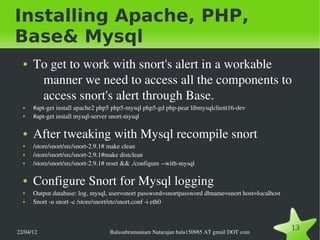
The document provides detailed instructions on installing Snort, an intrusion detection and prevention system, including creating necessary directories, configuring user permissions, and downloading required components and rules. It also covers database setup for logging Snort alerts using MySQL and installing Base for alert management. Lastly, it discusses the process for creating custom Snort rules to monitor specific activities.
![Snort Installation & Rule Creation
● By Balasubramaniam Natarajan
● bala150985 AT gmail [DOT] com
● www.etutorshop.com/moodle](https://image.slidesharecdn.com/snort-120422021030-phpapp01/85/Snort-1-320.jpg)