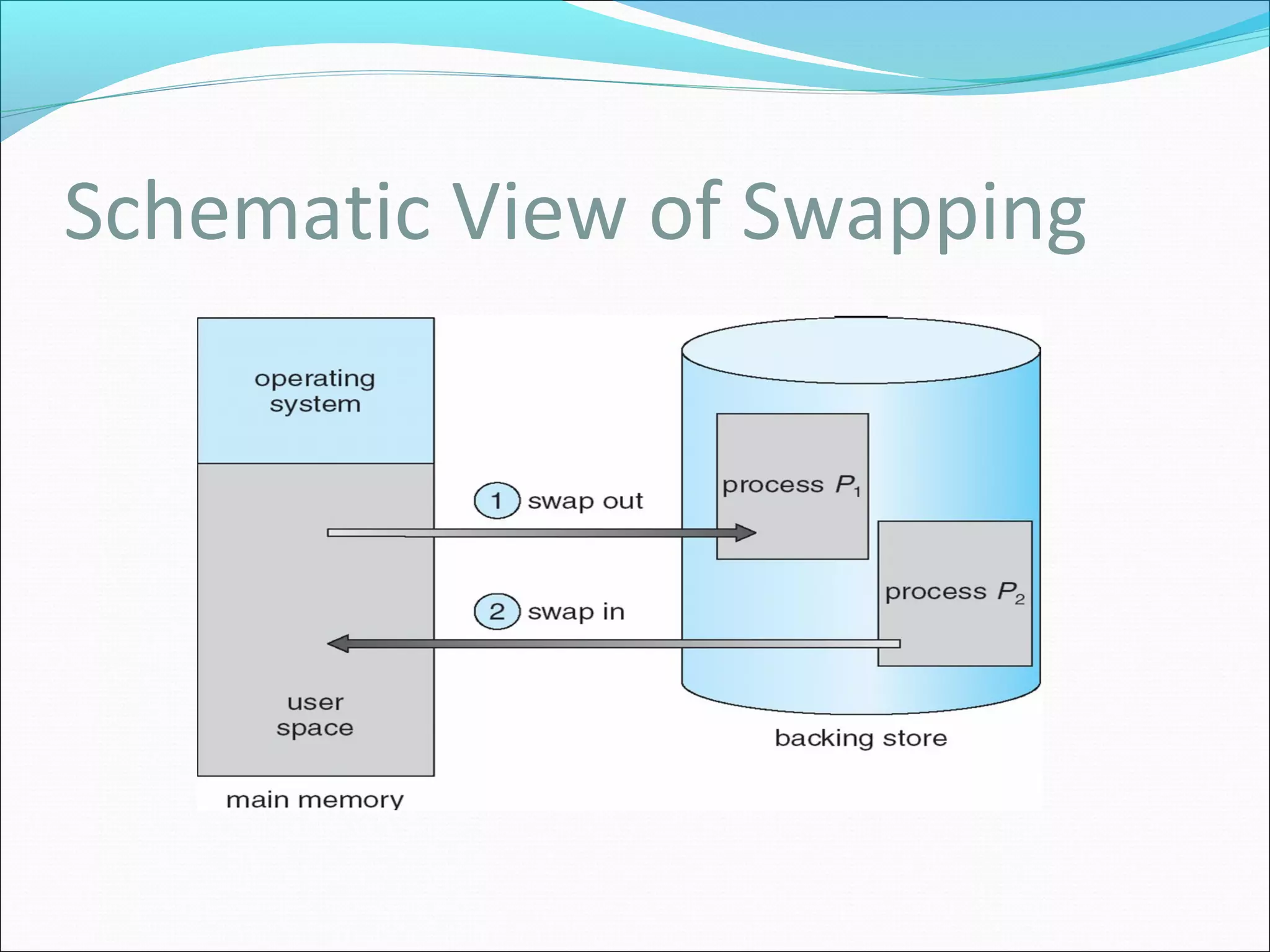
