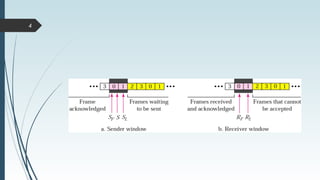
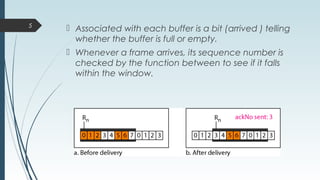
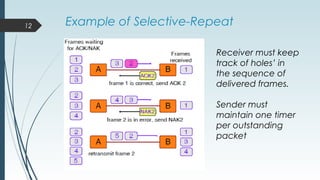
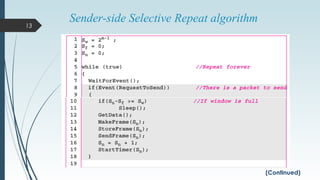
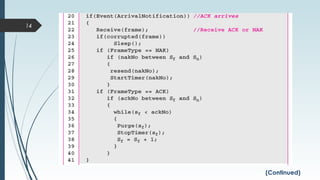
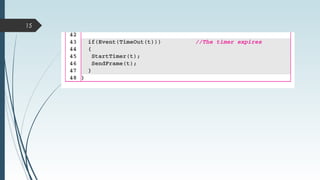
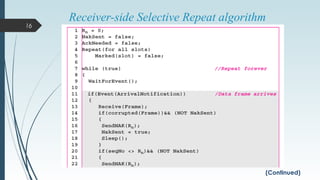
The selective repeat protocol allows the receiver to accept and buffer frames following a damaged or lost one. Both the sender and receiver maintain a window of outstanding and acceptable sequence numbers. The receiver has a buffer for each sequence number within its fixed window. Whenever a frame arrives within the receiver's window, it is accepted and stored without regard to expected sequence. This protocol has fewer retransmissions than go-back-n but is more complex, as each frame must be acknowledged individually and the receiver may receive frames out of order.