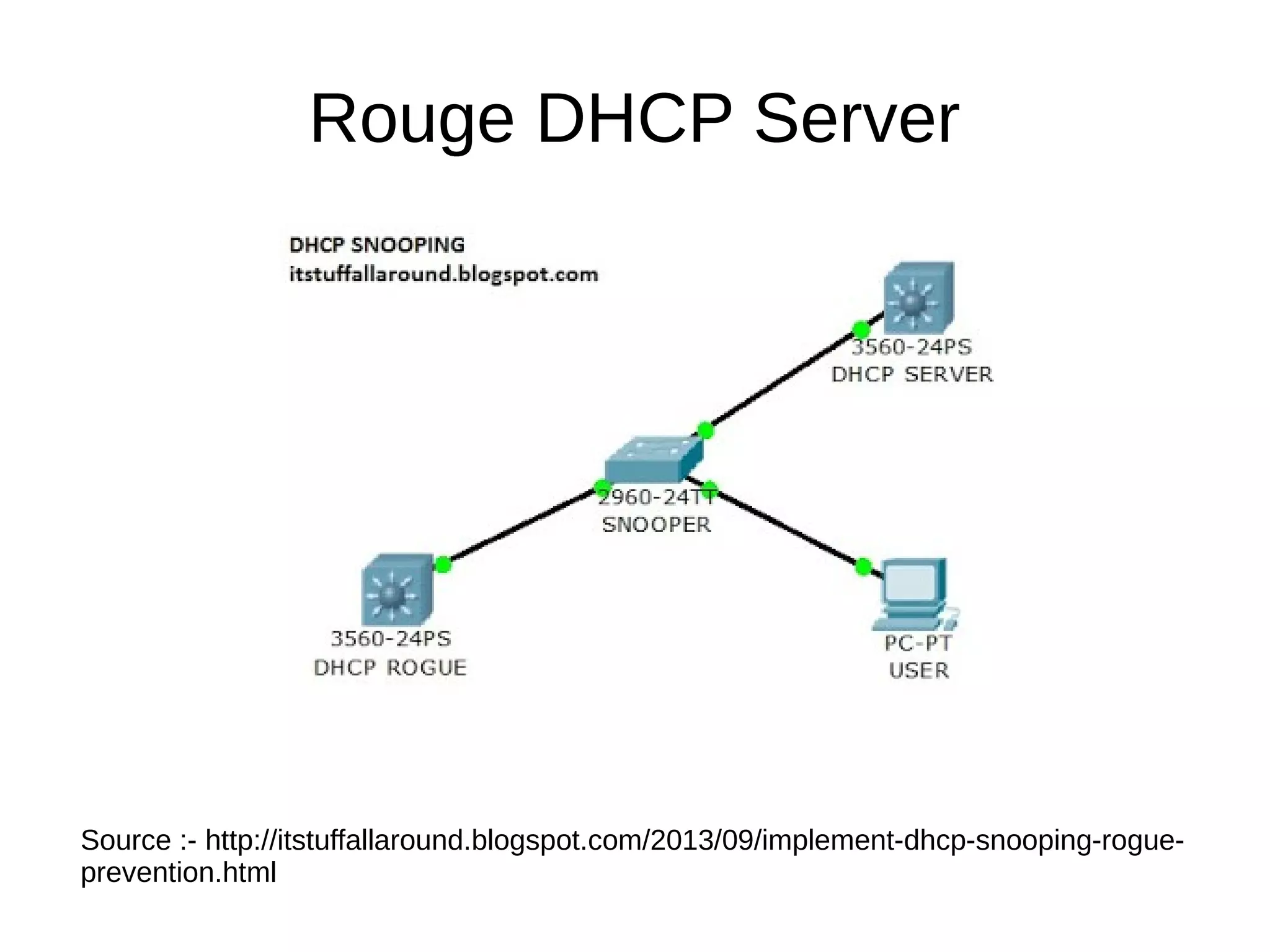
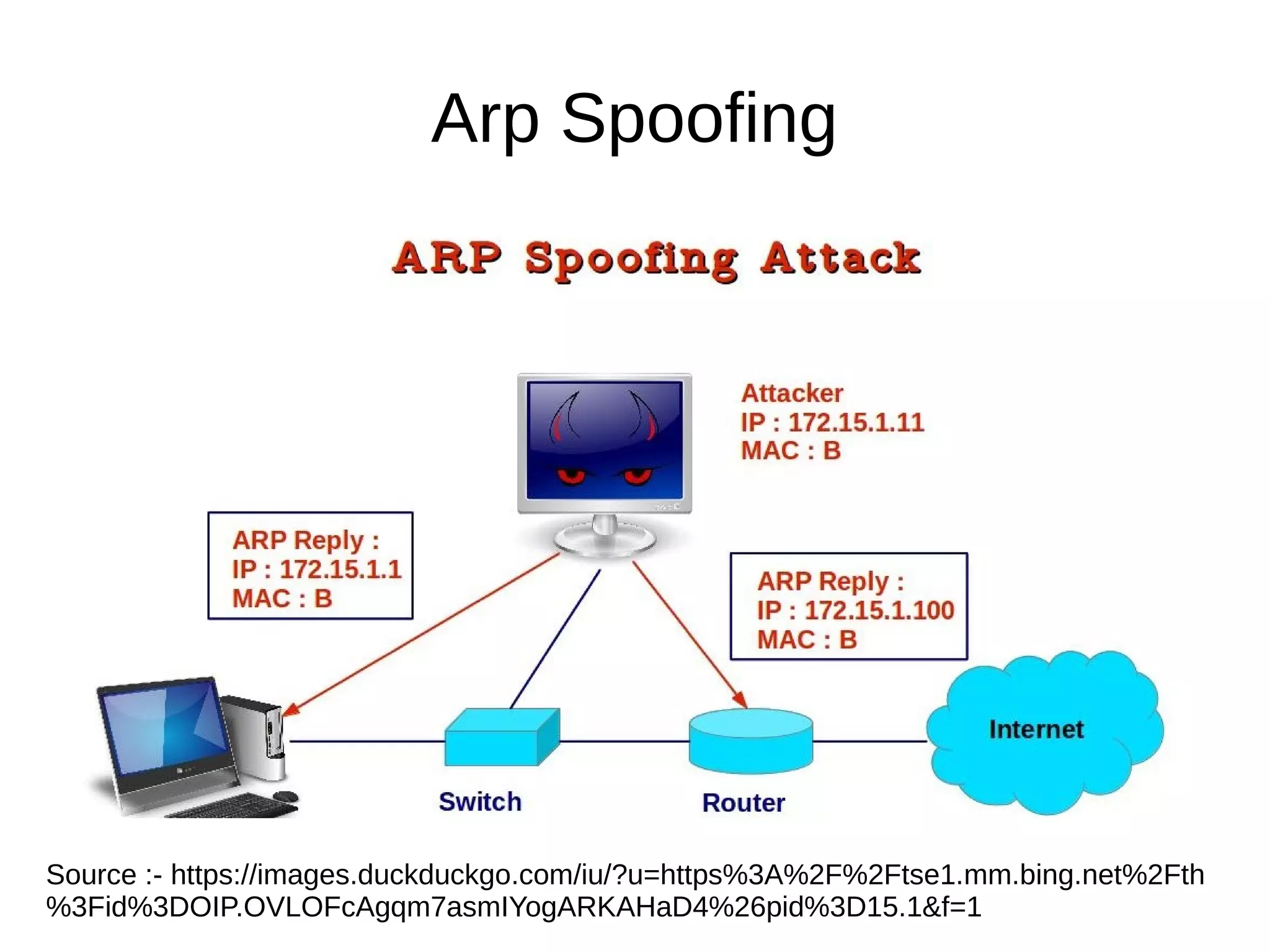
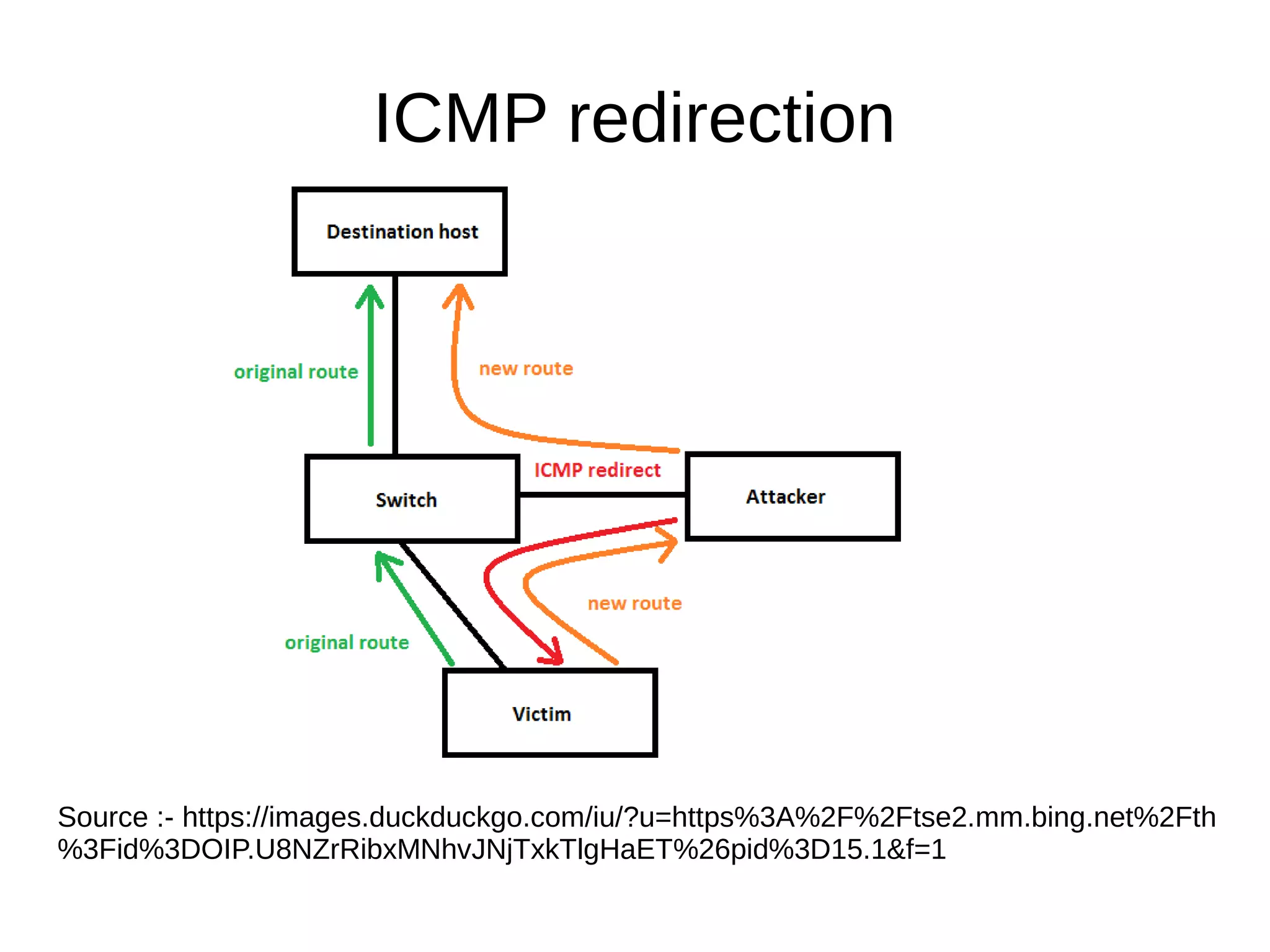
