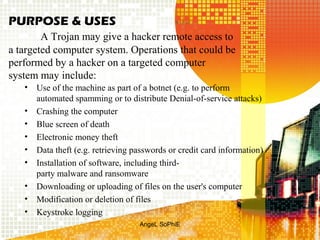
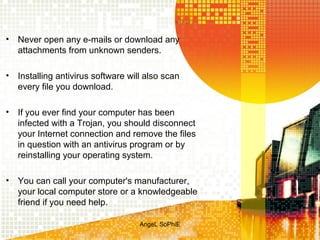
A Trojan horse is a destructive program that masquerades as a benign application. It does not replicate like viruses but can still cause damage. Trojan horses are classified based on how they breach systems and the damage they cause. The main types are remote access Trojans, data sending Trojans, destructive Trojans, proxy Trojans, FTP Trojans, security software disabler Trojans, and DoS attack Trojans. People can protect themselves by not opening emails from unknown senders, using antivirus software, and disconnecting from the internet if infected.