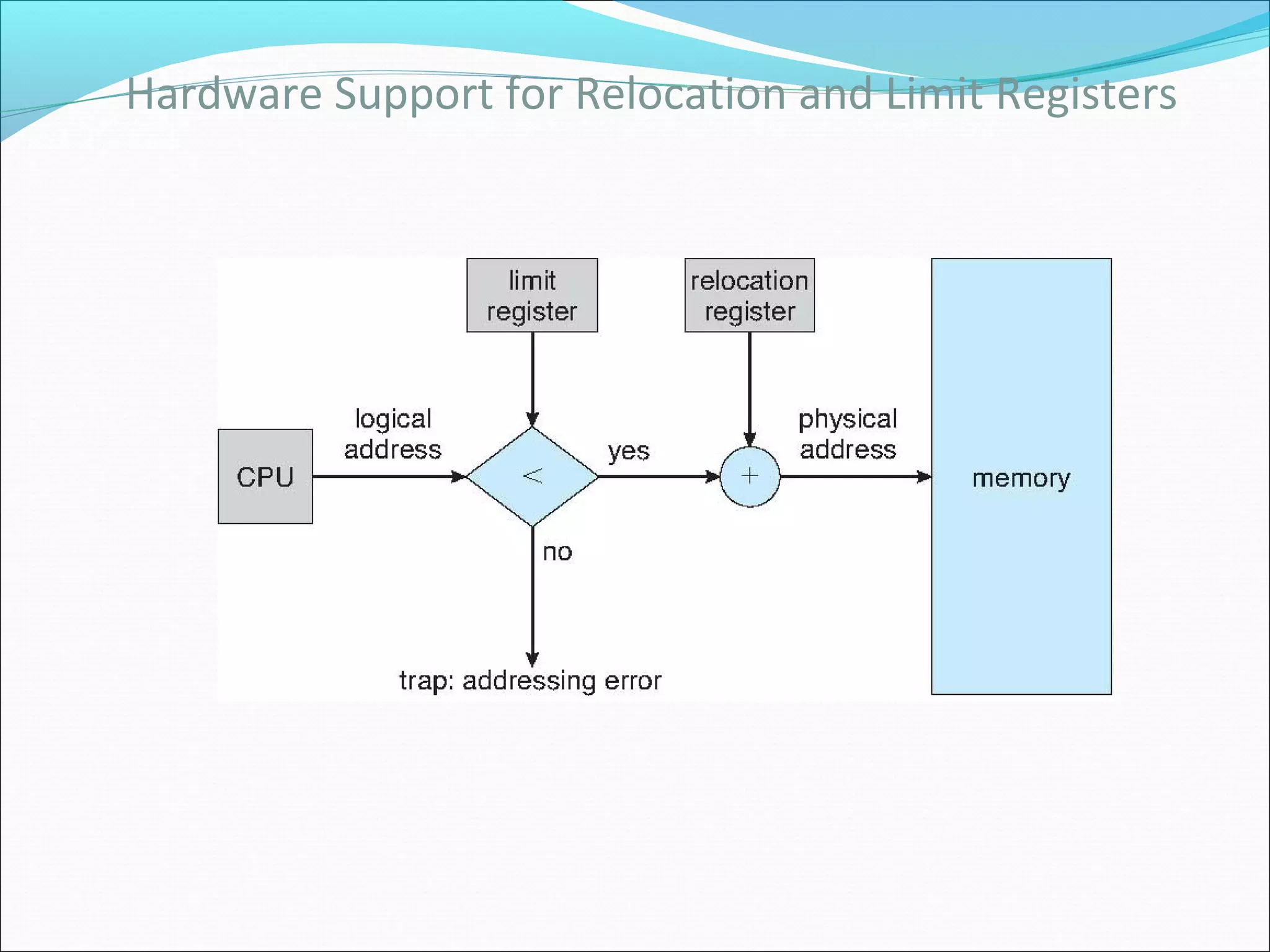
