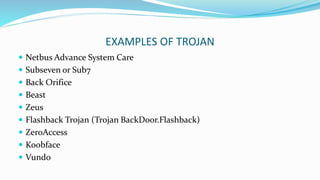
This document discusses trojans and backdoors. It defines a trojan as a malicious program that misrepresents itself as useful to install itself on a victim's computer. Trojans are used for destructive purposes like crashing systems or stealing data, or for using the computer's resources. Examples of trojans provided include Netbus and Back Orifice. Backdoors are methods of bypassing authentication to gain unauthorized access. They work by installing hidden server software that listens for connections from client software controlled by attackers. Known backdoors discussed include Back Orifice and a possible NSA backdoor in a cryptographic standard.