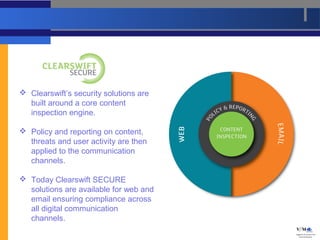
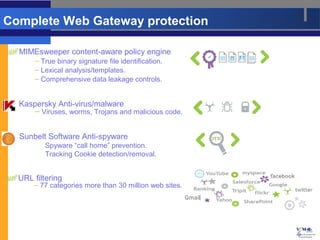
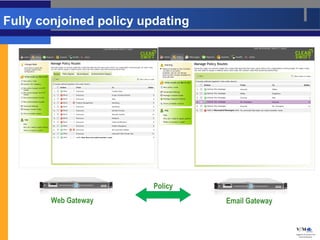
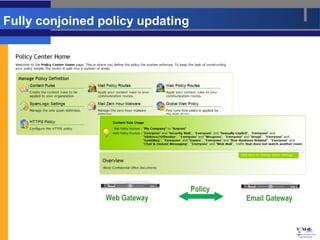
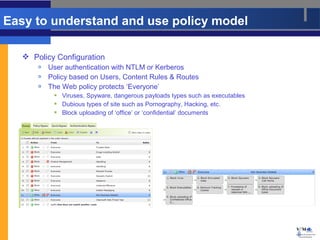
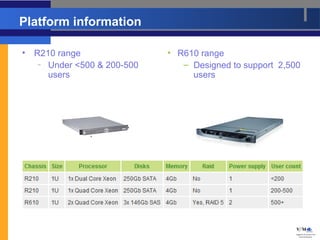
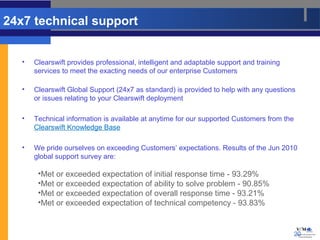
This document summarizes the Clearswift SECURE Email Gateway 3.2. It discusses how Clearswift aims to simplify IT security for businesses to protect data and intellectual property. It then describes Clearswift's secure web and email gateway solutions, which apply policies and reporting across digital communication channels like web and email. The document provides details on the secure web gateway platform, its protection capabilities like antivirus and URL filtering, easy policy management, and support services.