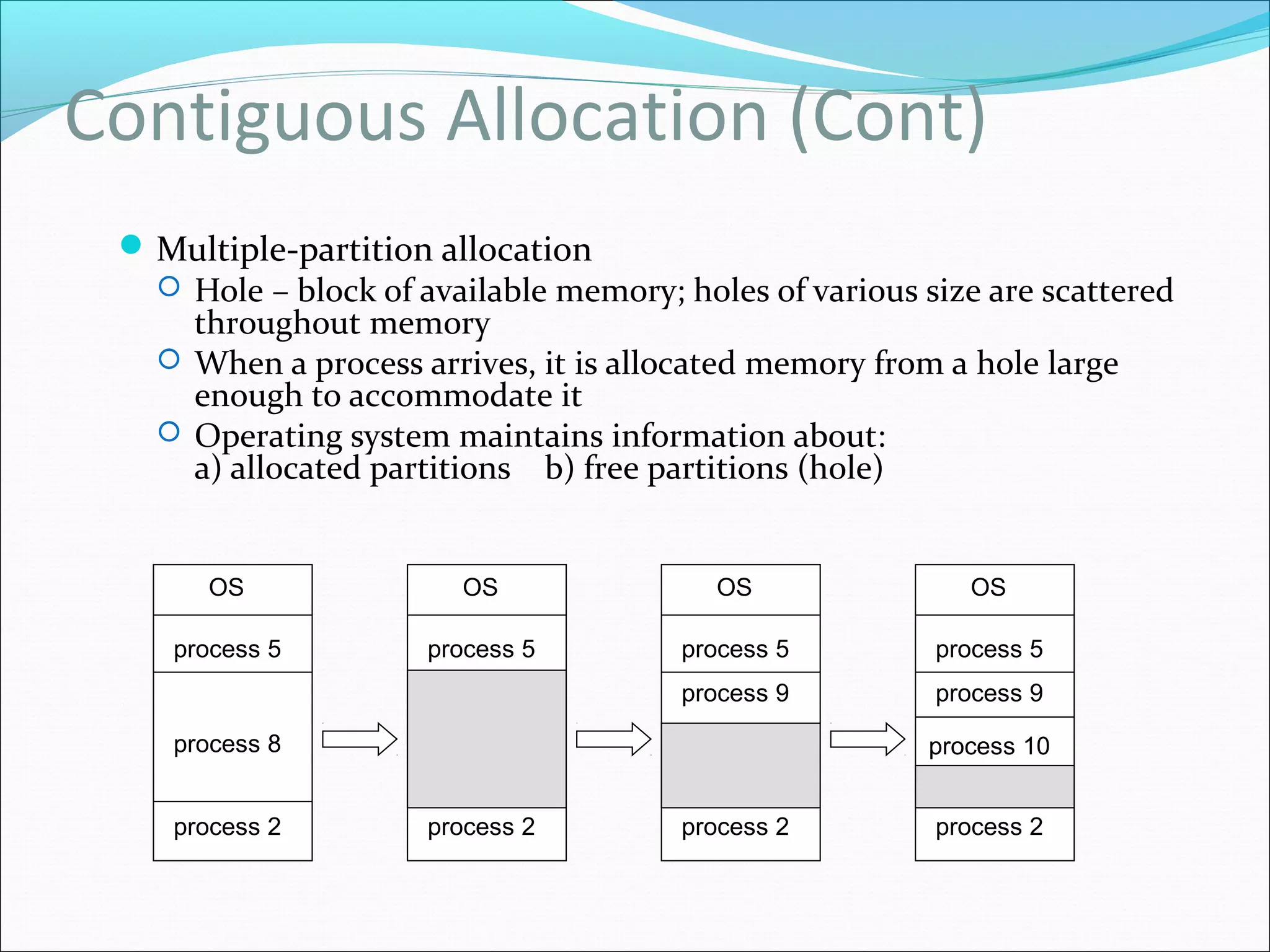
