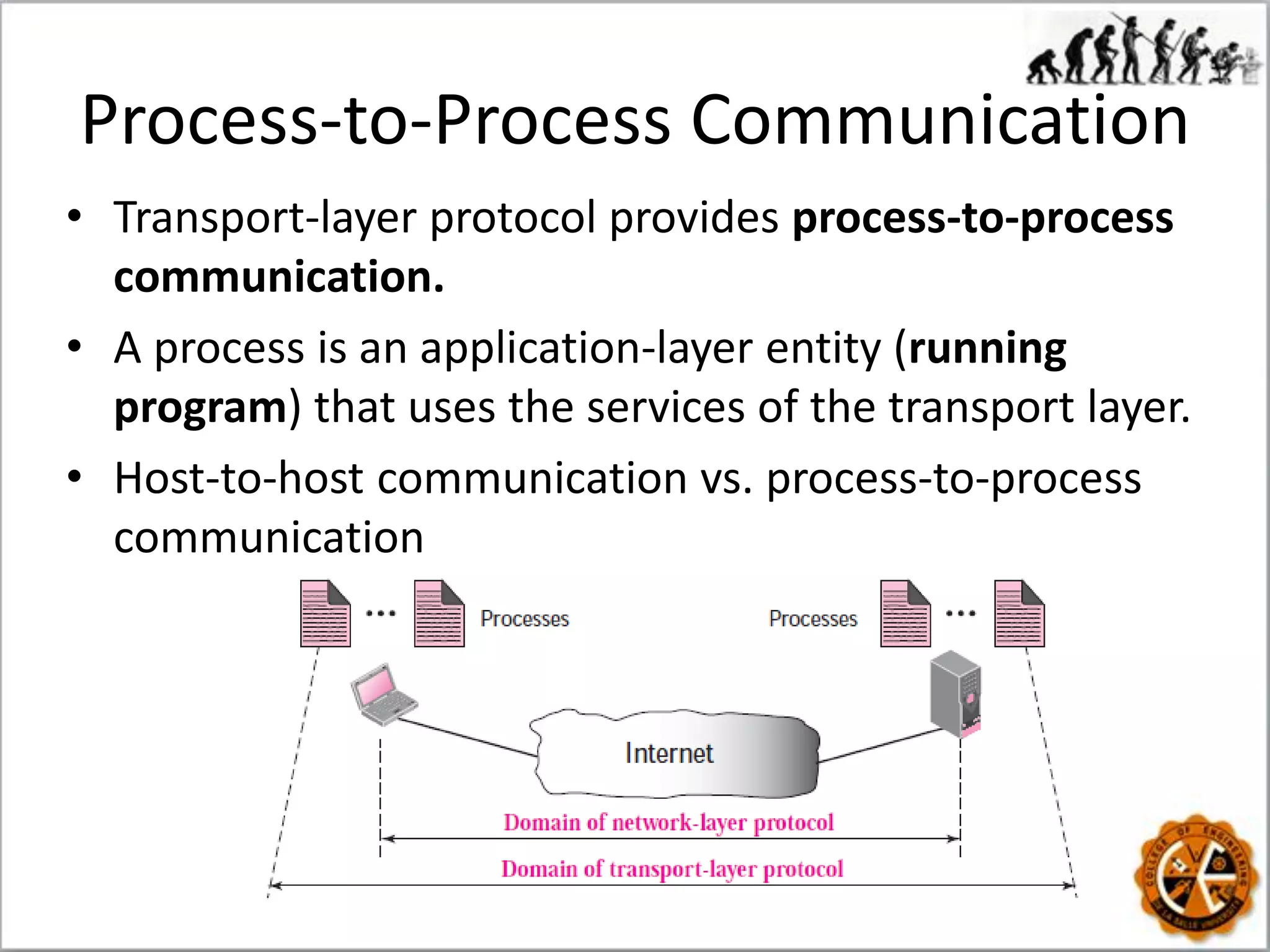
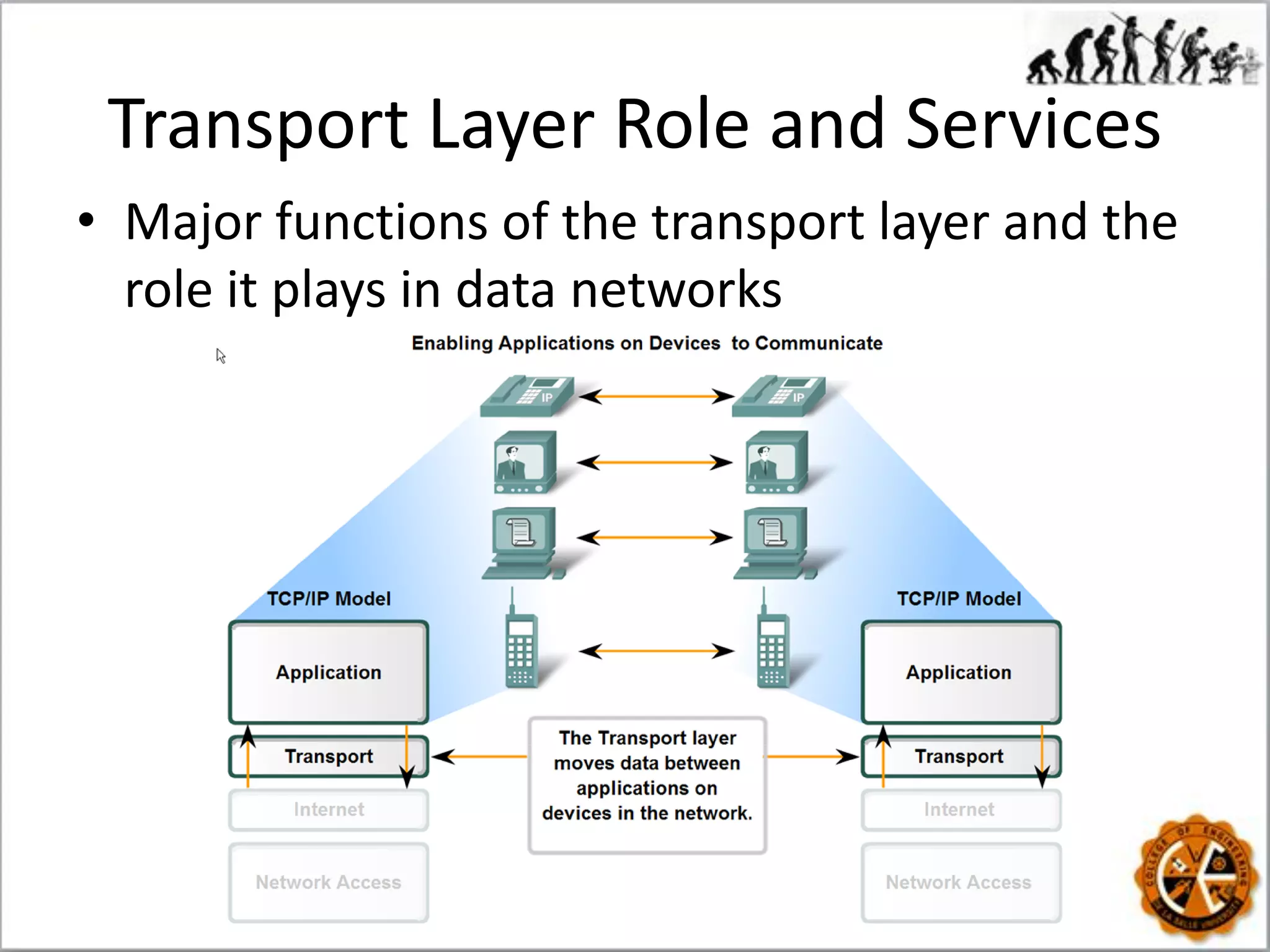
The document discusses transport layer protocols TCP and UDP. It provides an overview of process-to-process communication using transport layer protocols. It describes the roles, services, requirements, addressing, encapsulation, multiplexing, and error control functions of the transport layer. It specifically examines TCP and UDP, comparing their connection-oriented and connectionless services, typical applications, and segment/datagram formats.