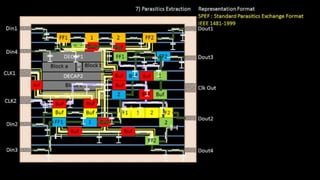
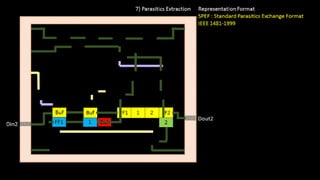
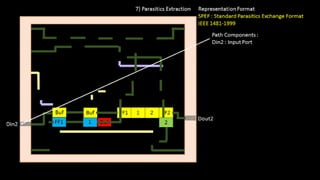
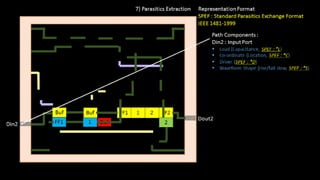
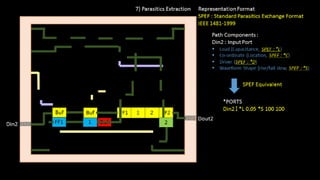
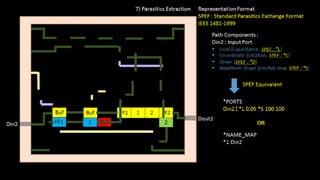
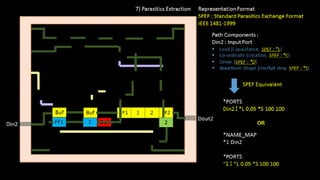
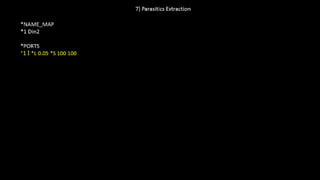
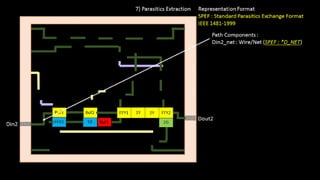
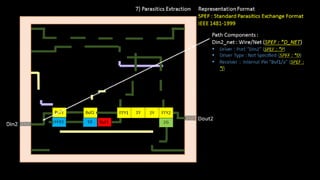
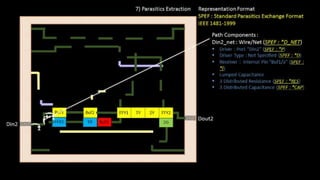
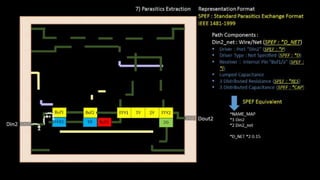
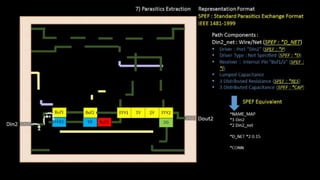
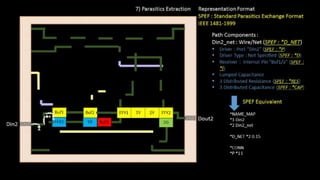
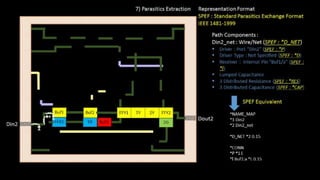
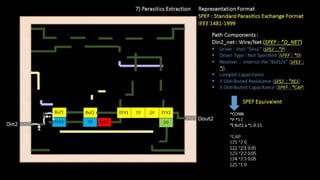
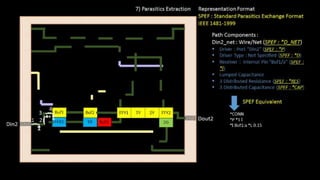
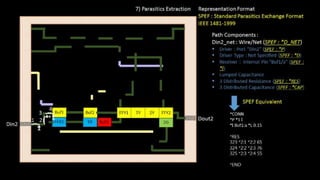
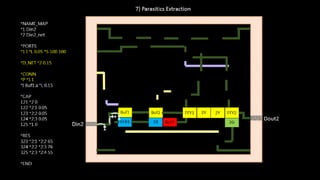
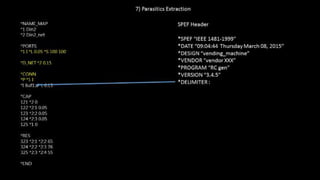
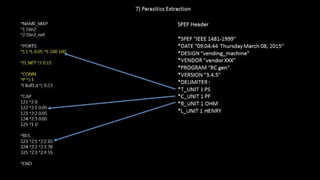
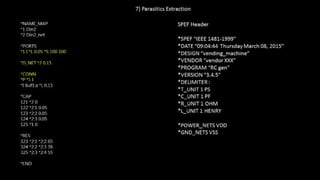
The document discusses the IEEE Standard Package for the Exchange of Product (SPEF) format in electronic design automation, detailing how to create an SPEF file for circuit components, including naming conventions and representation of resistances and capacitances. It explains the concept of name mapping to reduce file size significantly and offers a step-by-step example of constructing an SPEF file for an input port and net. Additionally, the document includes links to related courses for further learning on circuit design and physical design flow.