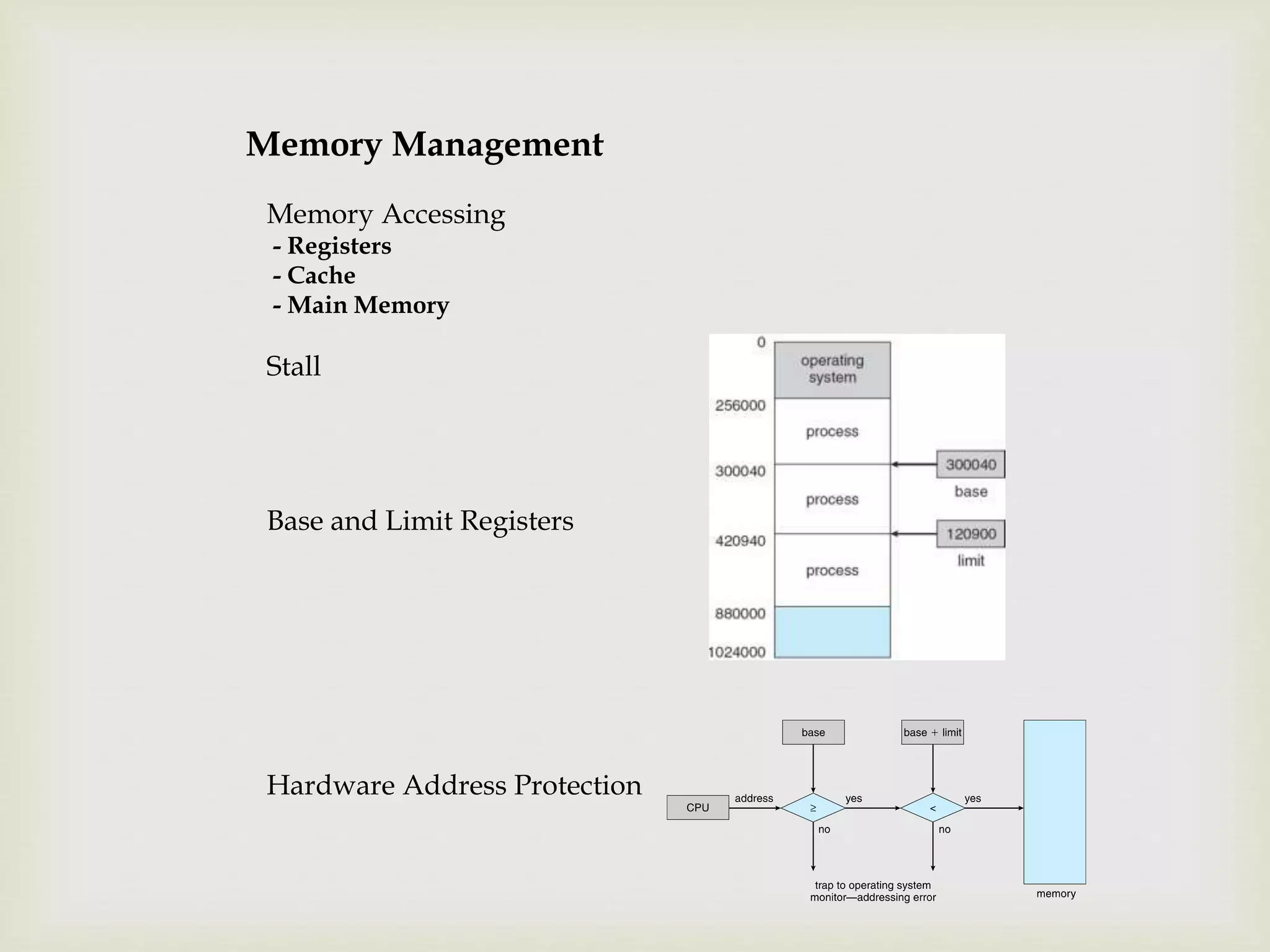
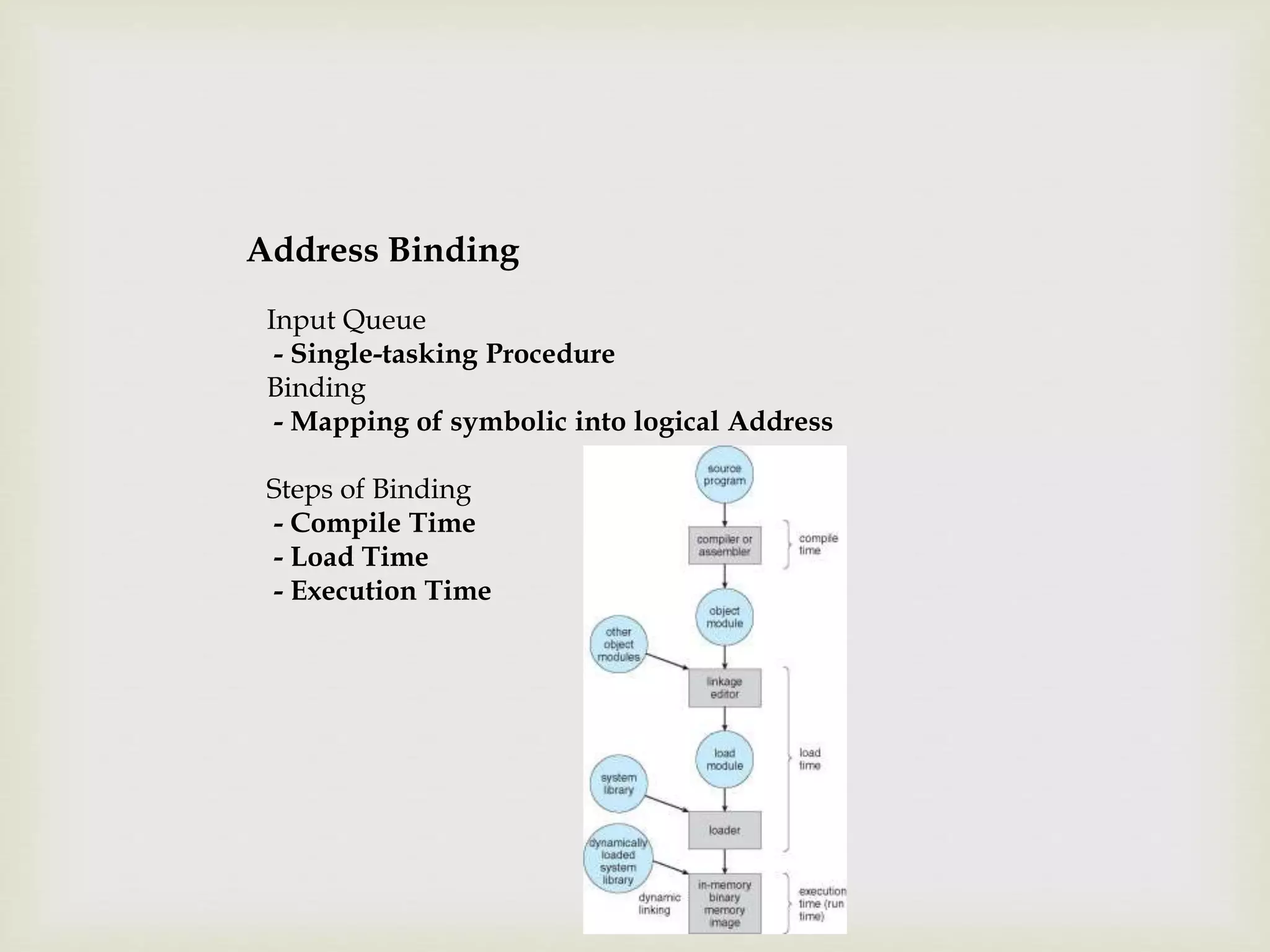
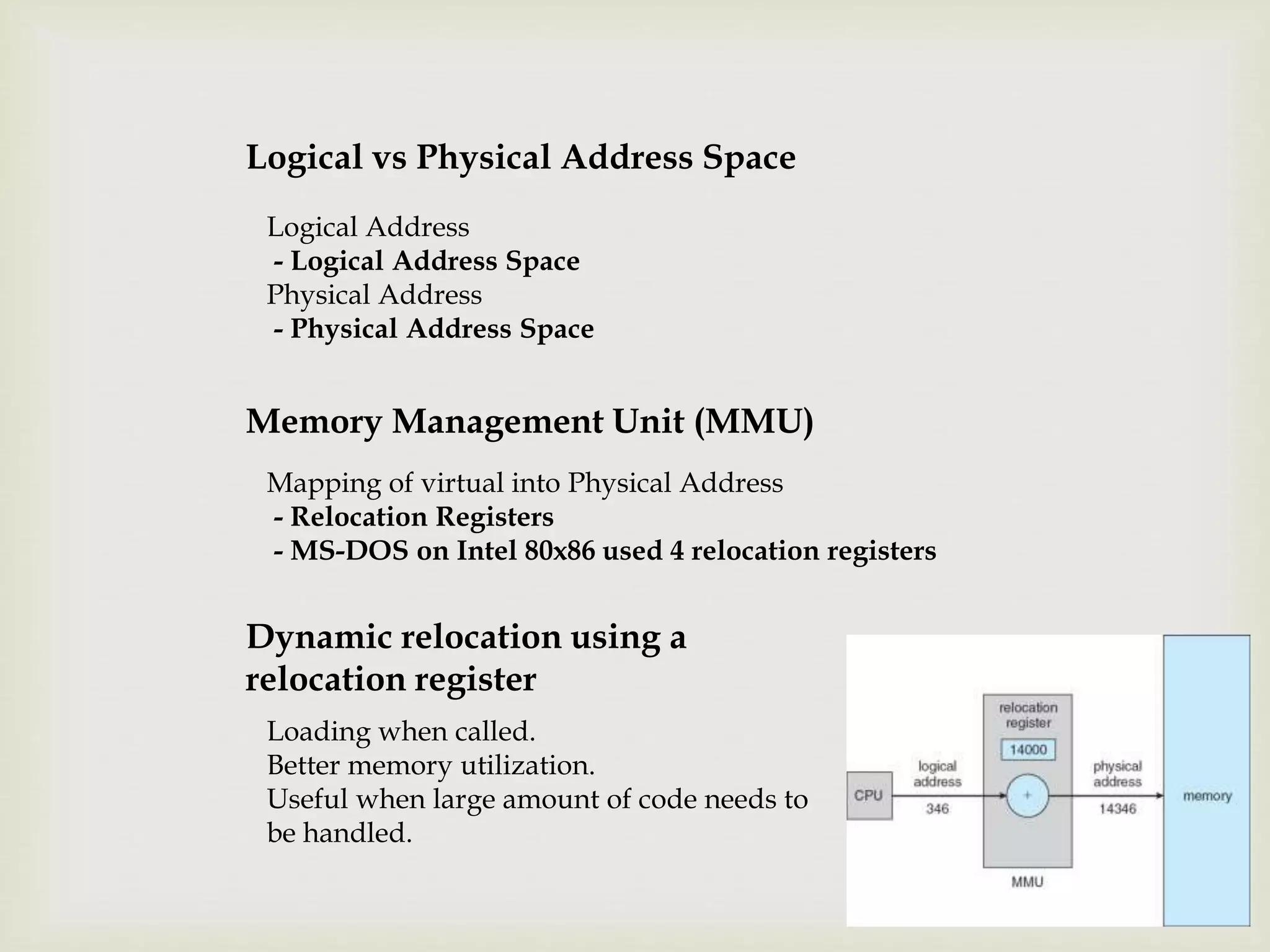
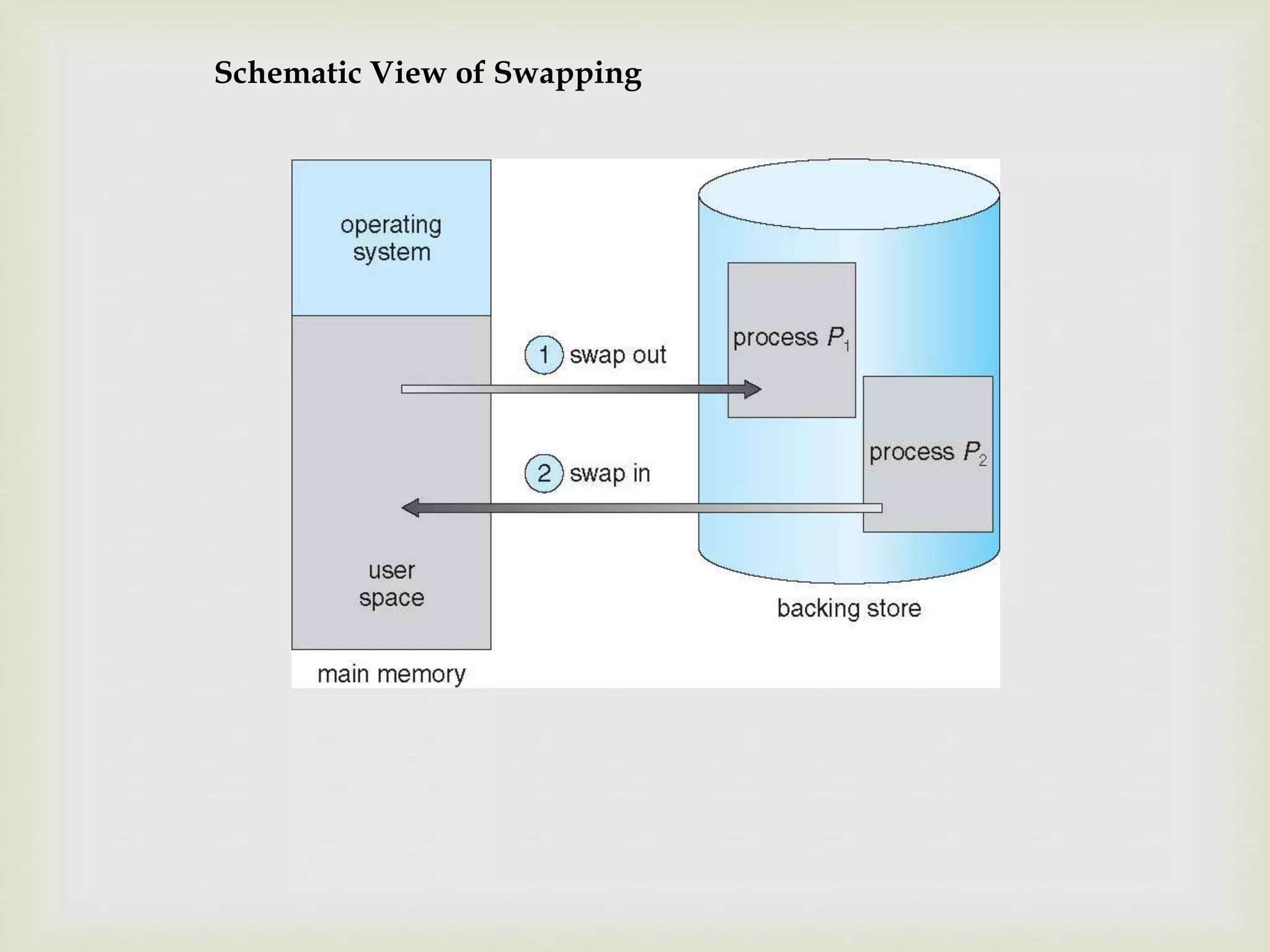
