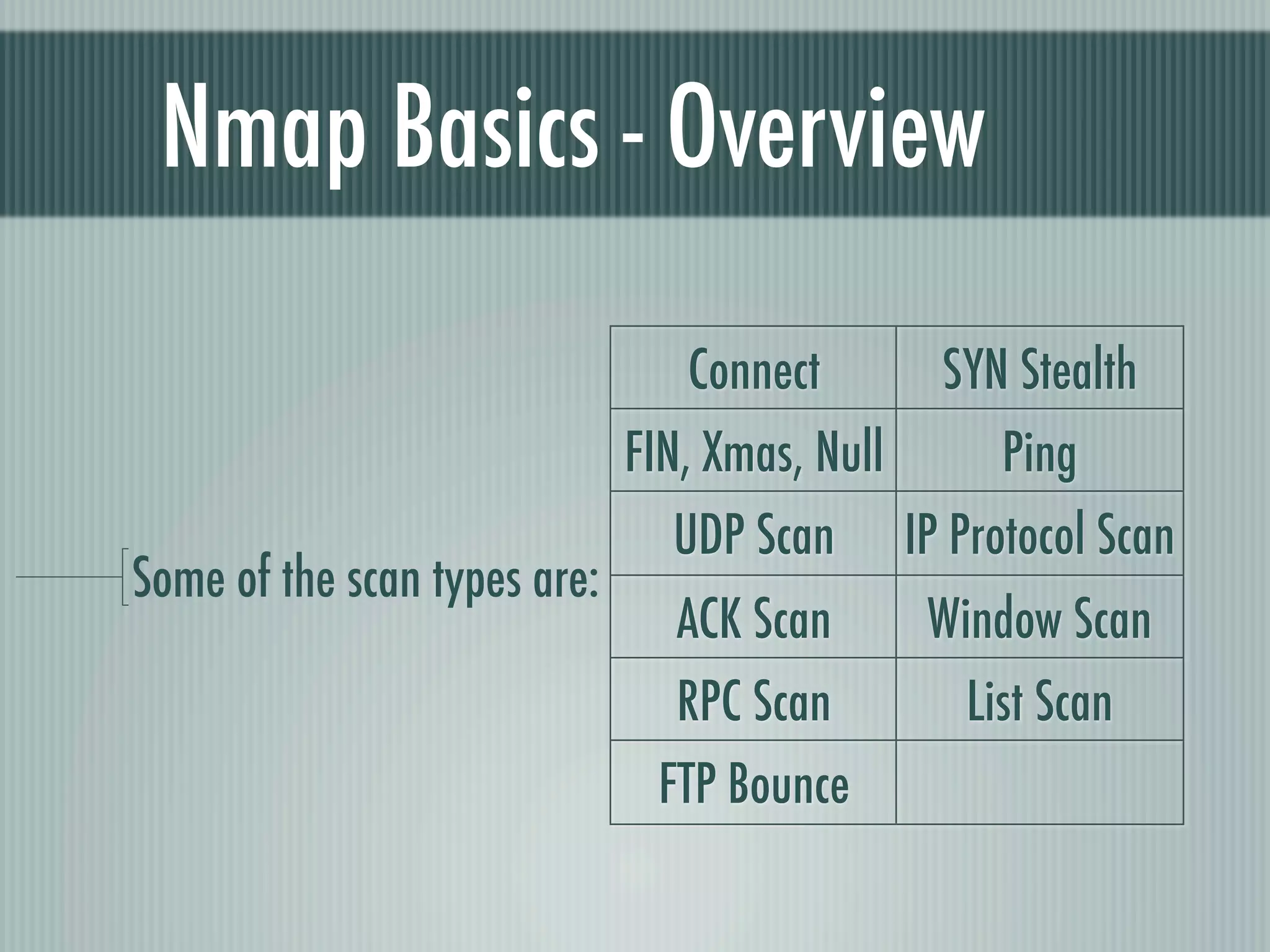
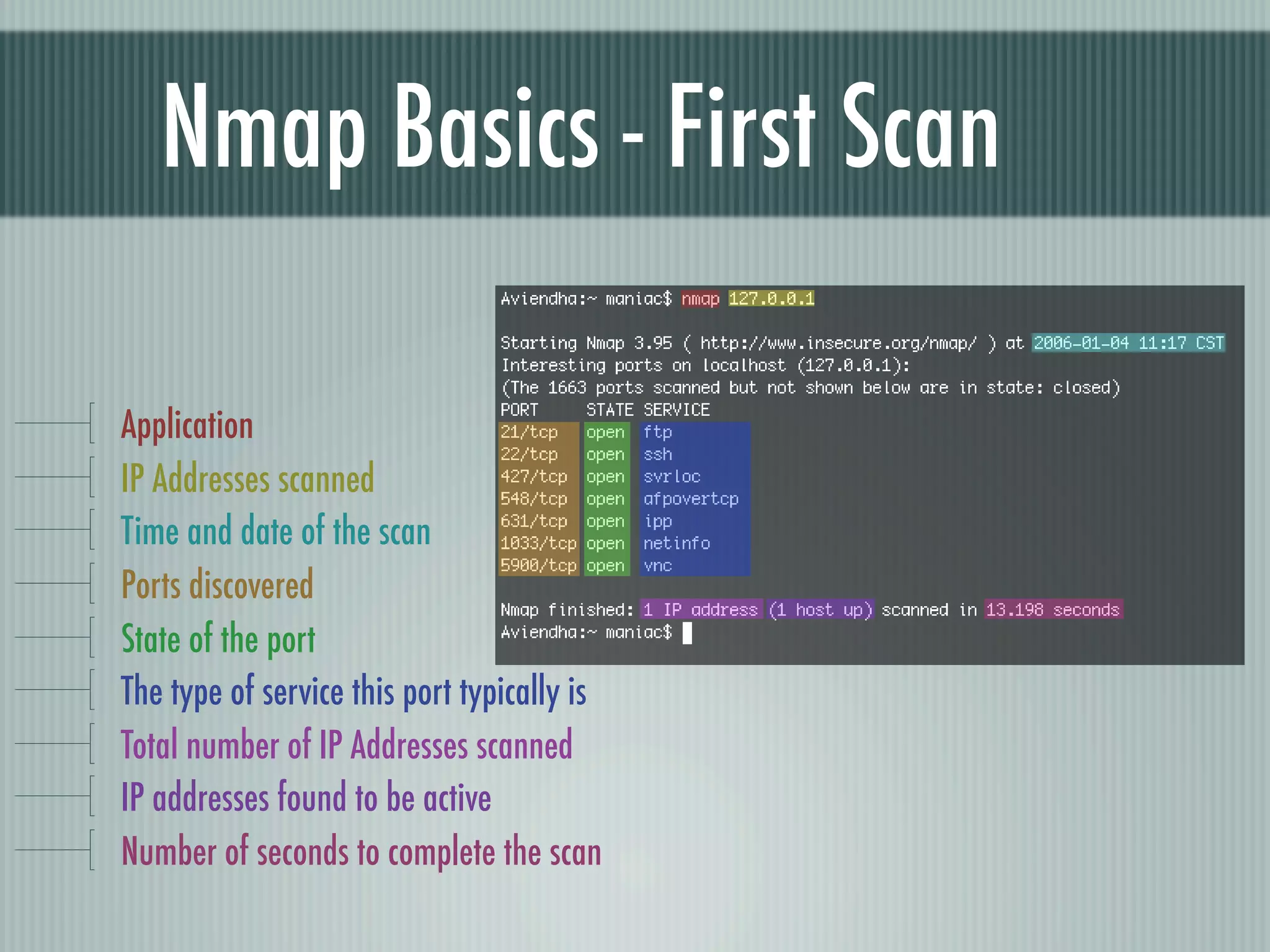
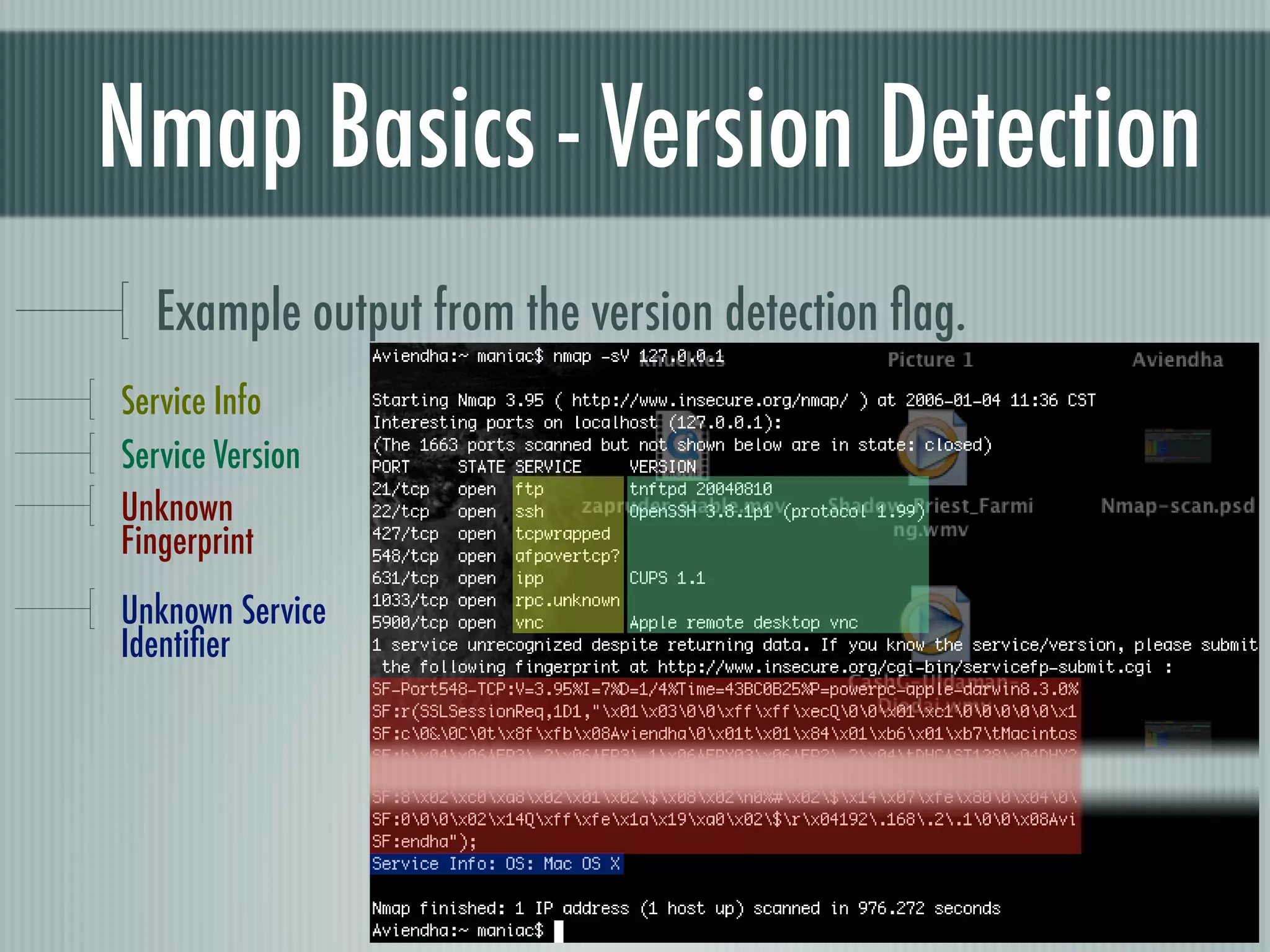
Nmap is an open source network scanning tool that can discover hosts on a network, services running on hosts, operating systems in use, and vulnerabilities. It uses raw IP packets to determine details about targets. Nmap runs on Linux, Windows, and other platforms and has both command line and graphical interfaces. Common scan types include TCP connect, SYN stealth, UDP scans, and operating system detection to reveal details about targets on a network.