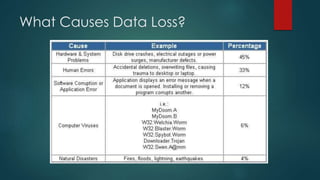
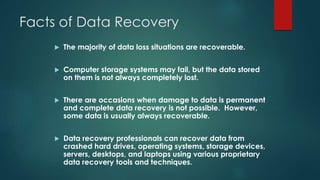
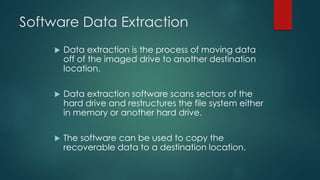
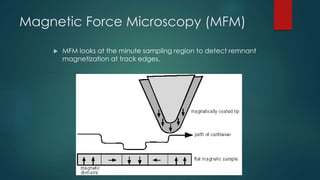
Data recovery involves retrieving deleted or inaccessible data from storage media due to various causes like hardware failure, human error, or natural disasters. Various techniques, including software-based recovery and advanced microscopy methods, can help recover data, though not all situations are recoverable. Employing professional data recovery services can significantly enhance the chances of recovering lost data.