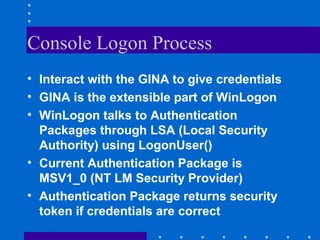
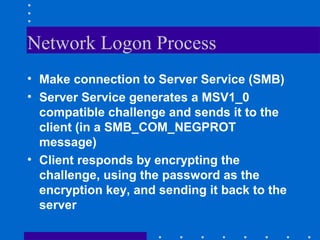
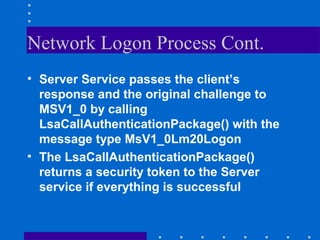
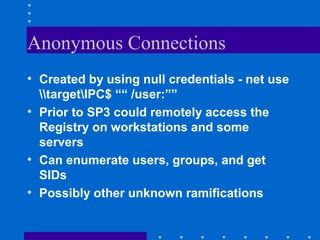
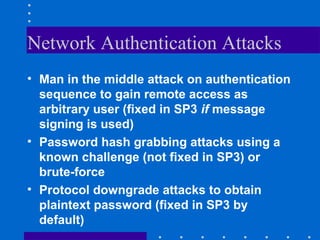
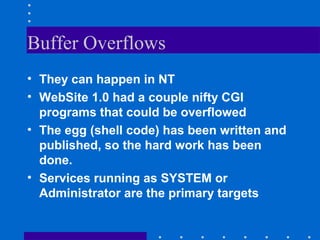
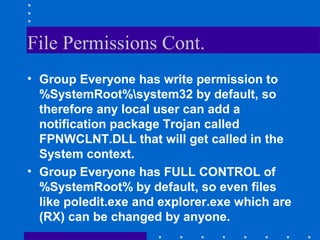
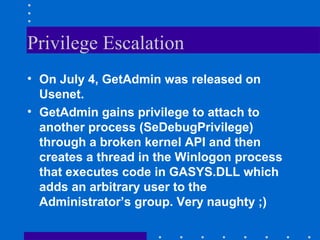
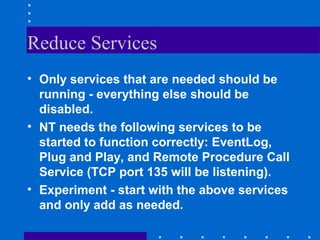
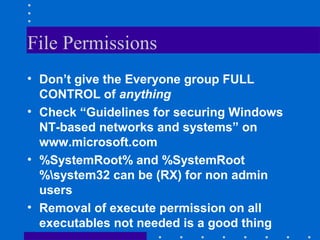
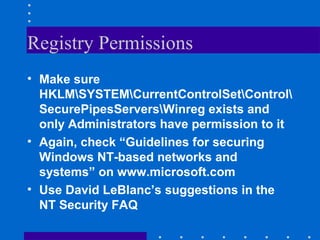
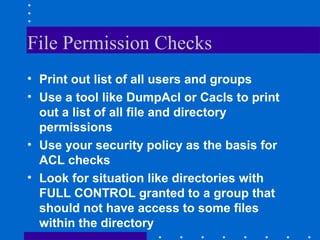
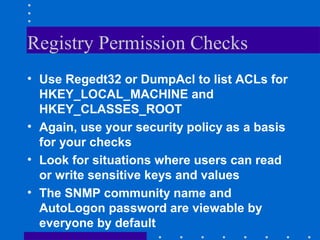
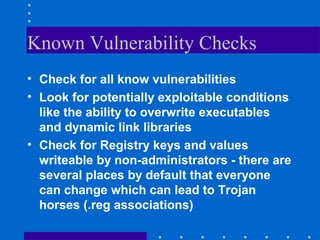
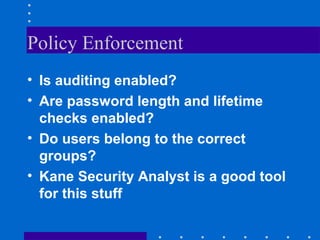
- The document discusses securing Windows NT systems by reviewing the NT security architecture, known vulnerabilities, and methods for exploiting them. It provides guidance on hardening NT security through measures like reducing unnecessary services, restricting file and registry permissions, and enforcing stronger passwords. System administrators can assess their security posture using various scanning and auditing tools to detect vulnerabilities, non-compliant configurations, and potential security breaches.