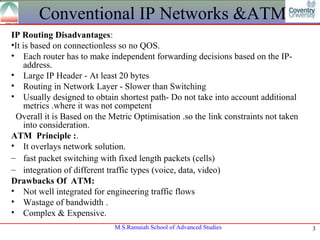
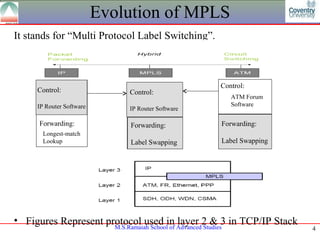
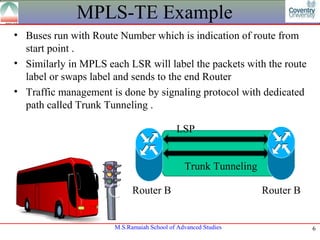
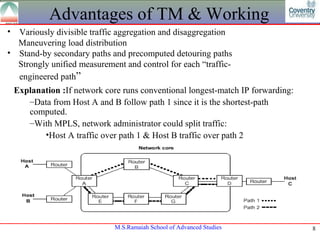
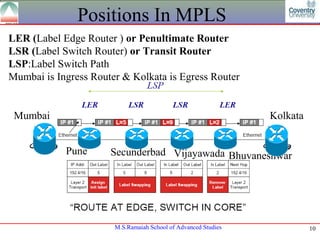
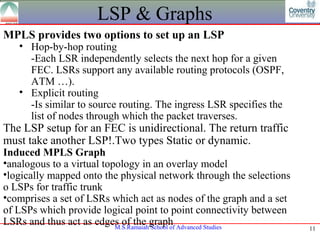
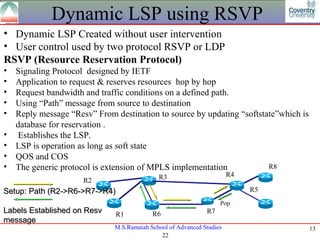
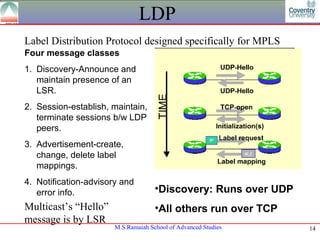
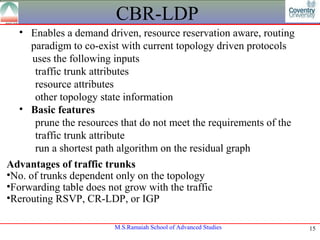
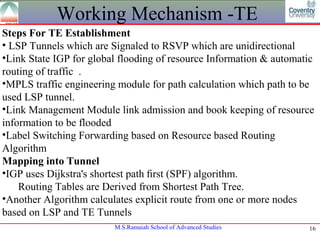
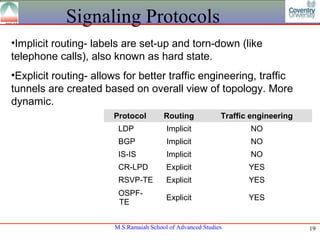
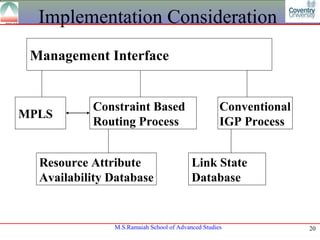
The document provides an overview of MPLS for traffic management. It discusses how MPLS improves on conventional IP networks and ATM by allowing traffic engineering through label switching. Key topics covered include MPLS components, terminology, dynamic LSP setup using RSVP signaling, traffic trunks, and deployment strategies. The goal of MPLS traffic engineering is to increase resource utilization and speed up network convergence.