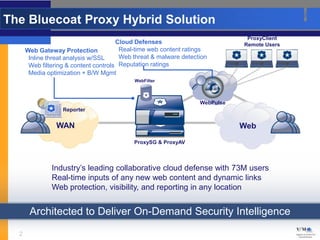
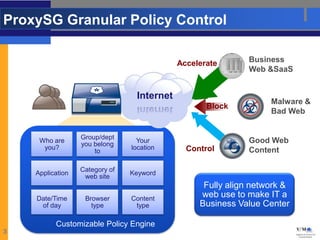
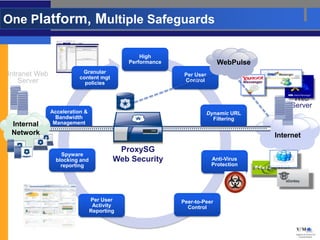
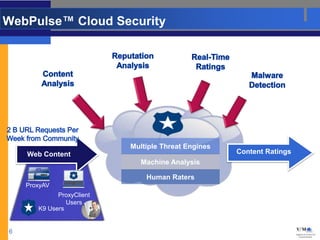
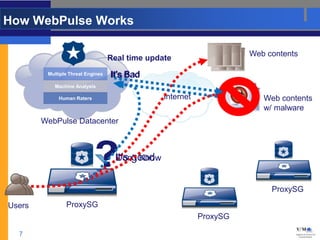
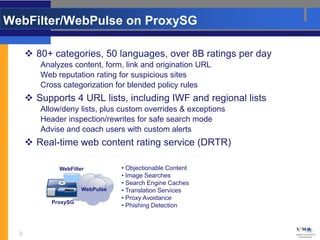
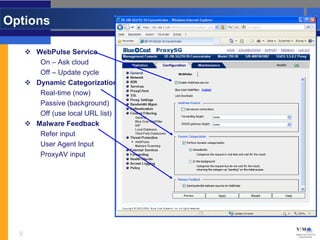
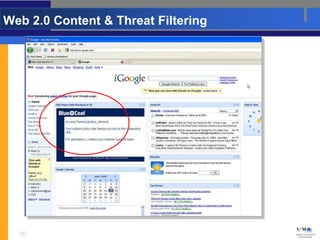
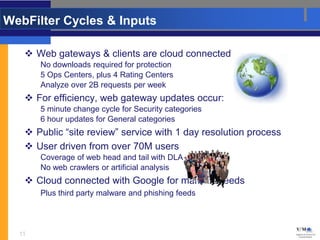
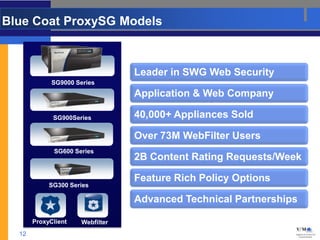
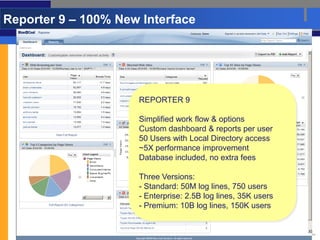
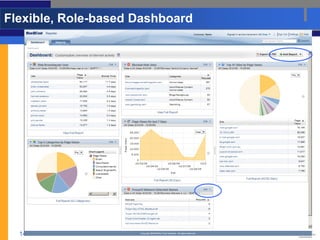
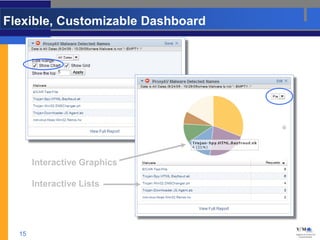
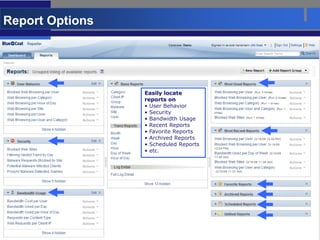
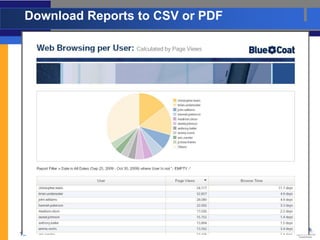
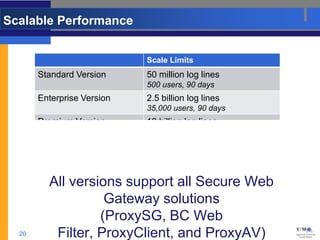
The Bluecoat ProxySG solution provides web filtering, malware protection, and reporting through its integrated WebFilter and WebPulse cloud services which analyze over 2 billion requests per week to provide real-time web ratings and threats intelligence to the ProxySG appliance. The new Reporter 9 interface provides customized dashboards and reporting for up to 150,000 users with scalable log storage and performance.