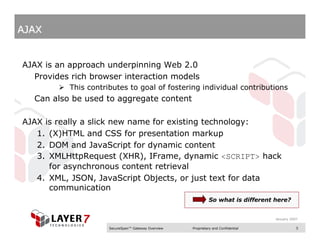
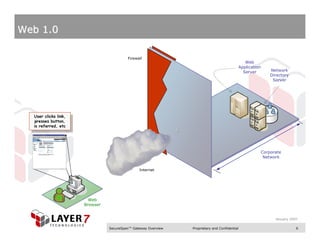
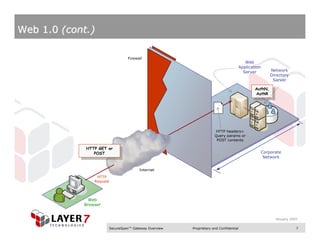
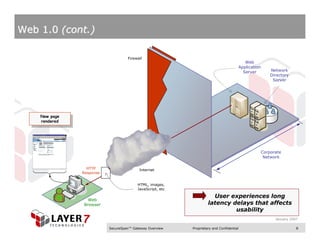
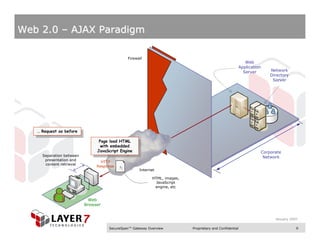
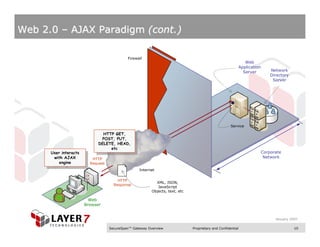
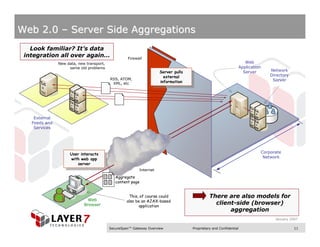
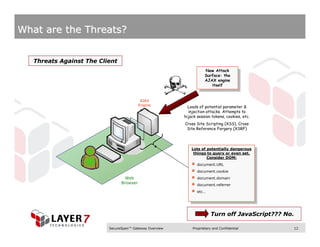
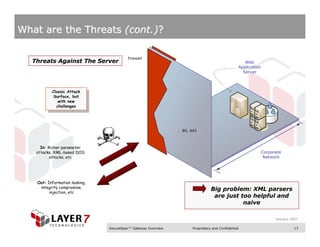
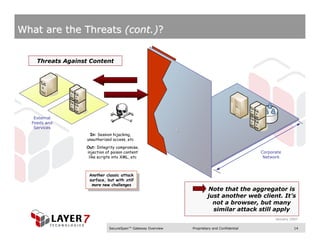
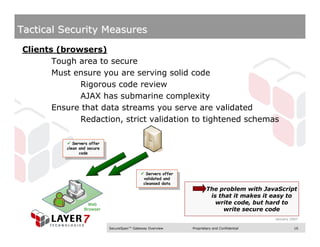
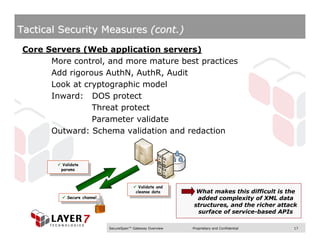
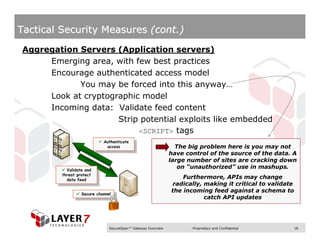
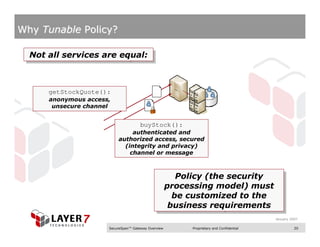
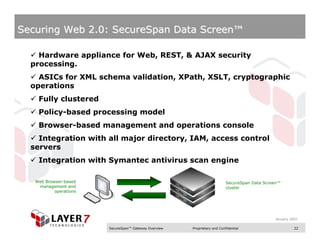
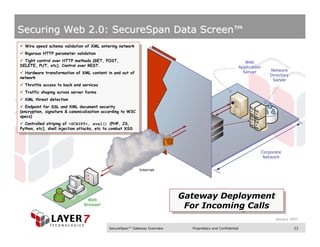
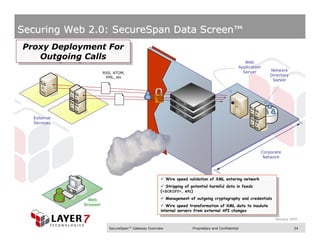
This document discusses securing web applications in the Web 2.0 era. It begins by explaining what Web 2.0 and AJAX are and how they have introduced new threats compared to traditional web applications. It then outlines various threat vectors against clients, servers, and aggregated content. Tactical security measures are proposed for clients, servers, and aggregation servers. Finally, the document introduces the SecureSpan Data Screen appliance as a specialized infrastructure solution for applying tunable security policies to address the evolving threats of Web 2.0.