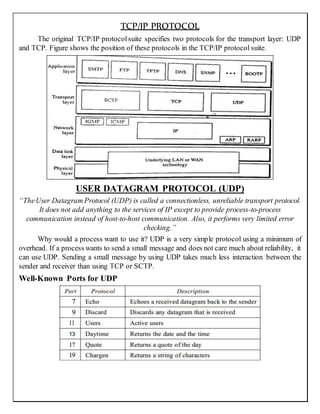
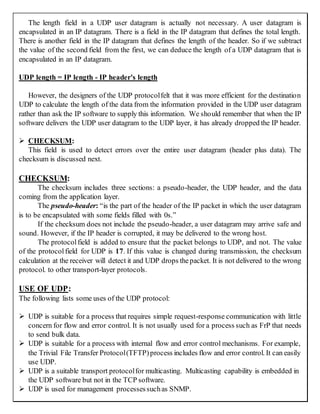
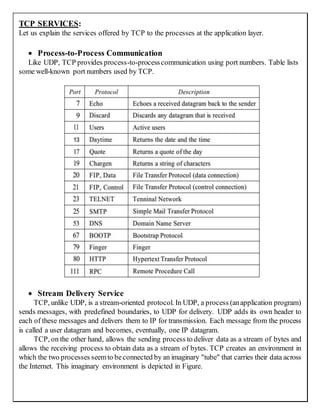
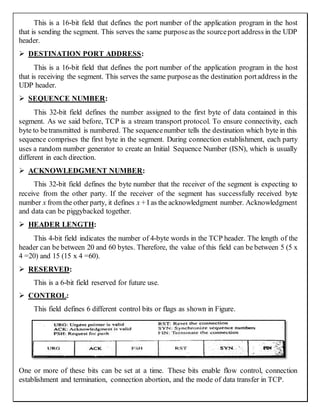
The document discusses the TCP/IP protocol suite and the UDP and TCP transport layer protocols. UDP is a connectionless, unreliable protocol that provides basic process-to-process communication with minimal overhead. TCP is a connection-oriented, reliable protocol that establishes virtual connections between processes, provides reliable in-order data delivery through flow and error control mechanisms, and allows processes to communicate via data streams. Both protocols use port numbers to identify communicating processes and encapsulate data in IP datagrams for transmission.