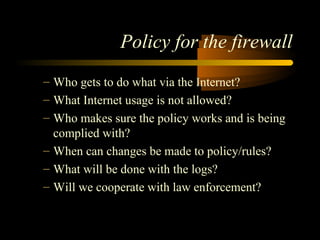
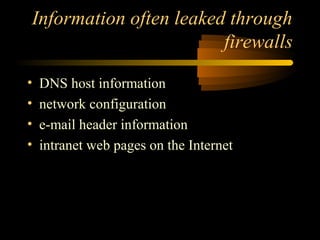
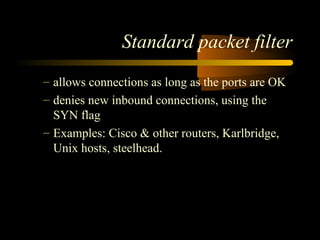
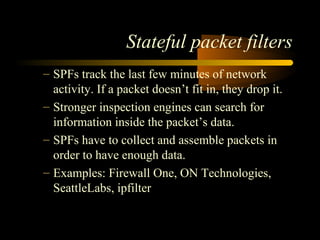
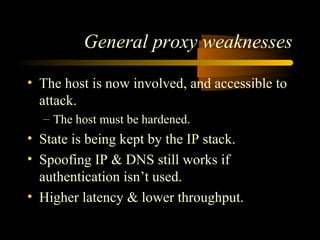
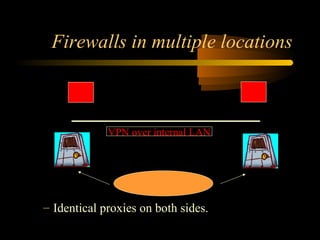
This document discusses firewalls and network security. It begins by outlining common firewall topics and risks to networks like data theft and denial of service attacks. It then examines why firewalls are needed to secure networks and assets. The document outlines different types of firewalls like packet filters, proxy firewalls, and network address translation. It discusses strengths and weaknesses of each approach. Finally, it covers best practices for firewall deployment, configuration, auditing and trends in firewall technologies.