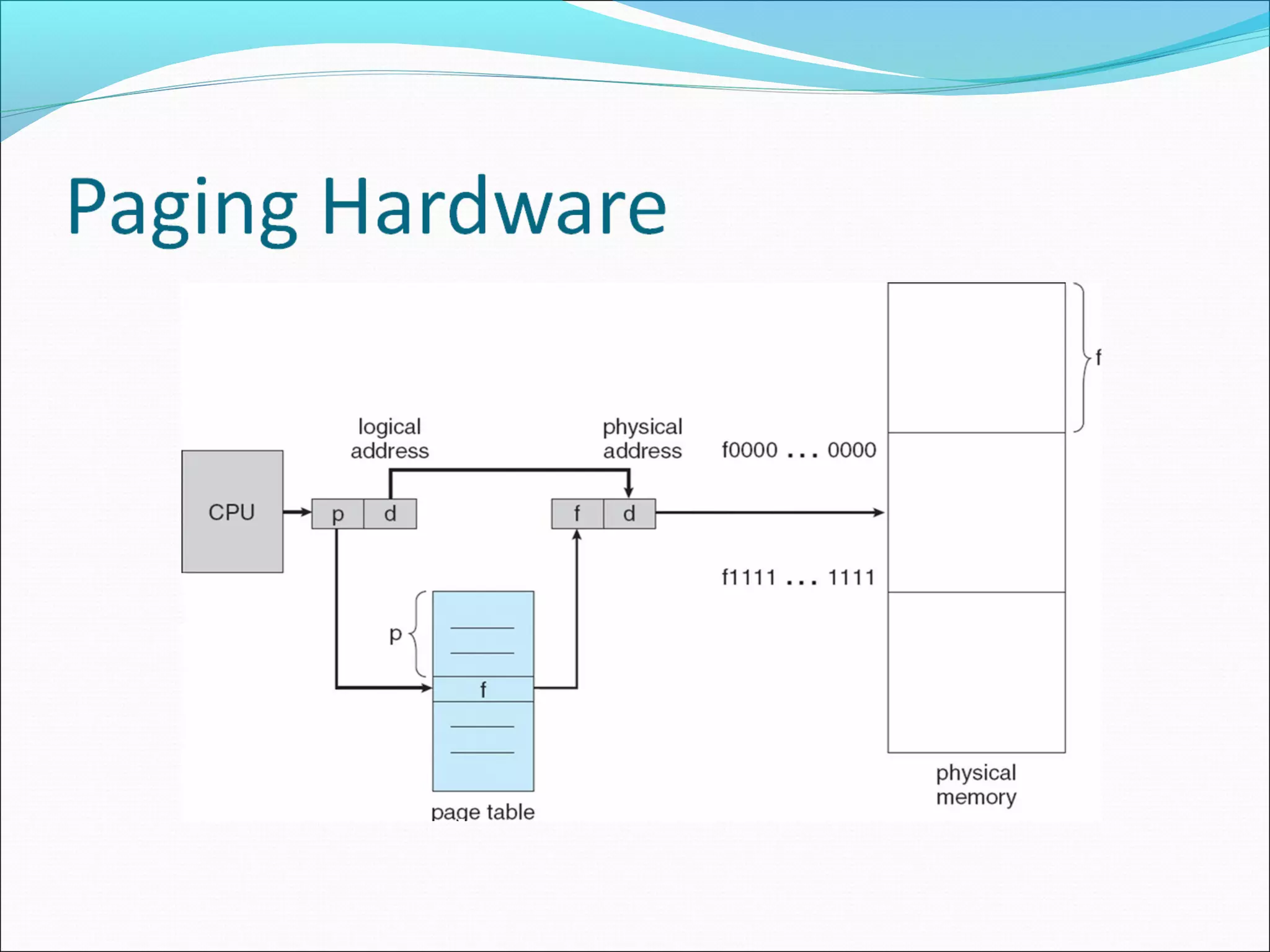
