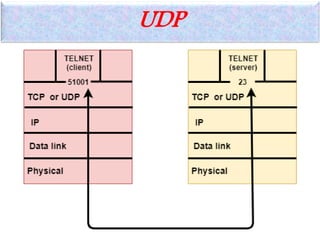
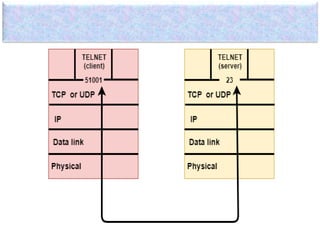
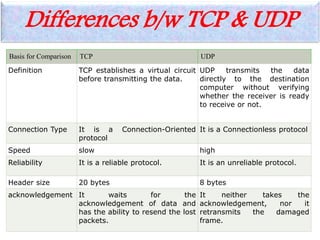
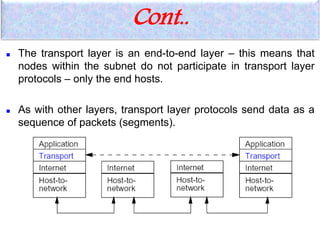
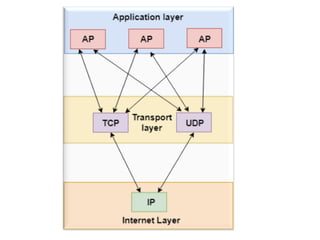
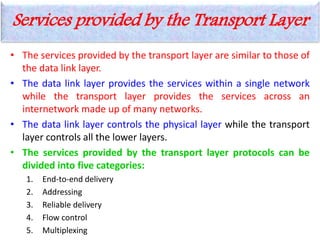
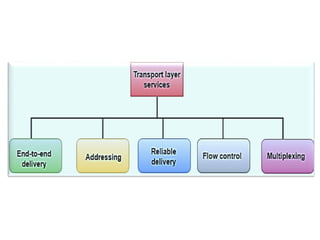
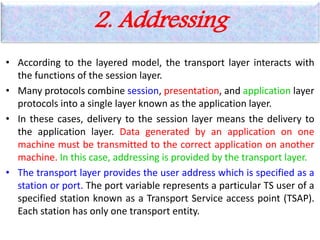
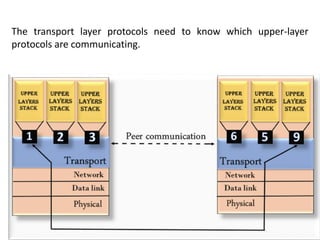
The transport layer provides logical communication between application processes running on different hosts. It implements protocols like TCP and UDP that provide services such as multiplexing, reliable data transfer, and flow control. TCP is connection-oriented and provides reliable, ordered delivery of streams of bytes. UDP is connectionless and offers low-latency communications at the cost of reliability. The transport layer addresses ensure end-to-end delivery of data packets from source to destination applications.
![Cont..
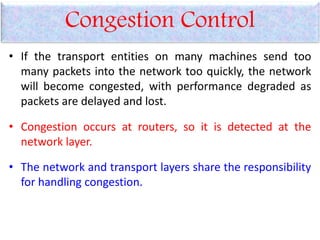
• However, the most effective way to control congestion is to reduce
the load that the transport layer is placing on the network.
Two layers are the responsible for congestion control:
• Transport layer, controls the offered load [here]
• Network layer, experiences congestion [previous]
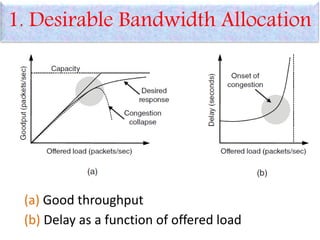
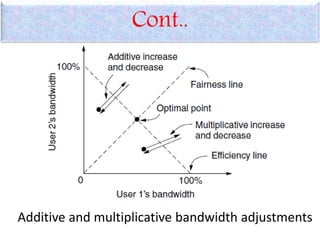
– Desirable bandwidth allocation
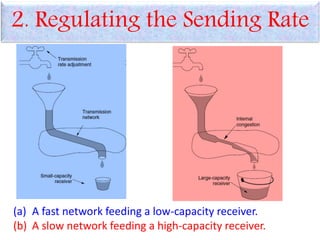
– Regulating the sending rate
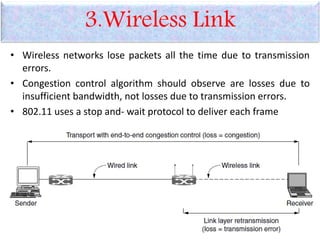
– Wireless issues](https://image.slidesharecdn.com/transportlayer-200201063112/85/Transport-layer-26-320.jpg)