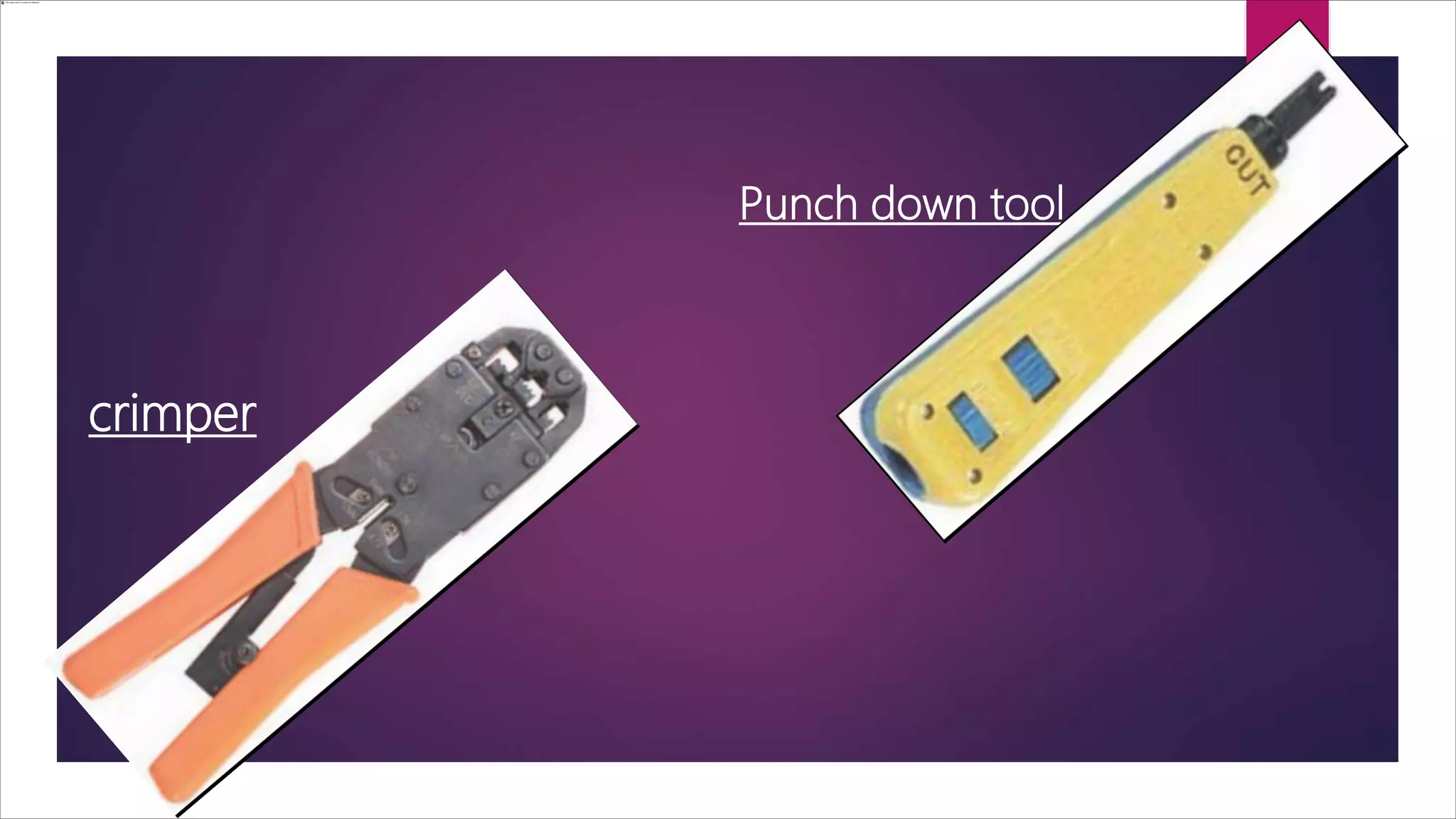
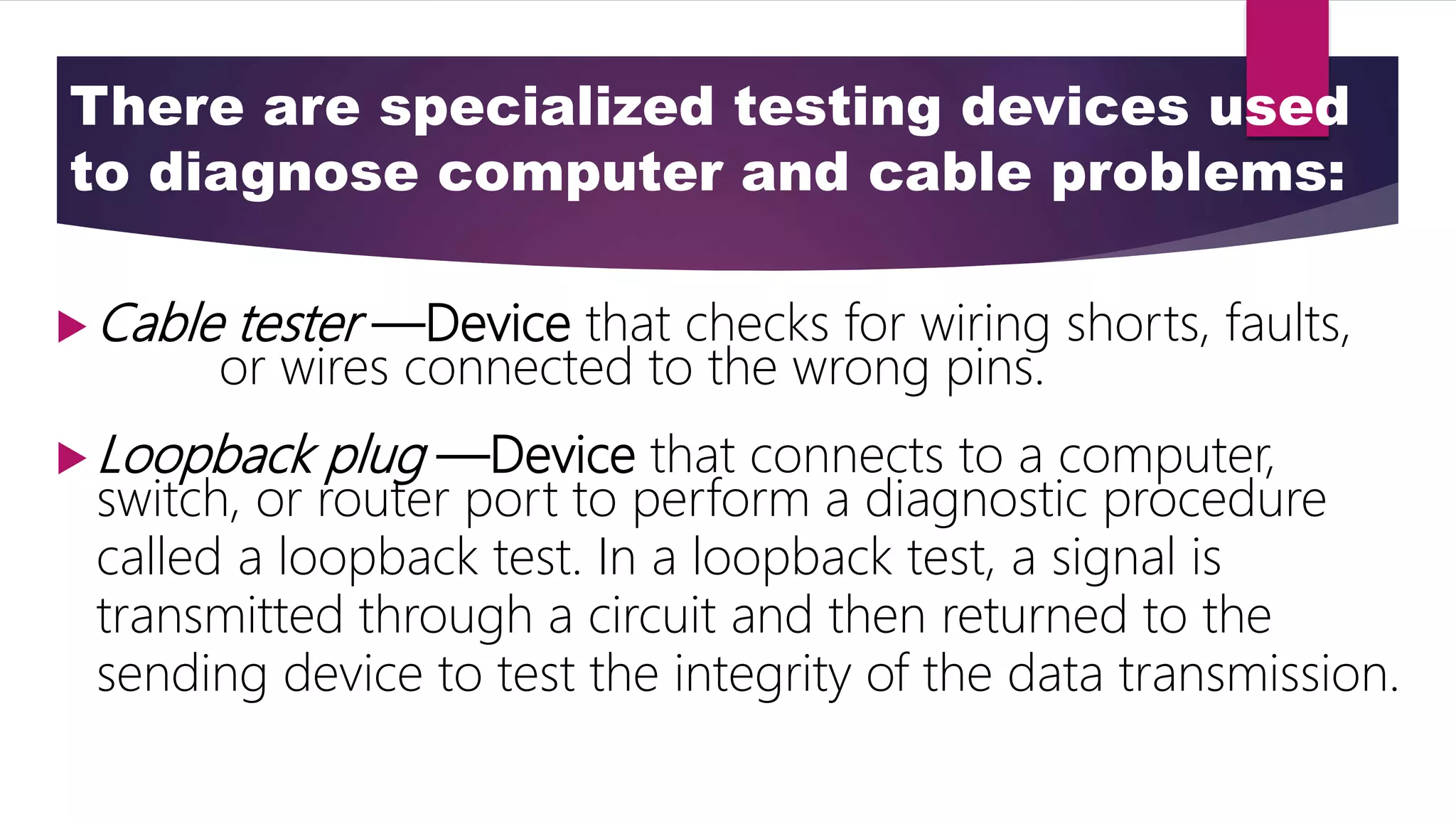
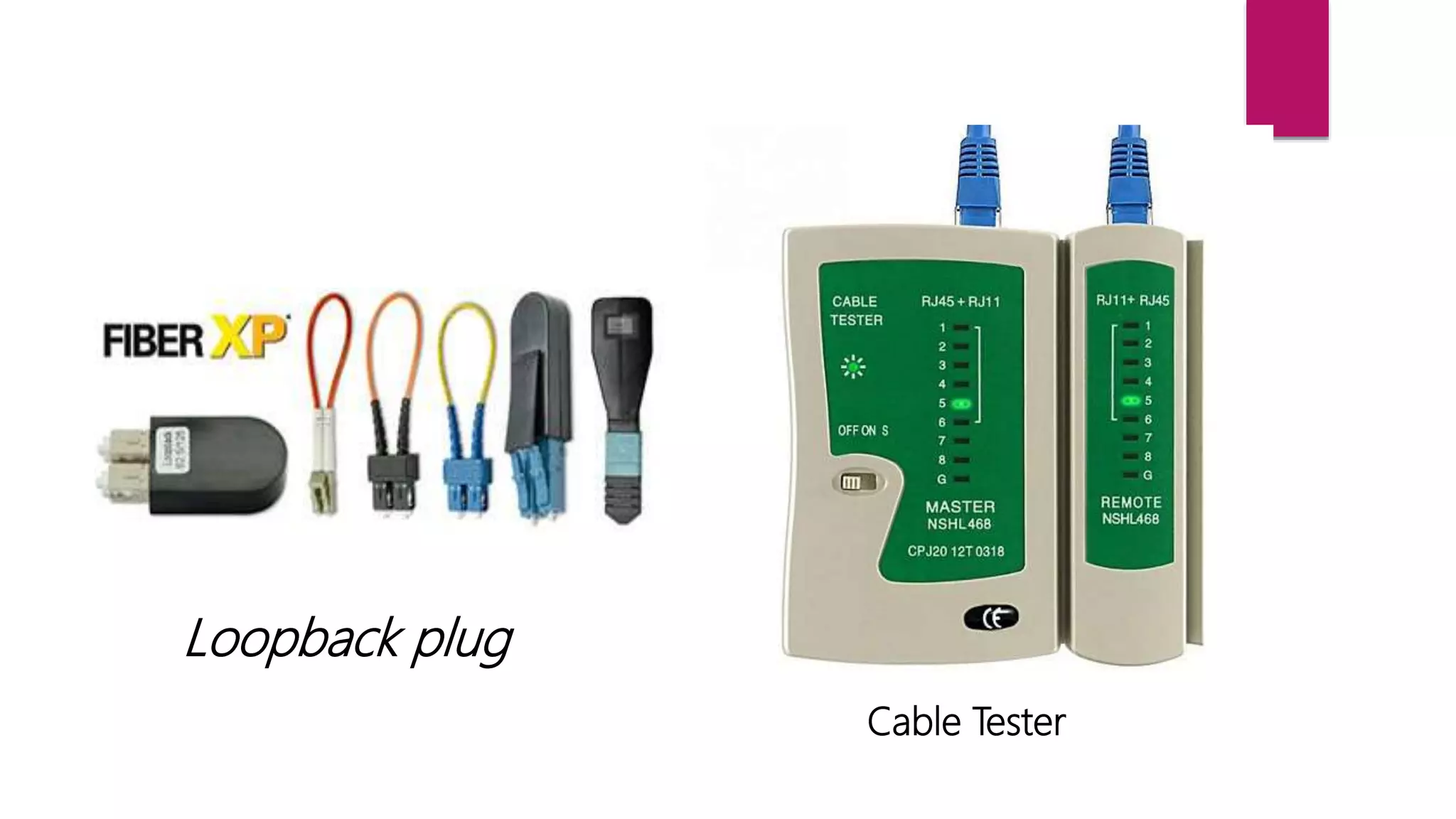
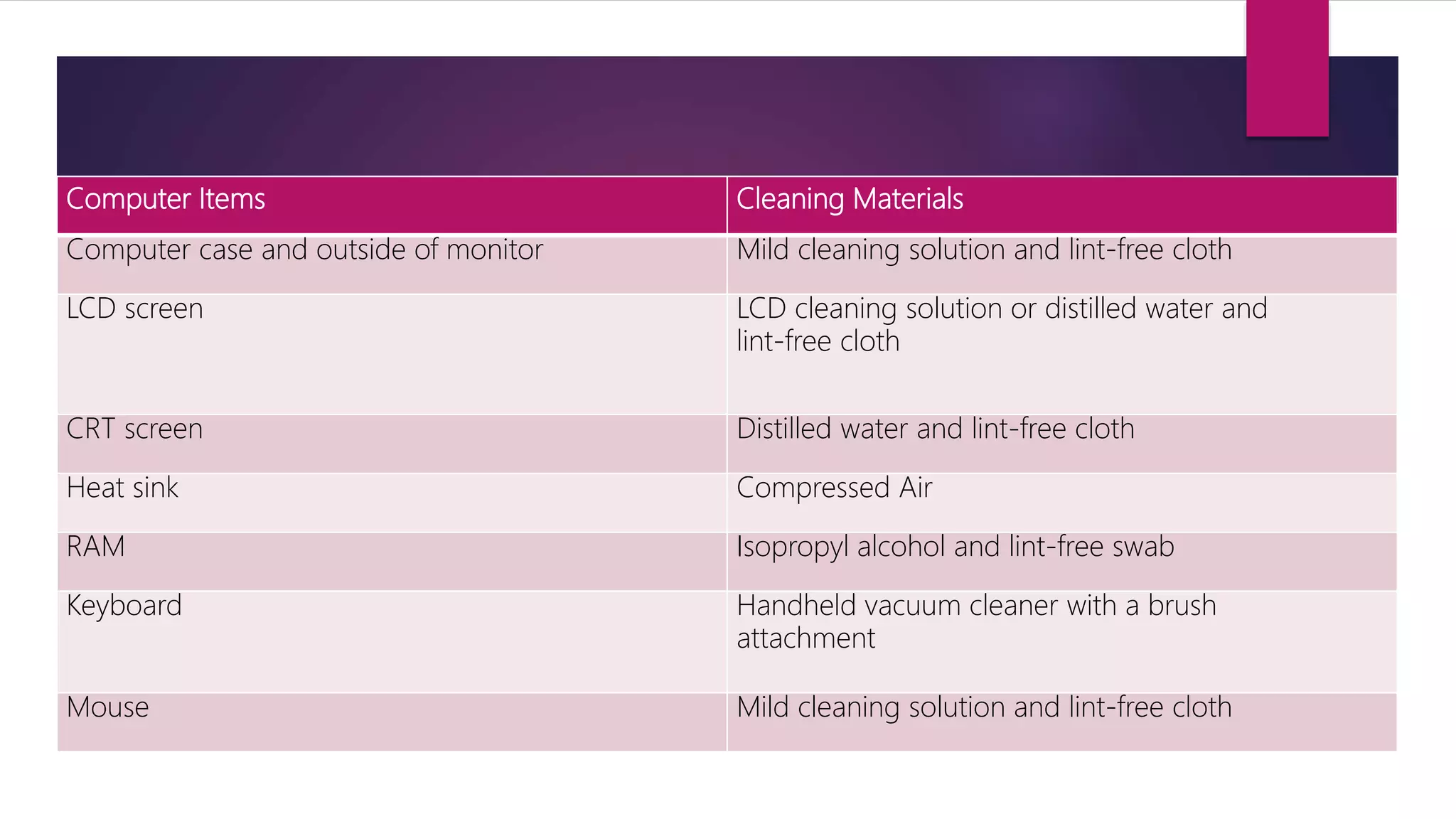
The document outlines proper use and types of hardware tools essential for computer repair, including ESD tools like antistatic wrist straps and mats, cable tools such as crimpers and punch down tools, and diagnostic tools like digital multimeters. It also covers various cleaning and protection software tools that ensure the maintenance and security of computer equipment, alongside organizational and reference tools that support technicians during the repair process. Additionally, it details the importance of proper handling techniques for tools to prevent damage to hardware, including specific instructions on using antistatic devices.