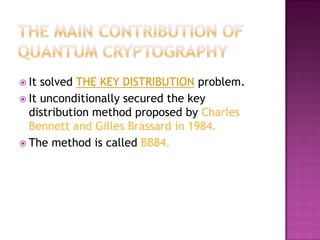
Quantum information theory deals with integrating information theory with quantum mechanics by studying how information can be stored and retrieved from quantum systems. Quantum computing uses quantum physics and quantum bits (qubits) that can exist in superpositions of states to perform computations in parallel and solve problems like factoring prime numbers faster than classical computers. Key challenges for quantum computing include preventing decoherence and protecting fragile quantum states.










![ The best known conventional algorithm
requires the solution time proportional to:
1/ 3 2/3
T (n) exp[ c (ln n ) (ln ln n ) ]
For p & q 65 digits long T(n) is approximately
one month using cluster of workstations
and
For p&q 200 digits long T(n) is astronomical.](https://image.slidesharecdn.com/quantuminformation-120412090119-phpapp02/85/Quantum-Information-Technology-21-320.jpg)
![ In 1994 Peter Shor from the AT&T Bell
Laboratory showed that in principle a
quantum computer could factor a very long
product of primes in seconds.
Shor’s algorithm time computational complexity
is 3
T (n) O [(ln n ) ]](https://image.slidesharecdn.com/quantuminformation-120412090119-phpapp02/85/Quantum-Information-Technology-22-320.jpg)