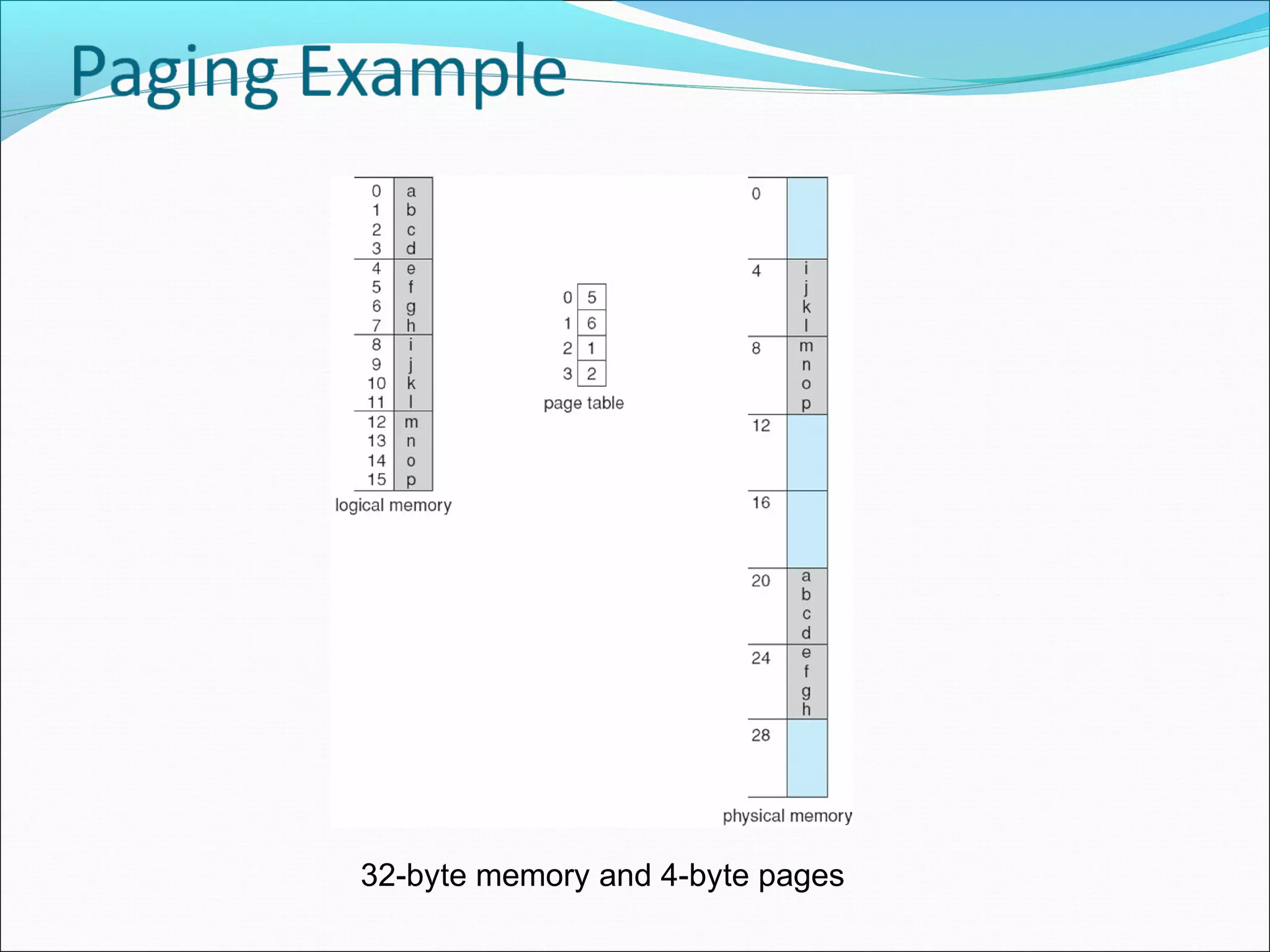