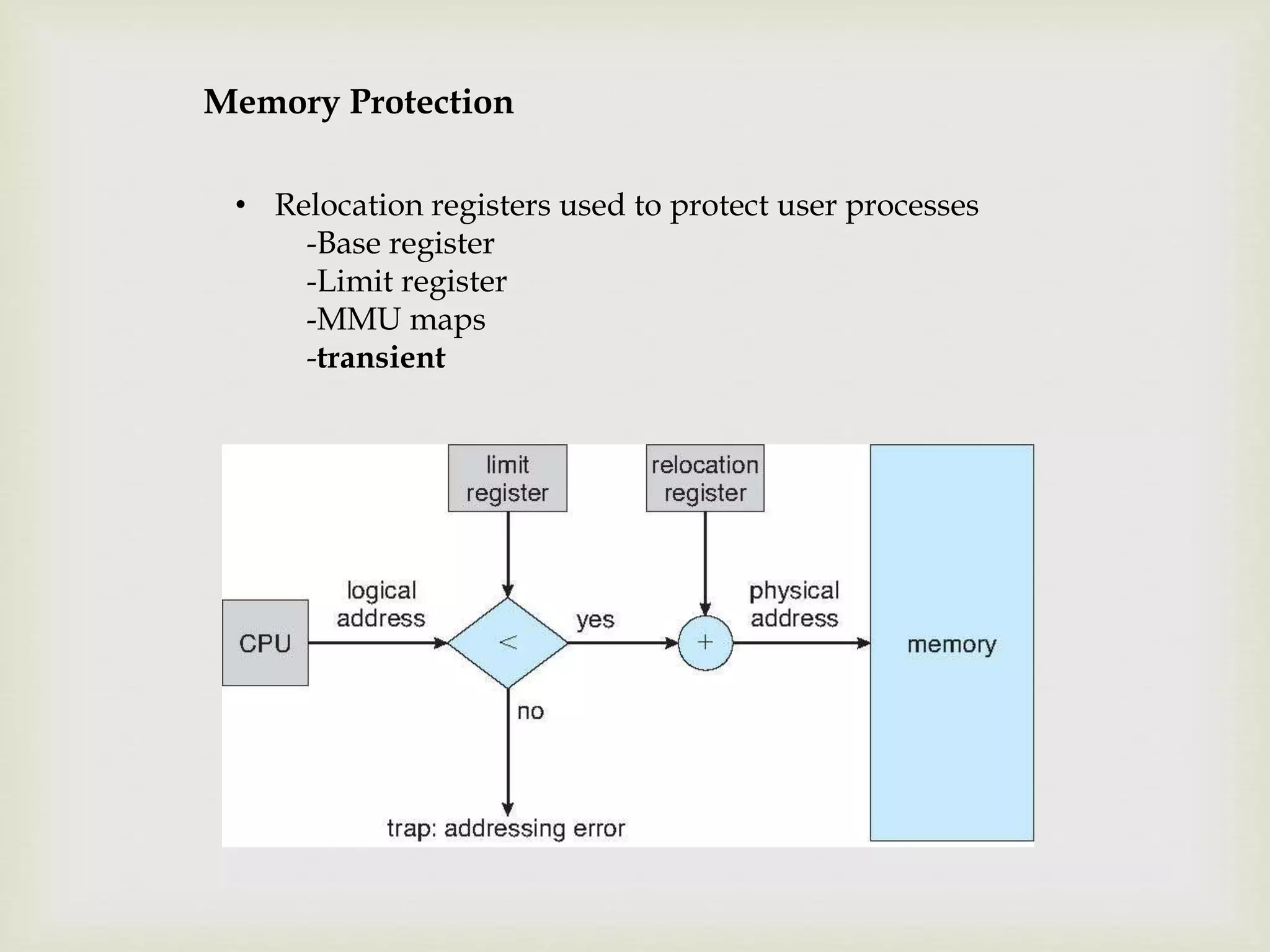
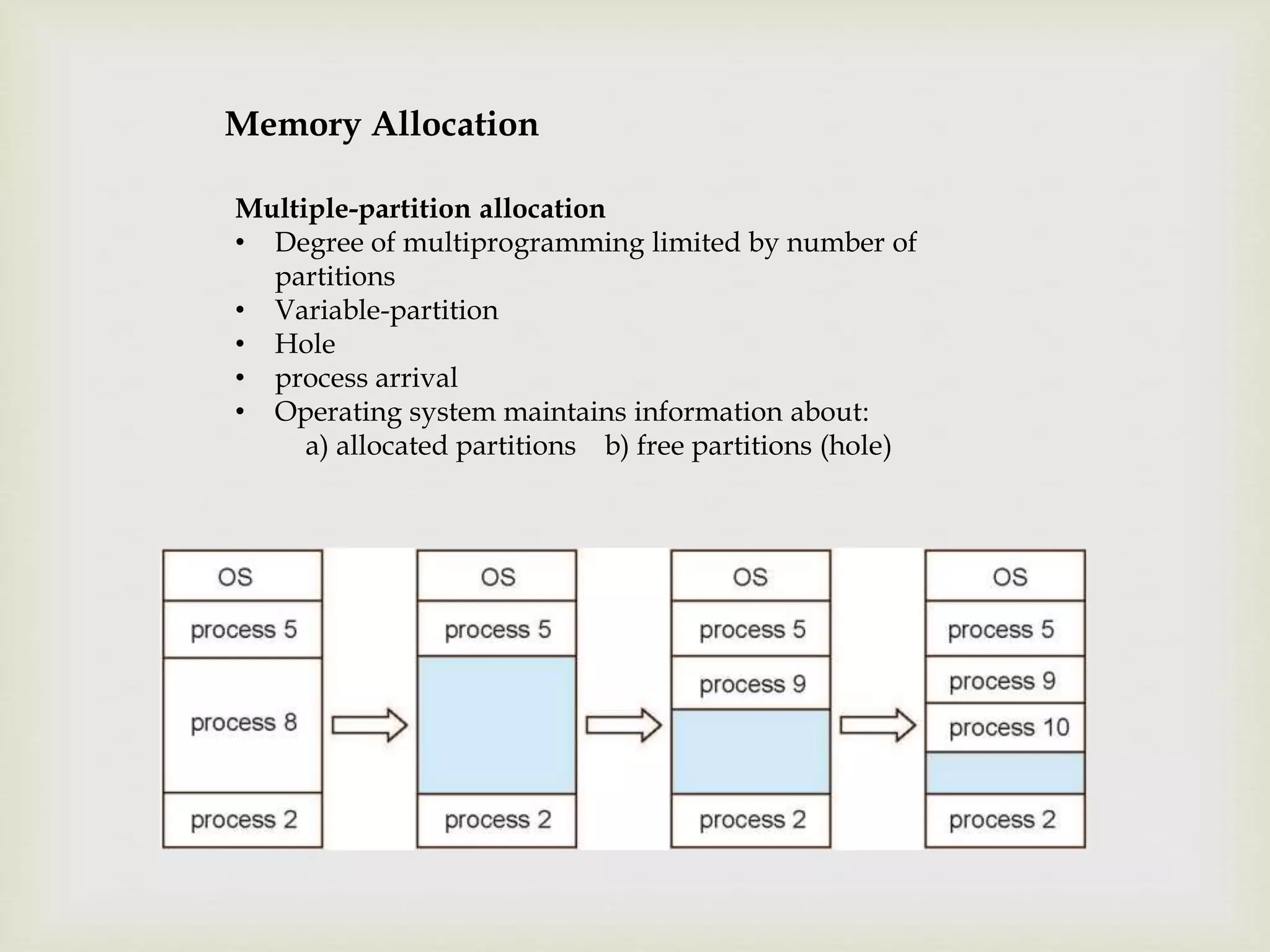
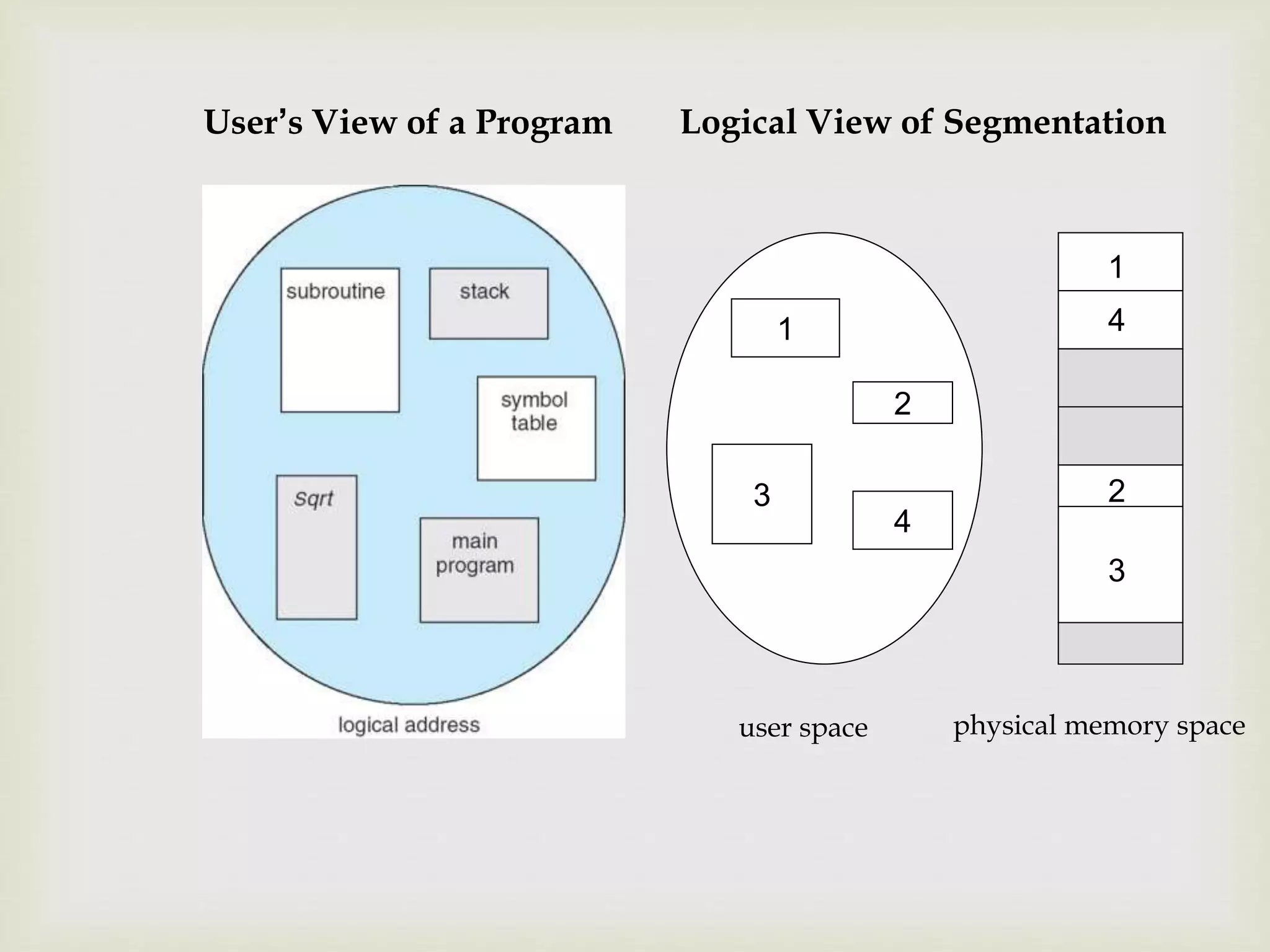
