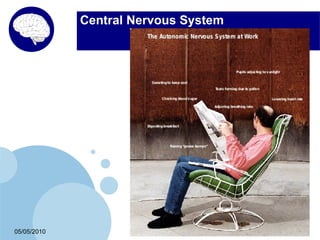
- Autonomic computing is a discipline that aims to create self-managing computer systems inspired by biological systems like the human central nervous system.
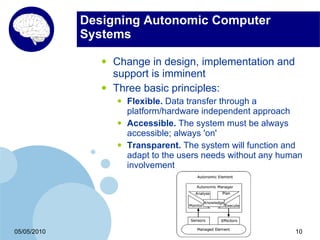
- It aims to overcome the complexity and inability to effectively maintain current and emerging computer systems by making systems self-configuring, self-healing, self-optimizing and self-protecting.
- Early research projects are exploring techniques like recovery-oriented computing, self-securing storage, and swarm-based autonomous systems to achieve attributes of self-management in systems.