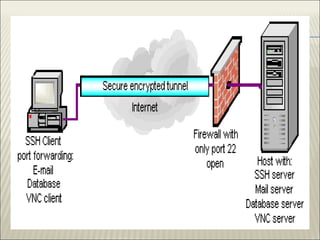
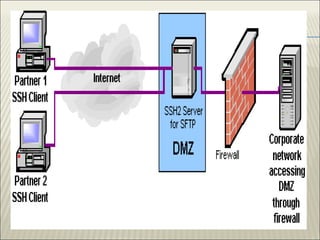
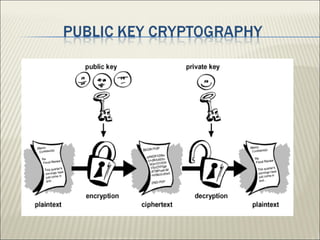
The document discusses the Secure Shell (SSH) protocol, detailing its history, functions, and architecture, including the transition from SSH-1 to SSH-2 with improvements in security. It highlights protocols for secure communication and file transfer between computers while addressing potential security issues like IP and DNS spoofing. SSH serves as a general-purpose tunneling platform, enhancing security across various applications by implementing robust encryption and authentication methods.



![ [1] Cusack, F. and Forssen, M. "Generic Message Exchange
Authentication for the Secure Shell Protocol (SSH)," RFC 4256,
January 2006.
[2] Lehtinen, S. and Lonvick, C., "The Secure Shell (SSH) Protocol
Assigned Numbers," RFC 4250, January 2006.
[3] JSchlyter, J. and Griffin, W. "Using DNS to Securely Publish Secure
Shell (SSH) Key Fingerprints," RFC 4255, January 2006.
[4] Ylonen, T., "SSH – Secure Login Connections over the Internet,"
Proceedings, Sixth USENIX UNIX Security Symposium, July 1996.](https://image.slidesharecdn.com/secureshellprotocolfinal-150303070353-conversion-gate01/85/Secure-shell-protocol-28-320.jpg)
