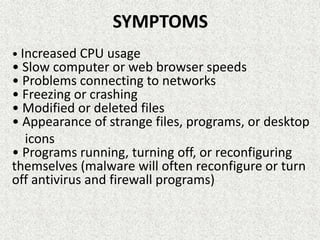
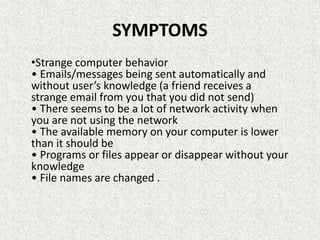
Malware can spread in several ways, including through social networks, pirated software, removable media, emails, and websites. Once activated, malware can cause damages such as data loss by deleting files, account theft by stealing login credentials, and turning computers into bots that hackers can use for password cracking or spam. Common types of malware include viruses, Trojan horses, worms, and remote access Trojans. Symptoms of infection may include increased CPU usage, slow performance, and strange computer behaviors.