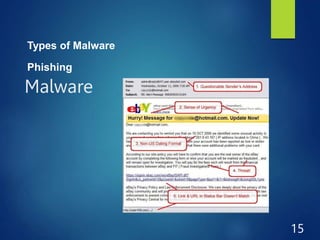
Malware comes in many forms and can damage computers in several ways. It is designed to spread without permission and perform unwanted tasks. Common types of malware include viruses, trojans, worms, spyware, and ransomware. Malware spreads through emails, websites, removable drives, and social networks. It can steal personal information, encrypt files until payment is made, and turn computers into bots. Users should protect themselves by installing antivirus software, practicing caution online, and scanning for malware regularly.