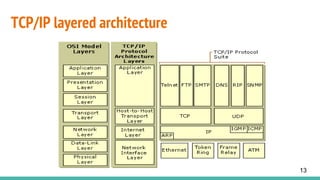
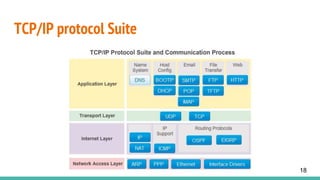
TCP/IP is a set of communication protocols that enable data transmission across networks and between devices. It involves two main protocols: TCP and IP. TCP establishes reliable connections and ensures reliable delivery of data packets. IP handles addressing, routing packets between networks, and fragmentation/reassembly of packets. Key features of TCP/IP include logical addressing, routability, name resolution, multiplexing, and interoperability. TCP/IP operates on four layers - network interface, internet, transport, and application - with each layer building on the services of the layer below.