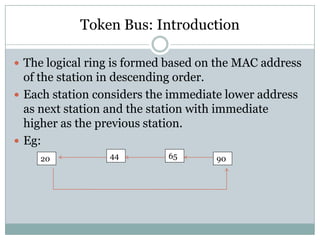
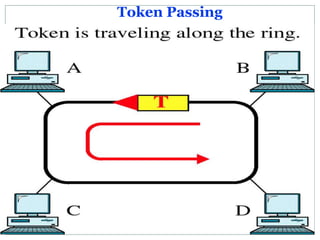
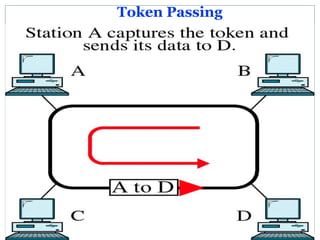
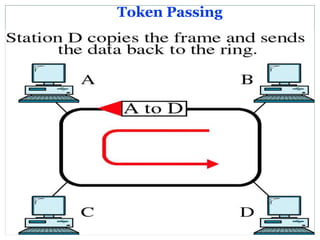
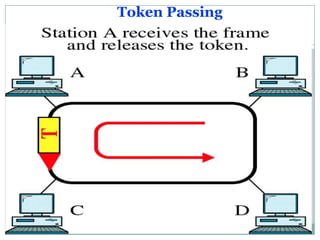
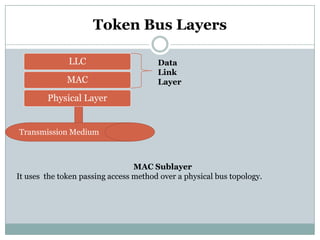
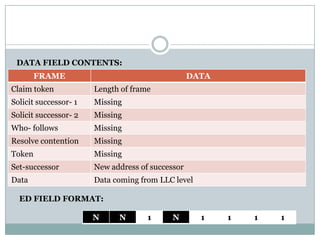
The document discusses Token Bus, which combines features of Ethernet and Token Ring. It operates as a physical bus but with stations logically organized into a ring, passing a token among them. Only the station holding the token can transmit data. Token Bus was limited to industrial applications and saw no commercial use for data communication. It uses the token passing mechanism over a physical bus topology at the data link layer.