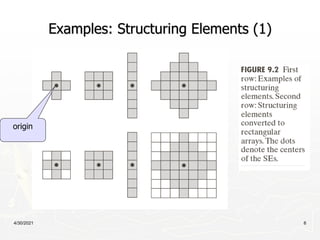
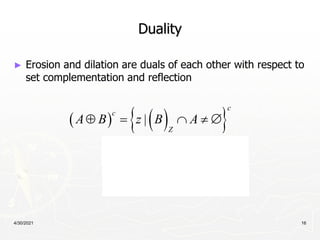
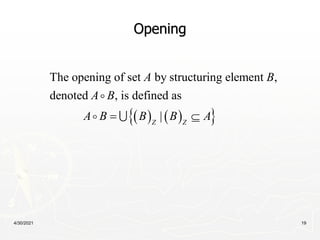
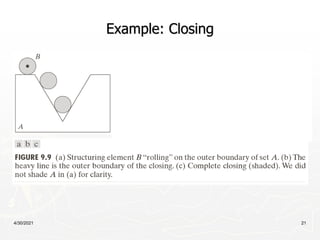
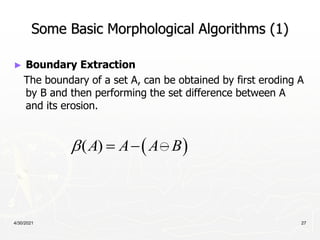
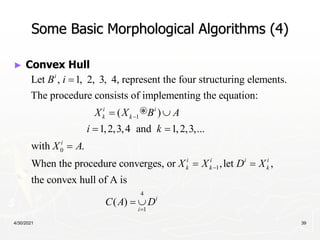
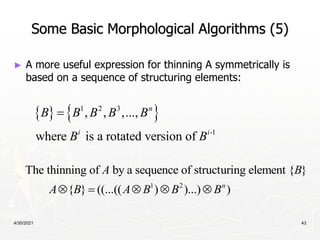
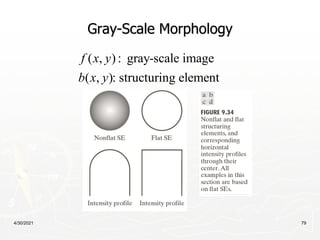
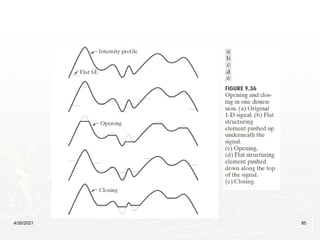
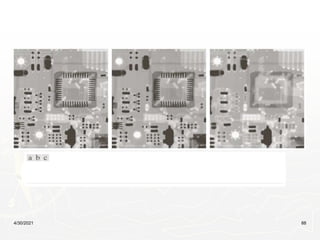
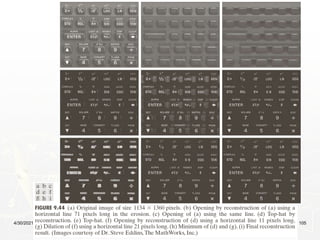
This document provides an overview of morphological image processing techniques. It begins with introductions to morphology, structuring elements, erosion, dilation, opening, closing, and hit-or-miss transformations. Examples are given for each. The document then describes basic morphological algorithms for boundary extraction, hole filling, connected component extraction, convex hulls, thinning, thickening, and skeletonization. Pruning, morphological reconstruction, and geodesic dilation are also summarized. Overall, the document covers fundamental concepts and operations in morphological image processing.