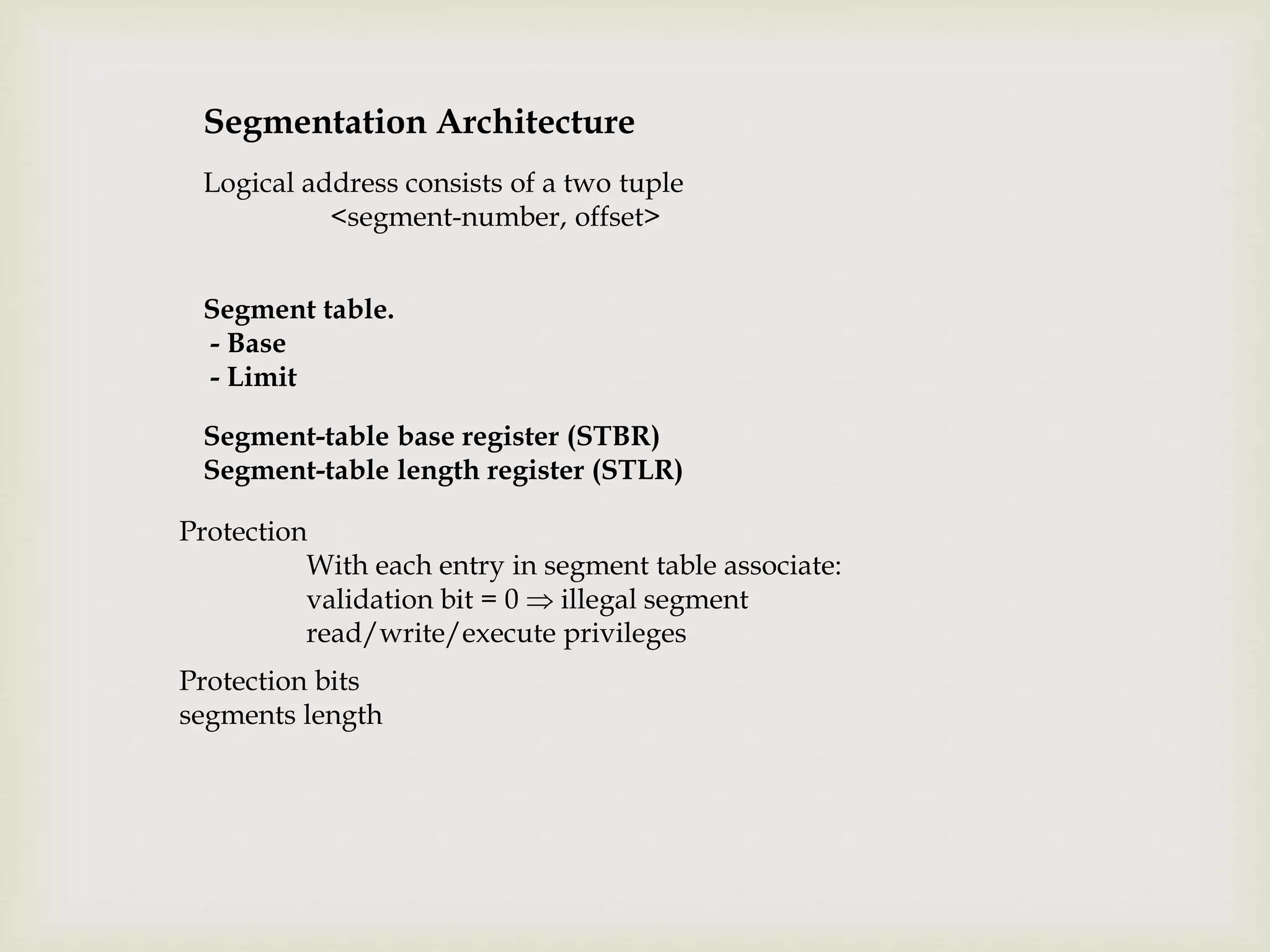
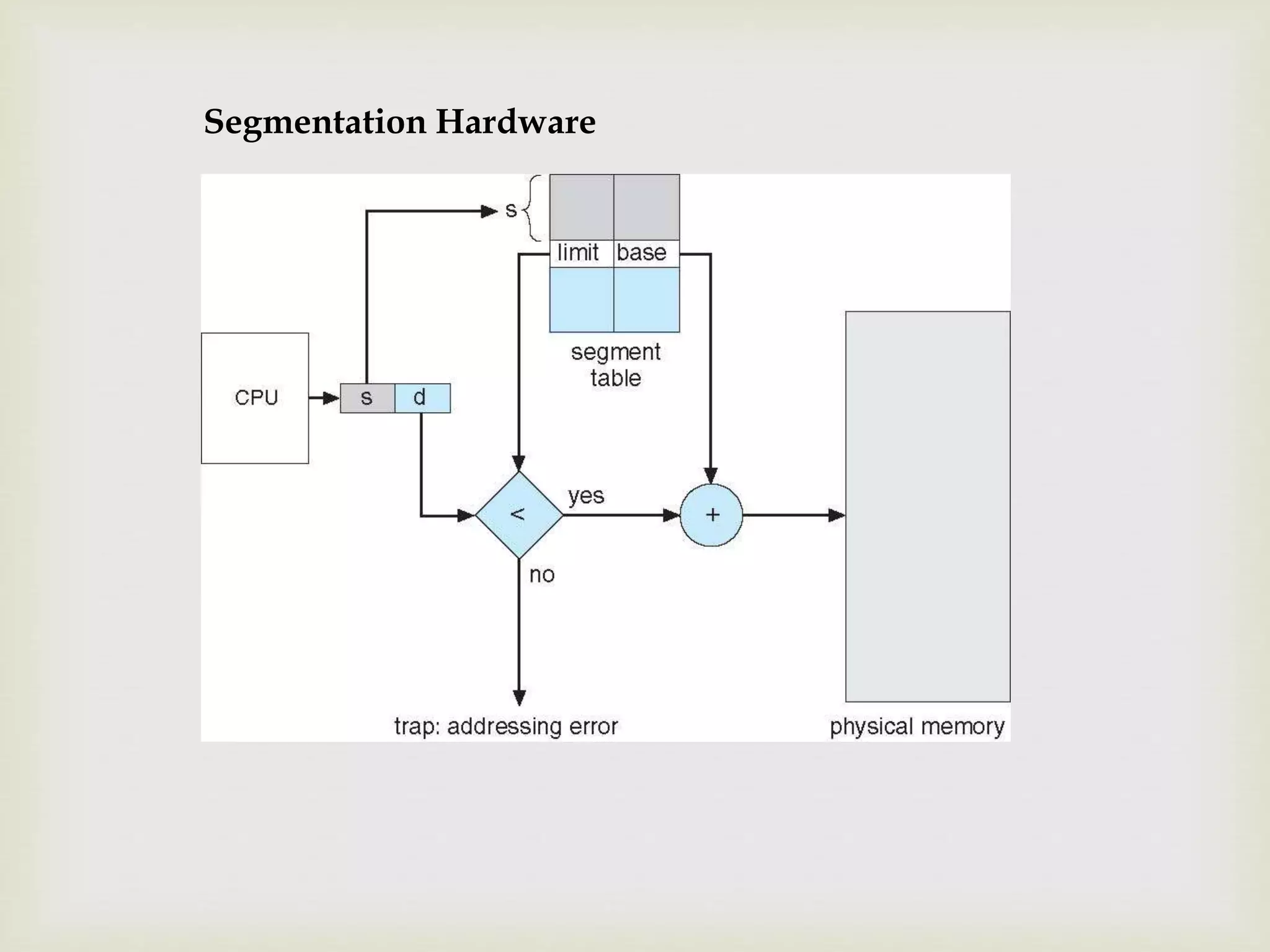
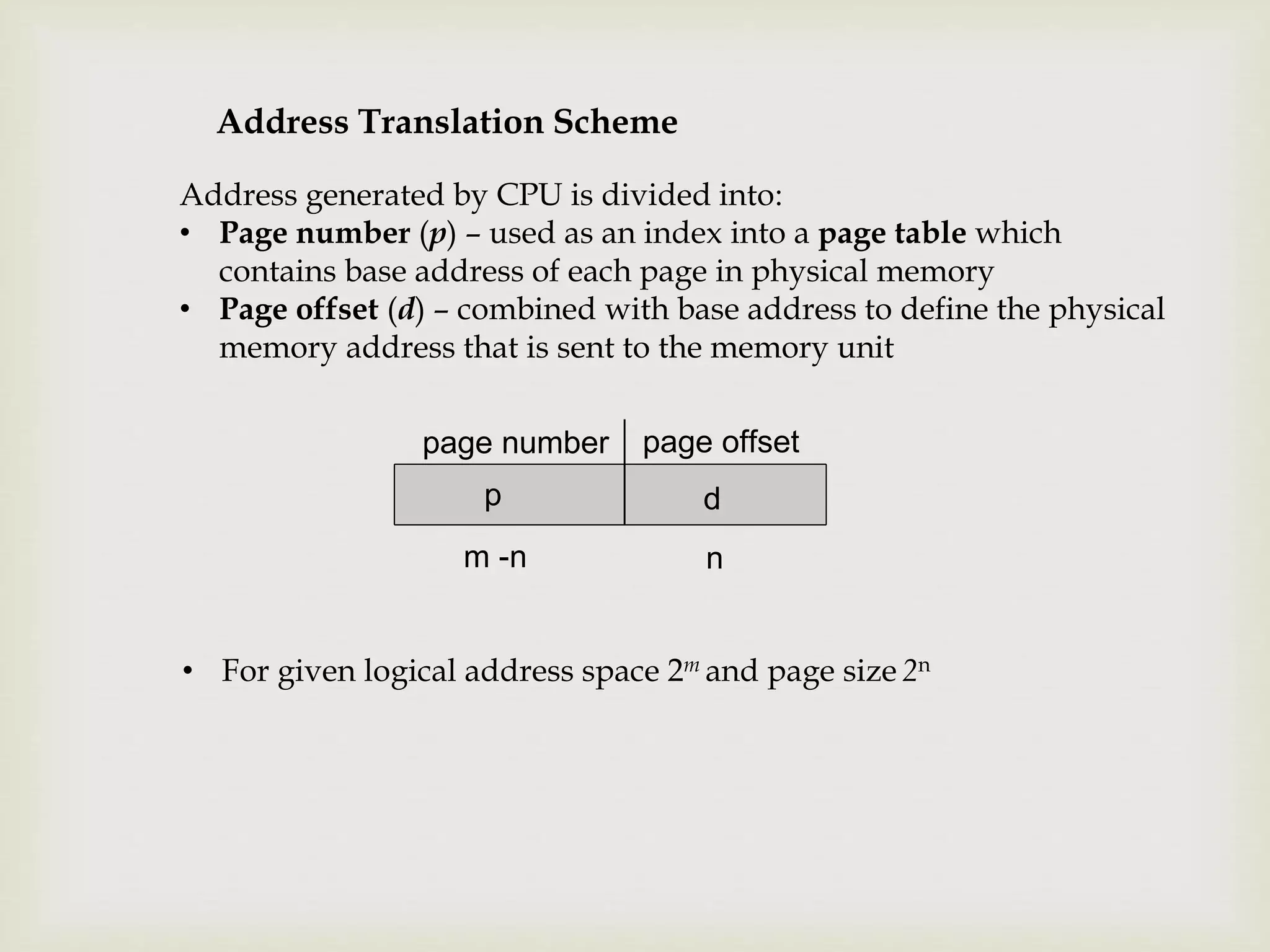
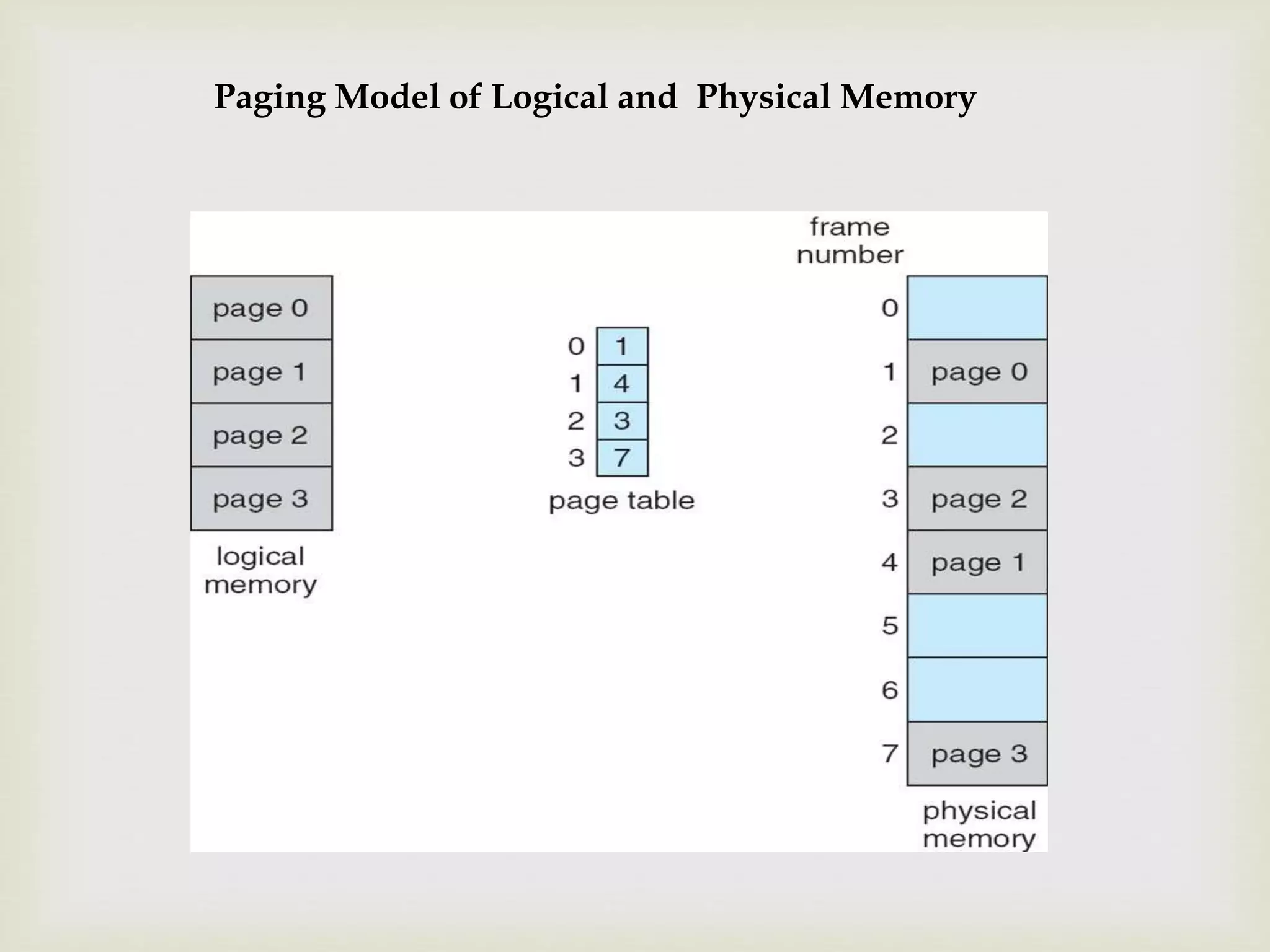