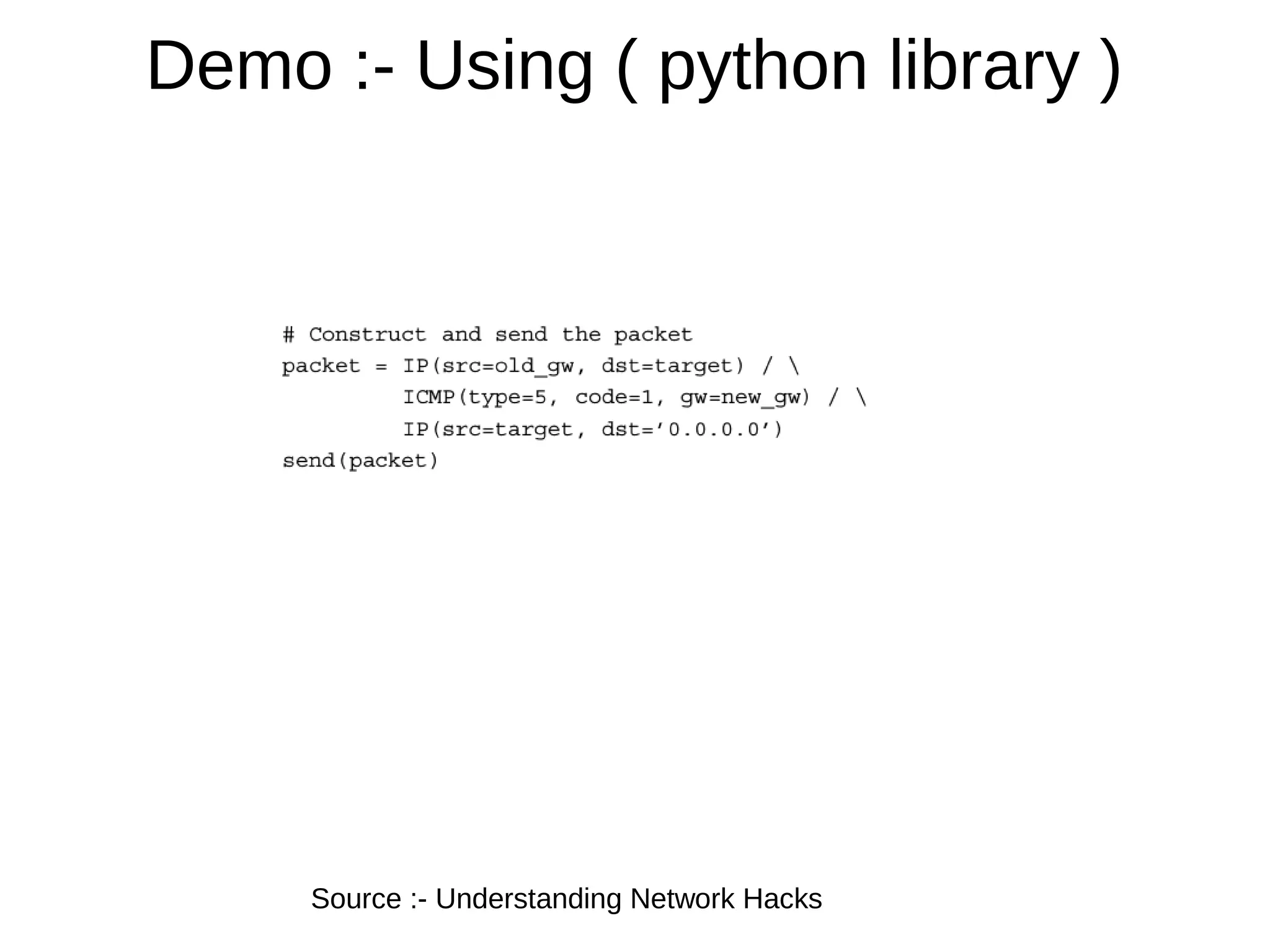
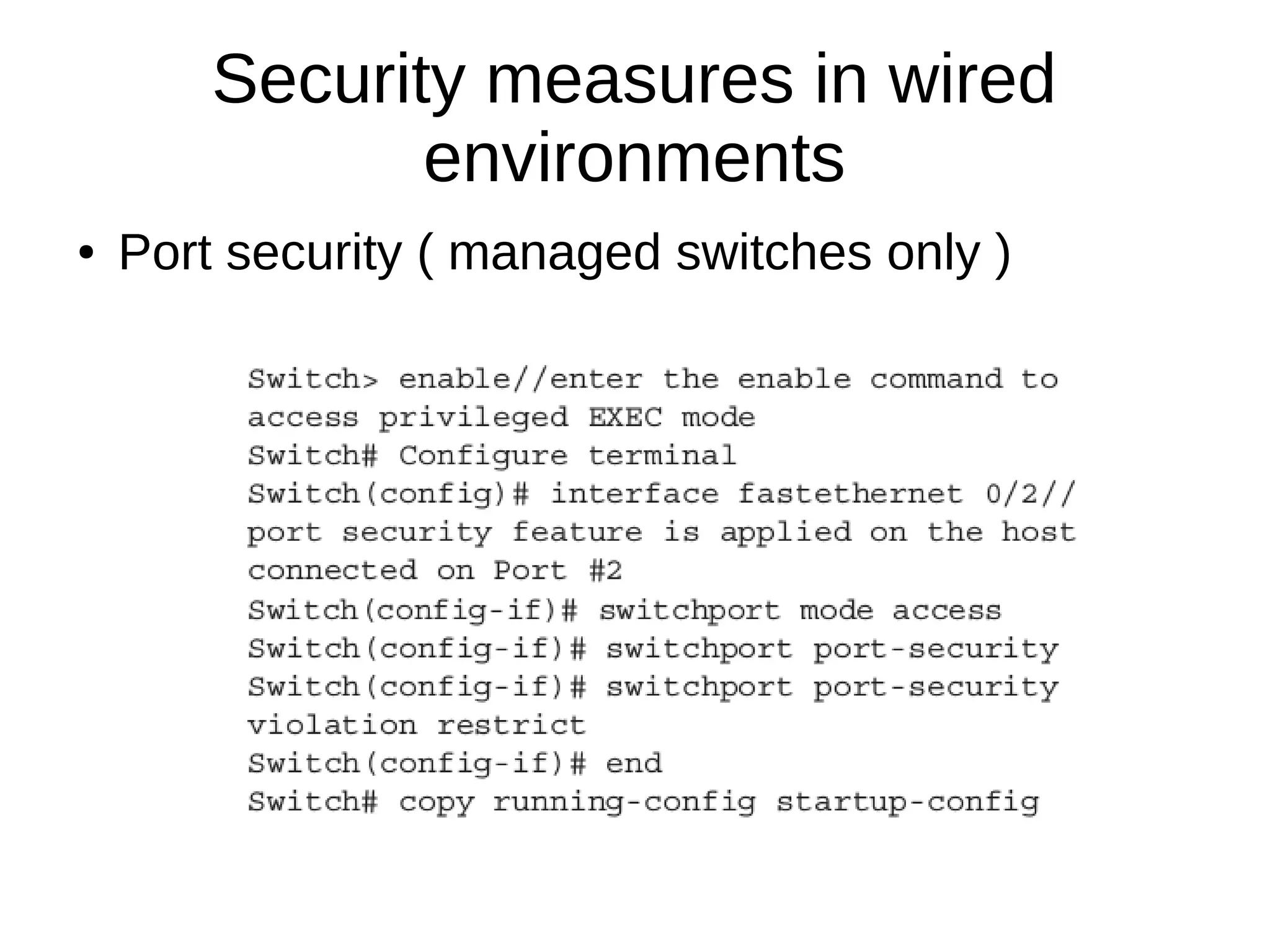
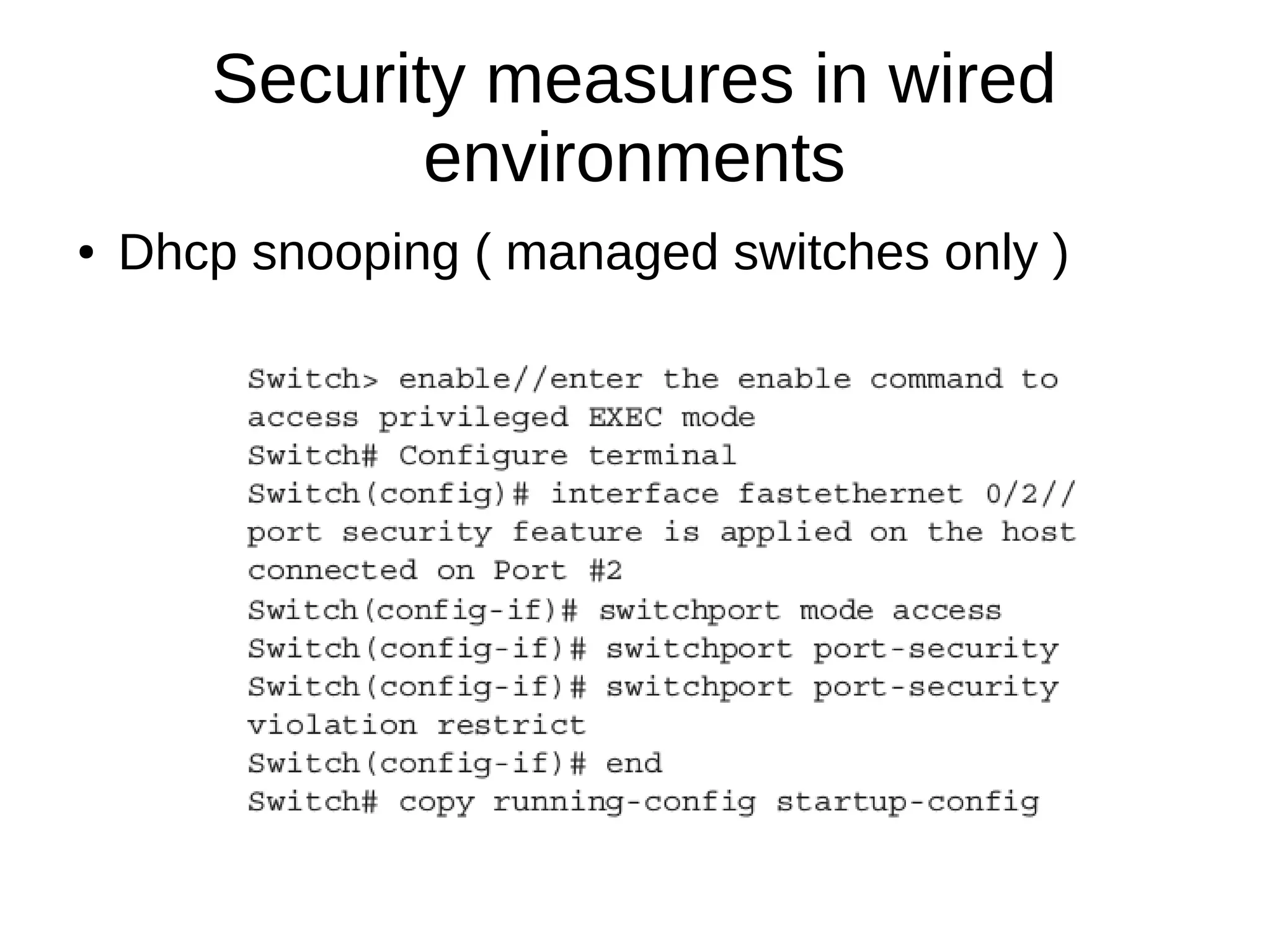
