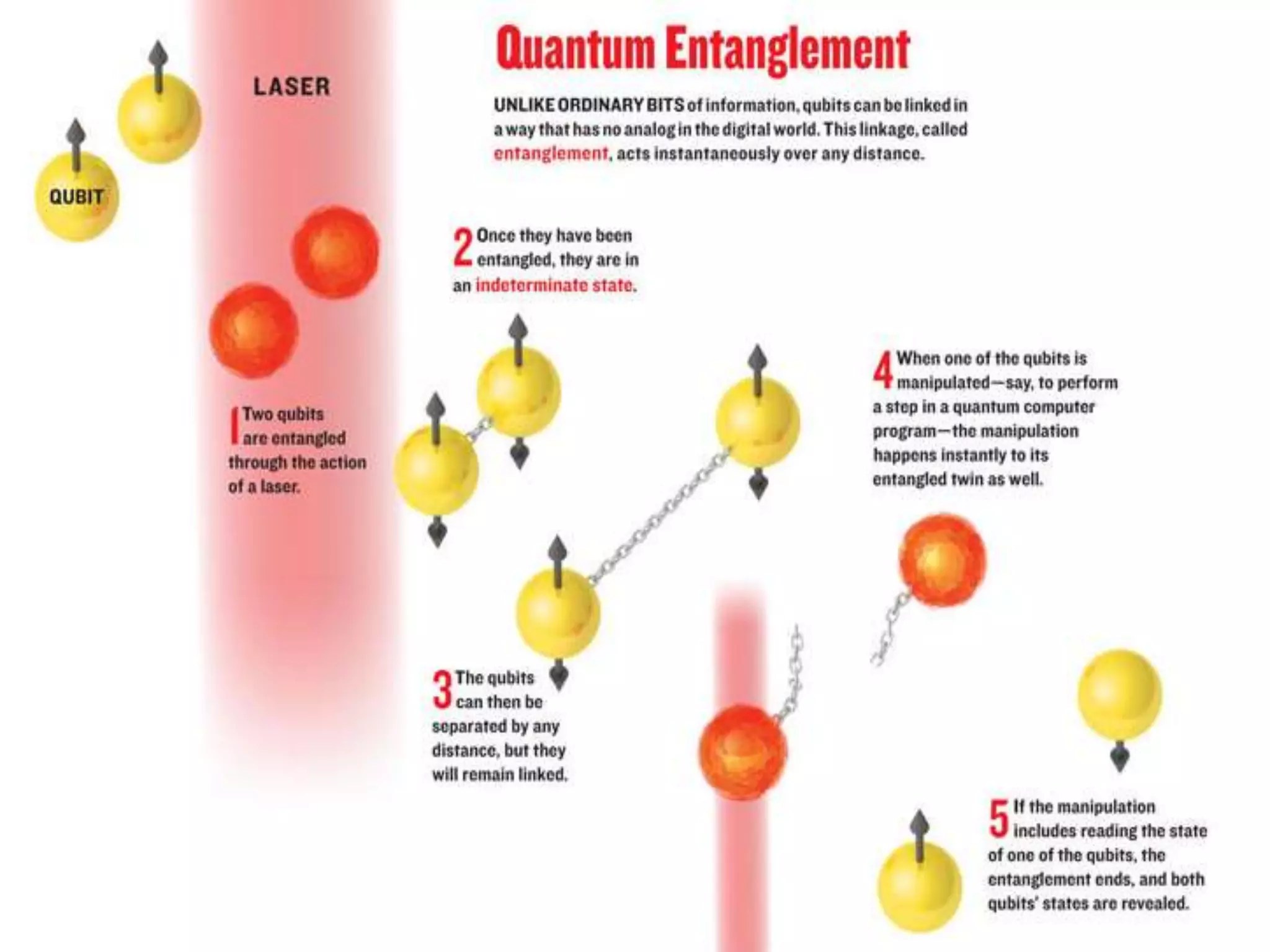
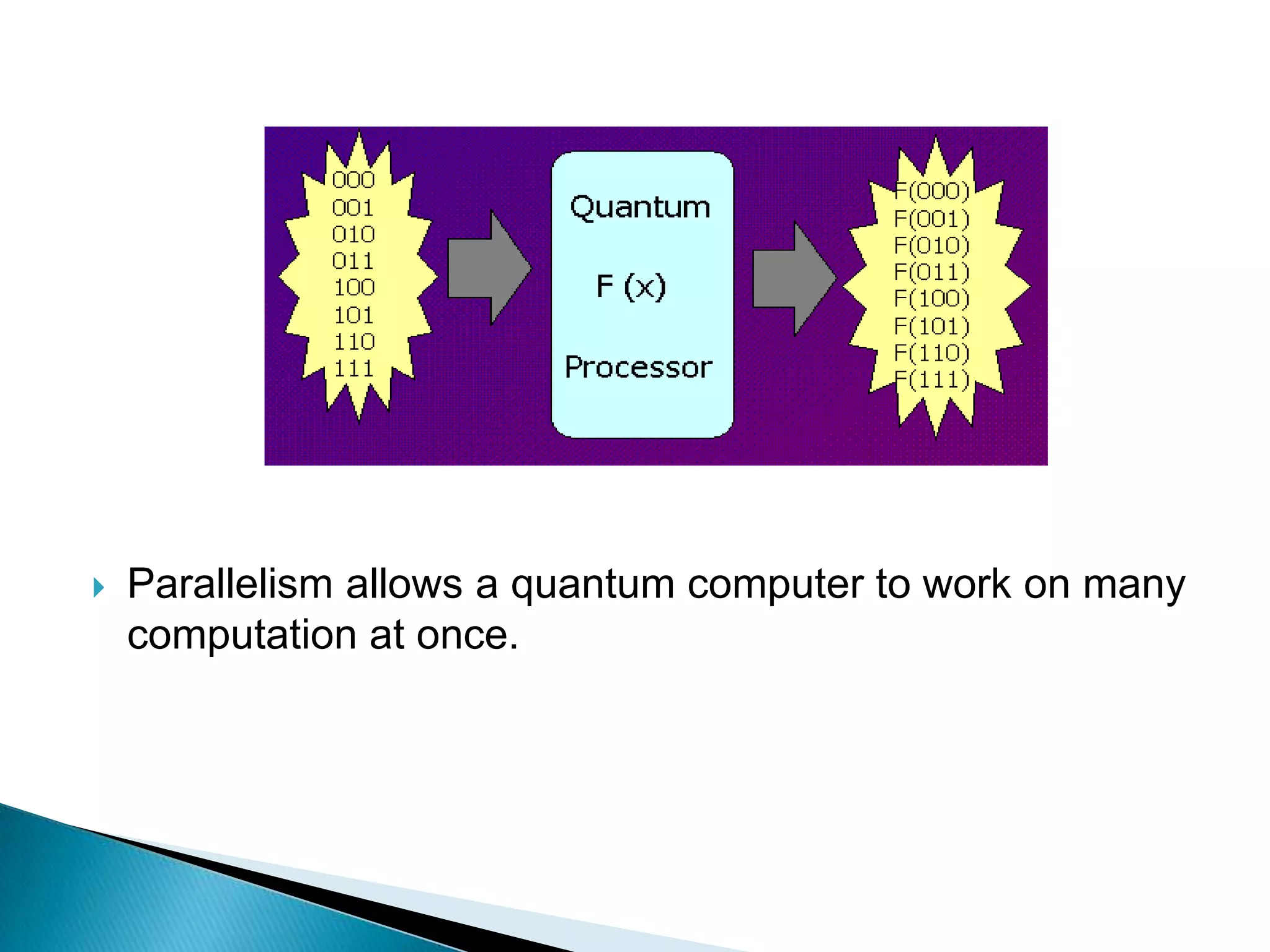
Quantum computers have the potential to solve certain problems much faster than classical computers by exploiting principles of quantum mechanics, such as superposition and entanglement. However, building large-scale, reliable quantum computers faces challenges related to decoherence and controlling quantum systems. Current research aims to develop quantum algorithms and overcome issues in scaling up quantum hardware to perform more complex computations than today's most powerful supercomputers.