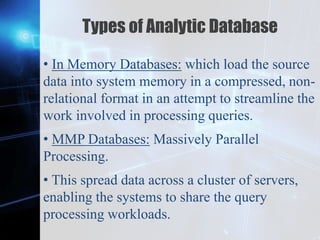
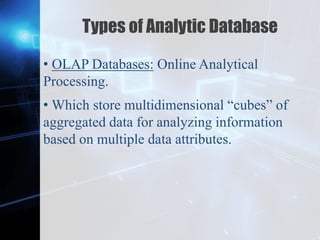
This document discusses trends in database management. It begins by reviewing basic database concepts like data, information, databases, and DBMS. It then covers the scope of the lesson which includes operational databases, analytical databases, data warehouses, and distributed databases. Each of these topics are defined and examples are provided. Operational databases are used for real-time data management while analytical databases support business intelligence. Data warehouses store historical data for analysis and reporting. Distributed databases have portions of data stored across multiple computers within a network.