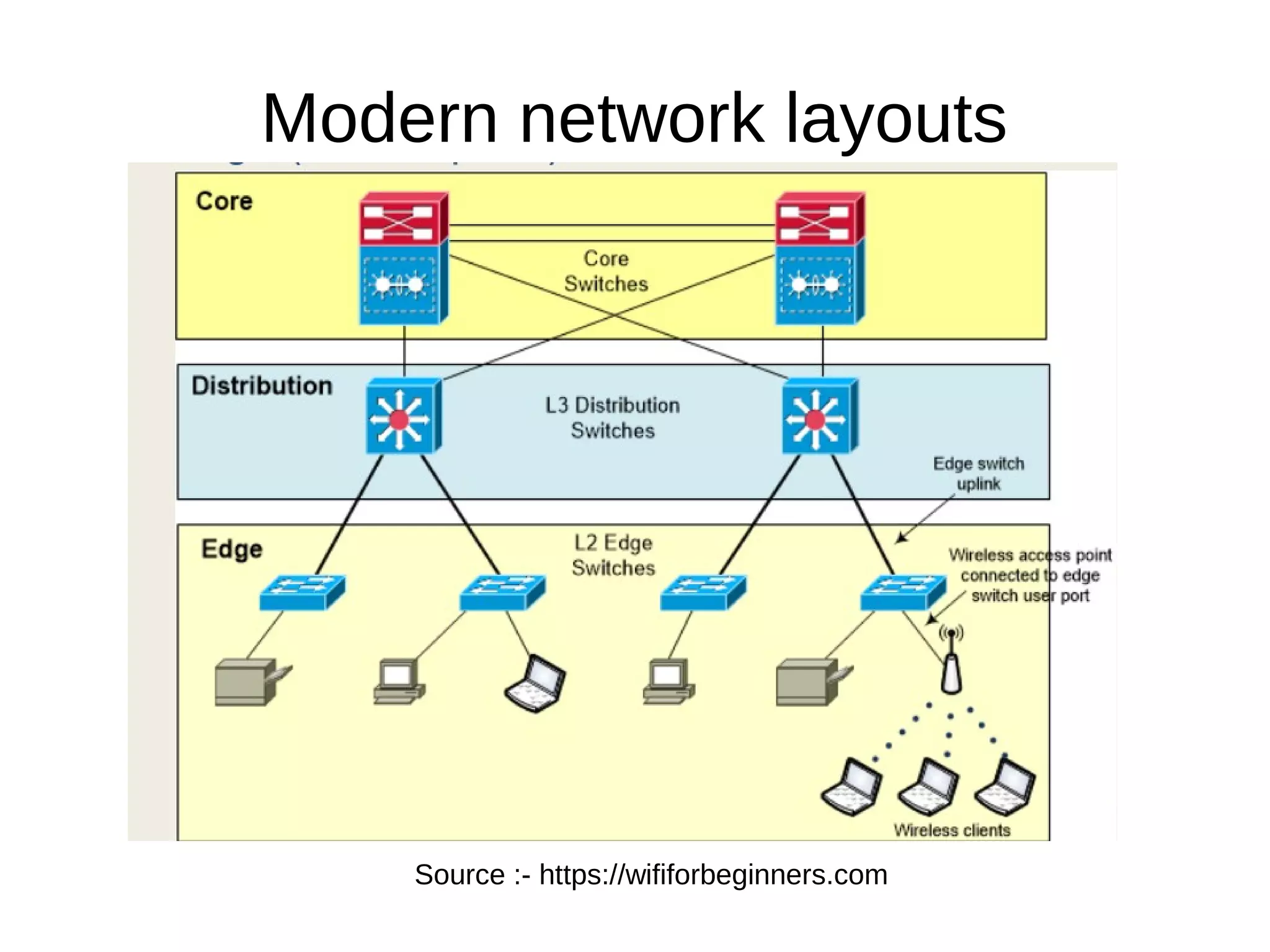
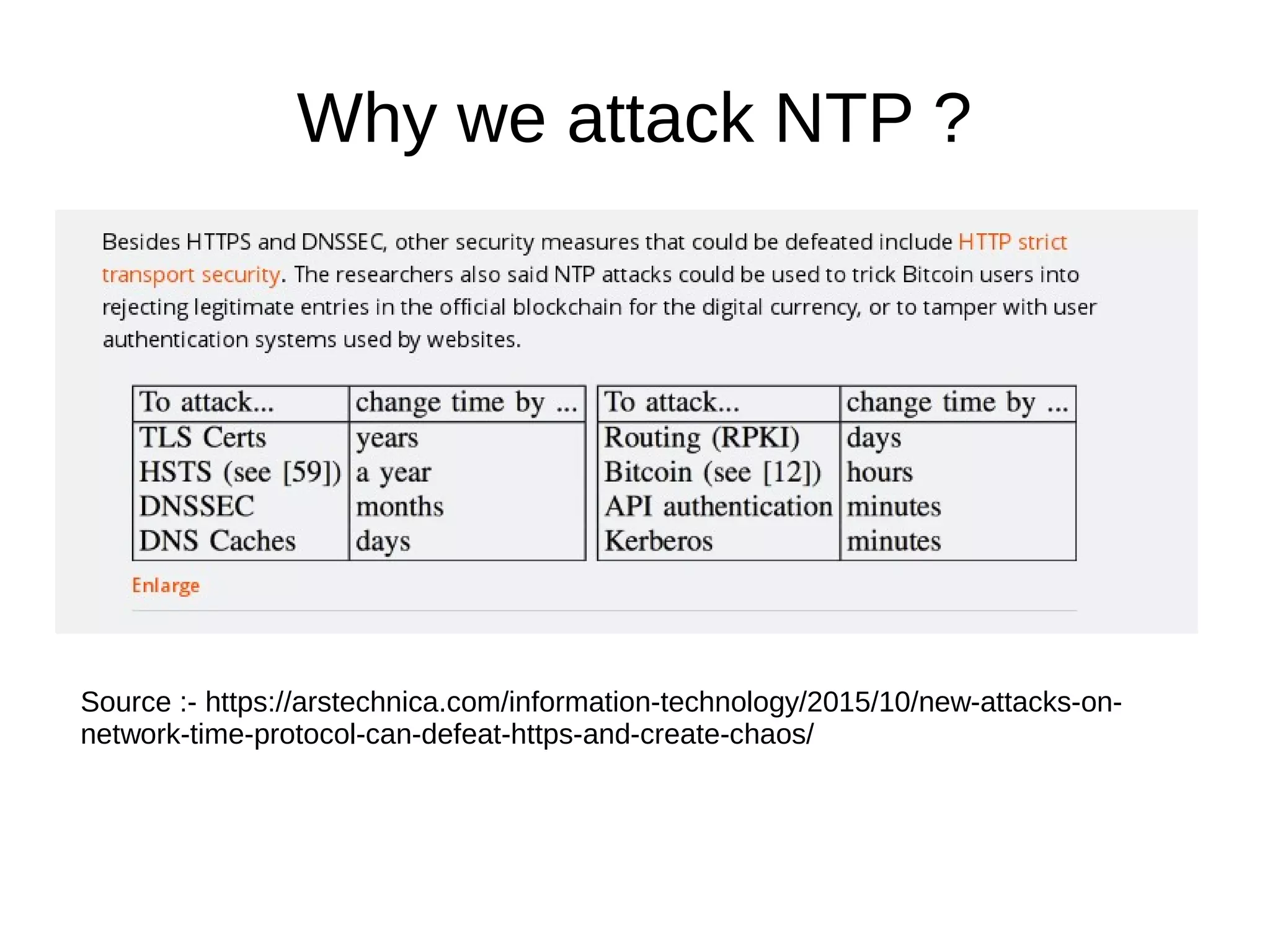
The document discusses various network security threats, specifically focusing on wired and wireless environments, including attacks like rogue DHCP servers, MAC flooding, and packet injection. It highlights the differences between wired and wireless security, emphasizing the vulnerabilities present in wireless networks, such as easy access to monitor traffic and the potential for man-in-the-middle attacks. The conclusion suggests that while wireless networks pose significant security risks, protective measures like WIDS and encryption are essential for safeguarding against attacks.