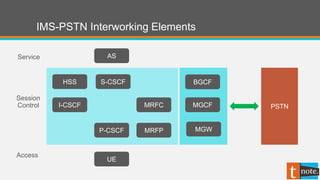
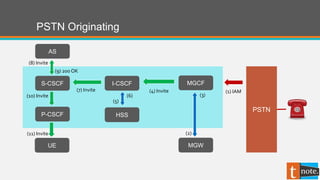
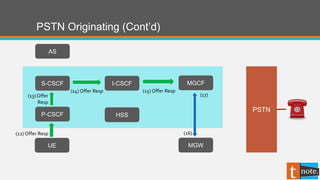
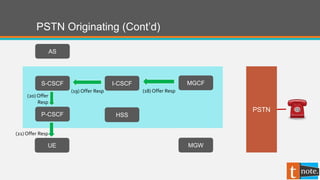
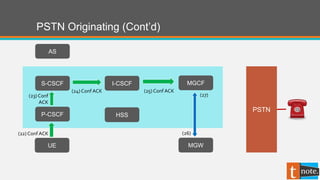
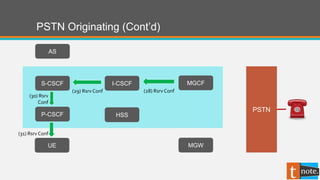
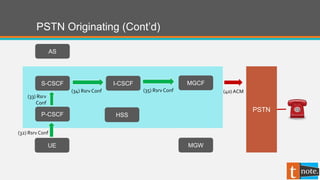
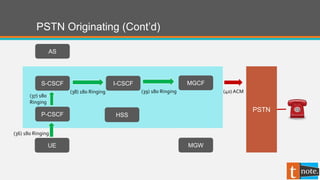
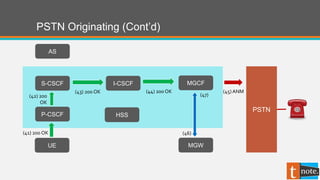
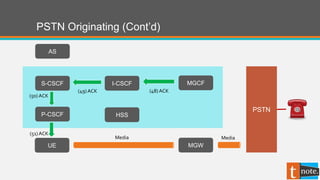
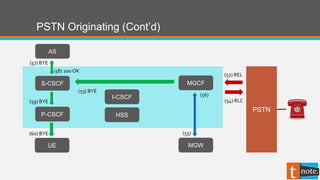
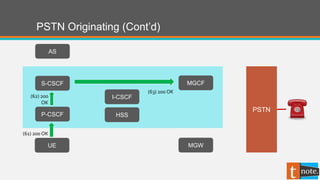
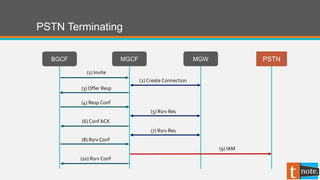
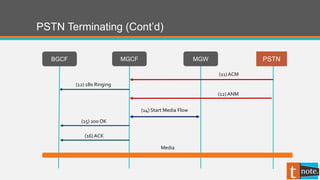
The document describes the call flow process for interworking between an IP Multimedia Subsystem (IMS) network and a public switched telephone network (PSTN). It involves elements like the P-CSCF, I-CSCF, S-CSCF, HSS, MGCF, and MGW. The call flow shows the signaling exchanges between these elements for originating and terminating call scenarios between the IMS and PSTN networks.