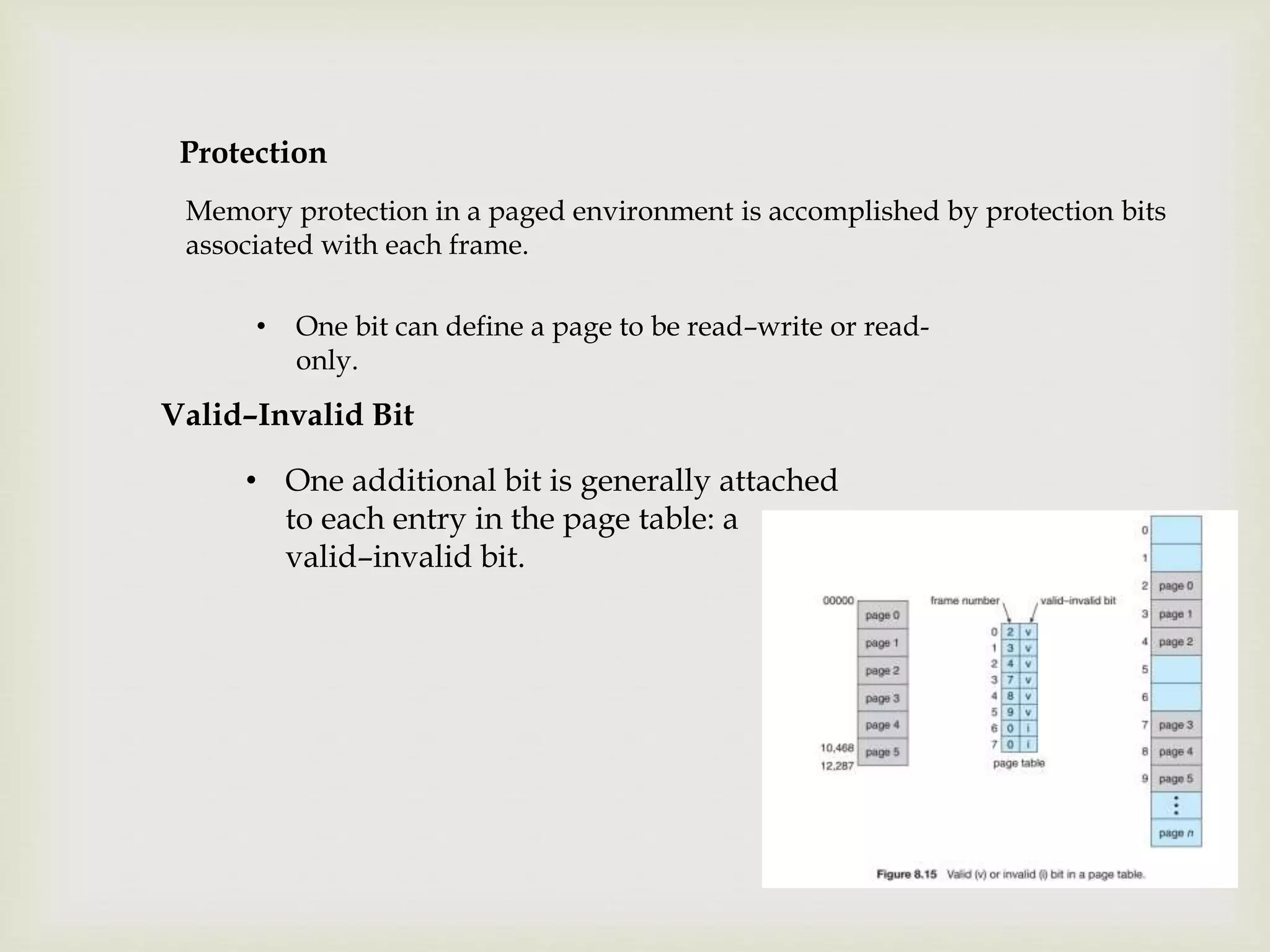
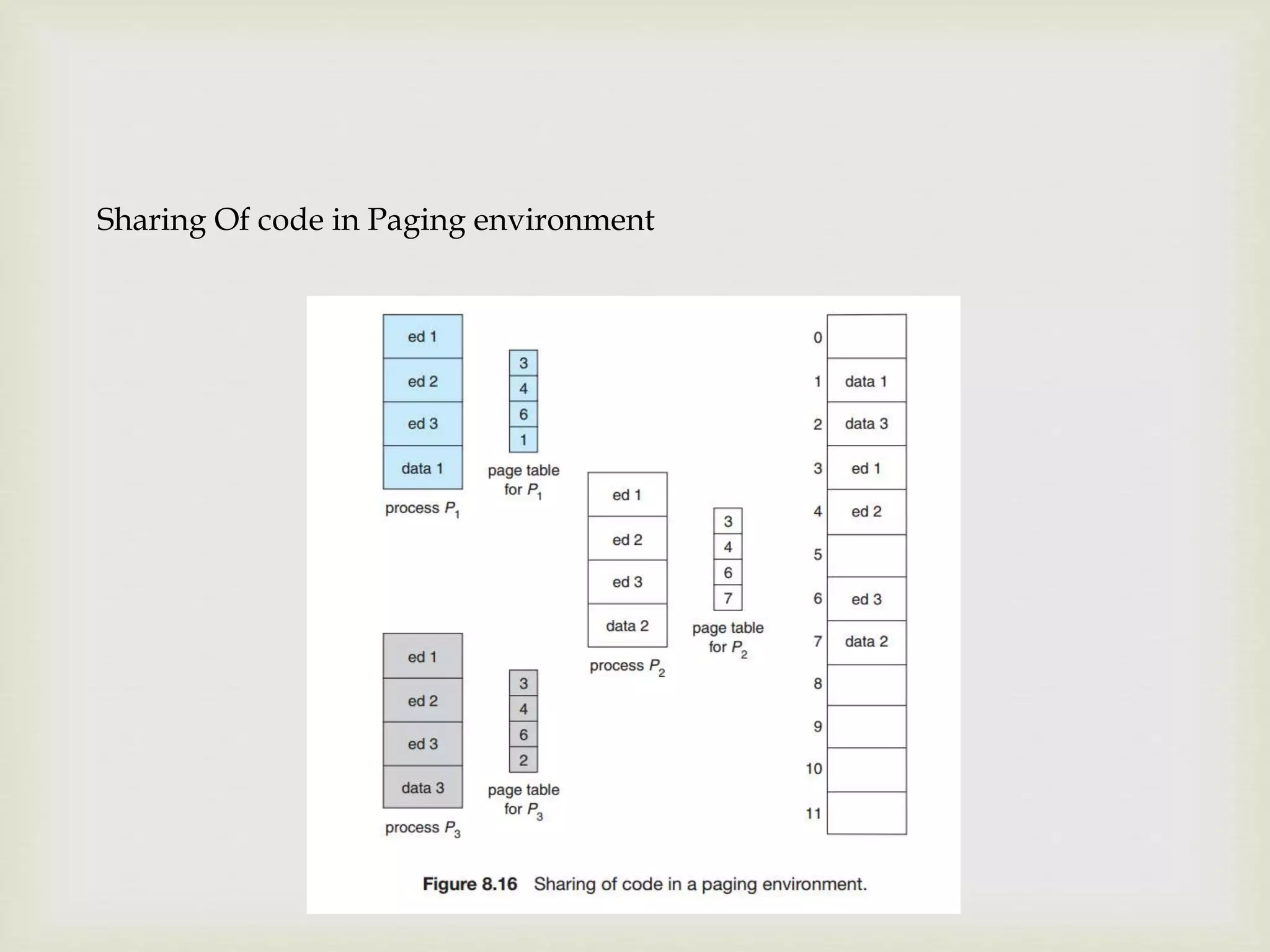
This document discusses various memory management techniques used in operating systems, including memory protection using base and limit registers, address binding at compile, load, and execution times, logical vs physical address spaces, memory allocation using contiguous and multiple partition schemes, segmentation using segment tables, and paging using page tables. Paging allows for non-contiguous allocation of physical memory through the use of pages and frames, address translation via a page table with page and offset, and protection bits. It aims to reduce fragmentation and support sharing of common code through reentrant code.