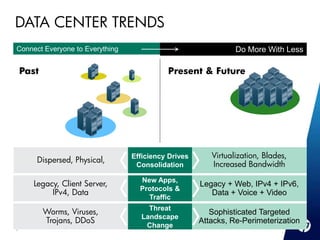
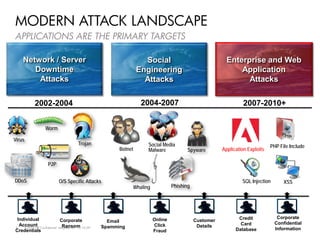
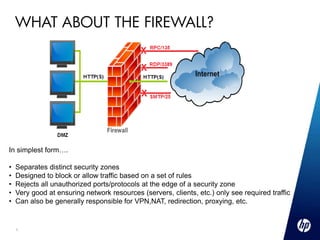
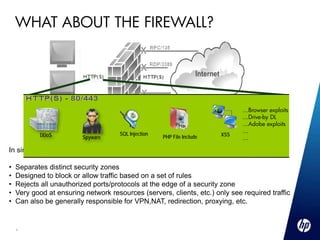
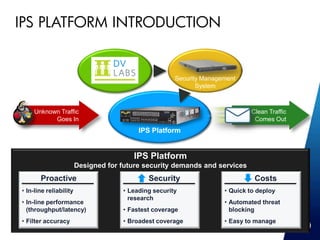
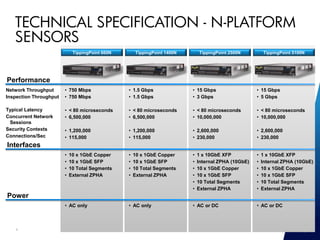
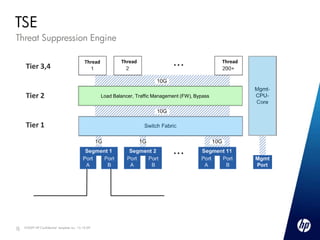
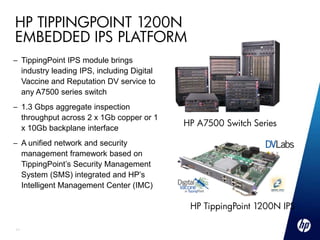
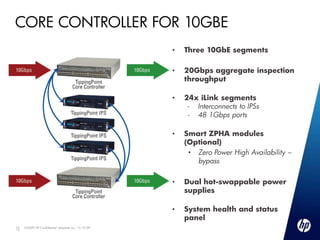
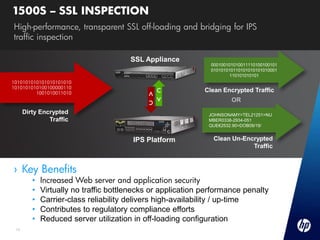
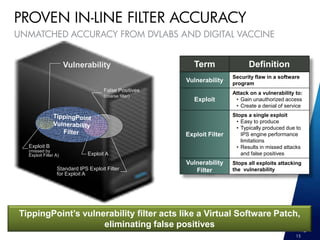
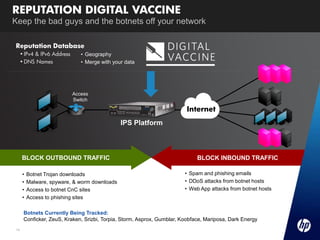
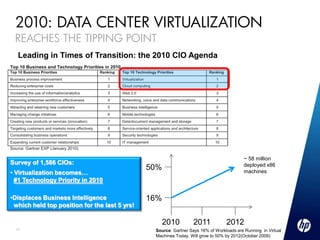
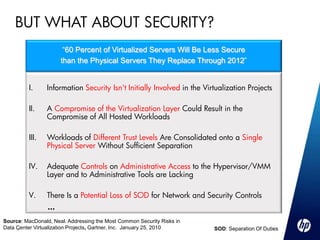
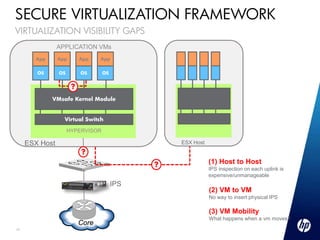
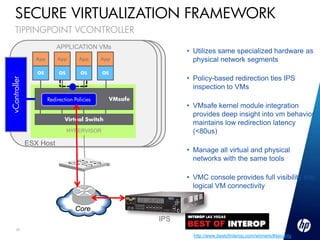
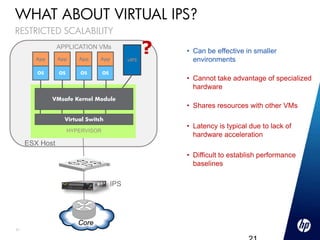
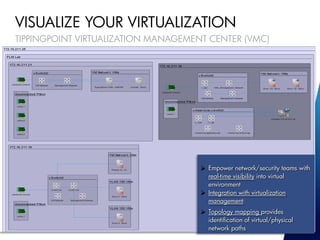
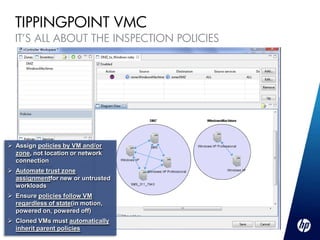
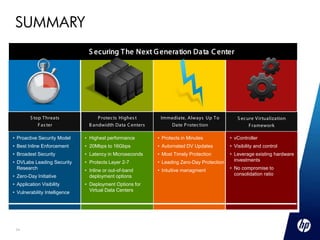
This document discusses HP TippingPoint's IPS and virtualization security solutions for data centers. It provides an overview of the modern threat landscape facing applications, and introduces HP TippingPoint's IPS platform and product lines. Key details include the platform's performance capabilities, available models in the S-Series and N-Series, and the TippingPoint 1200N embedded IPS module for HP switches. Virtualization security solutions are also briefly mentioned.