This document provides an overview of Mobile Number Portability (MNP), explaining its functionality, types, implementation processes, and benefits for both subscribers and telecom operators. It details the porting process, routing mechanisms, and the evolution of MNP in various countries, particularly focusing on its launch in India. The article concludes with future considerations and the importance of a centralized implementation approach to enhance customer service and promote competition among service providers.




![History
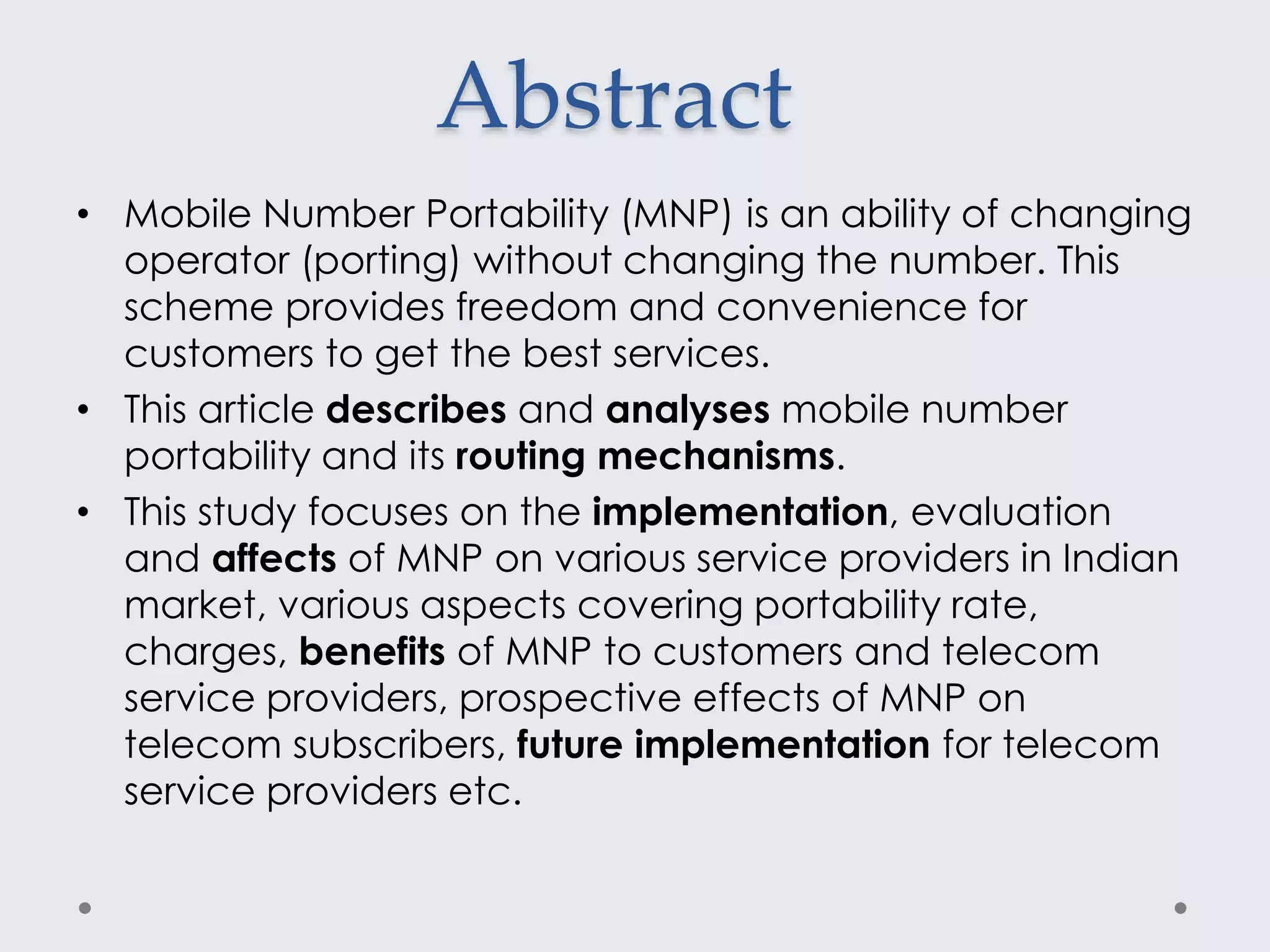
Country Year of implementation
Singapore June 13,1997
Hong Kong March 01,1999
Australia September 25,2001
Italy April 01,2002
Germany November 01,2002
France June 30,2003
USA November 24,2003
Saudi Arabia July 08,2006
South Africa November 10,2006
Canada March 14,2007
Pakistan March 23,2007
New Zealand April 01,2007
Mexico July 05,2008
Brazil September 01,2008
India January 20,2011(MNP)
[ 3rd July, 2015 (NMNP)]](https://image.slidesharecdn.com/mobilenumberportability-151006235452-lva1-app6892/75/Mobile-number-portability-with-IEEE-Material-6-2048.jpg)


