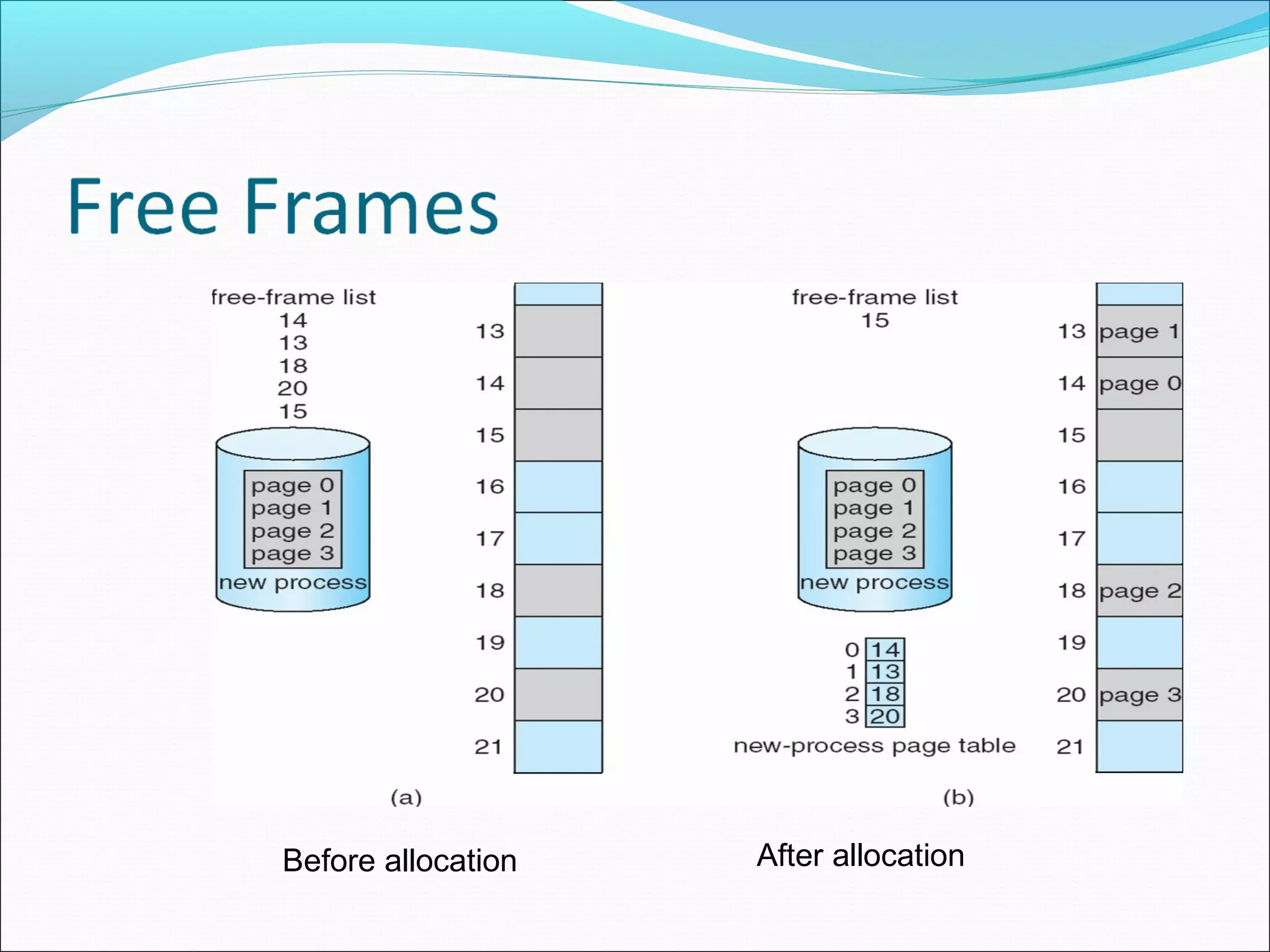
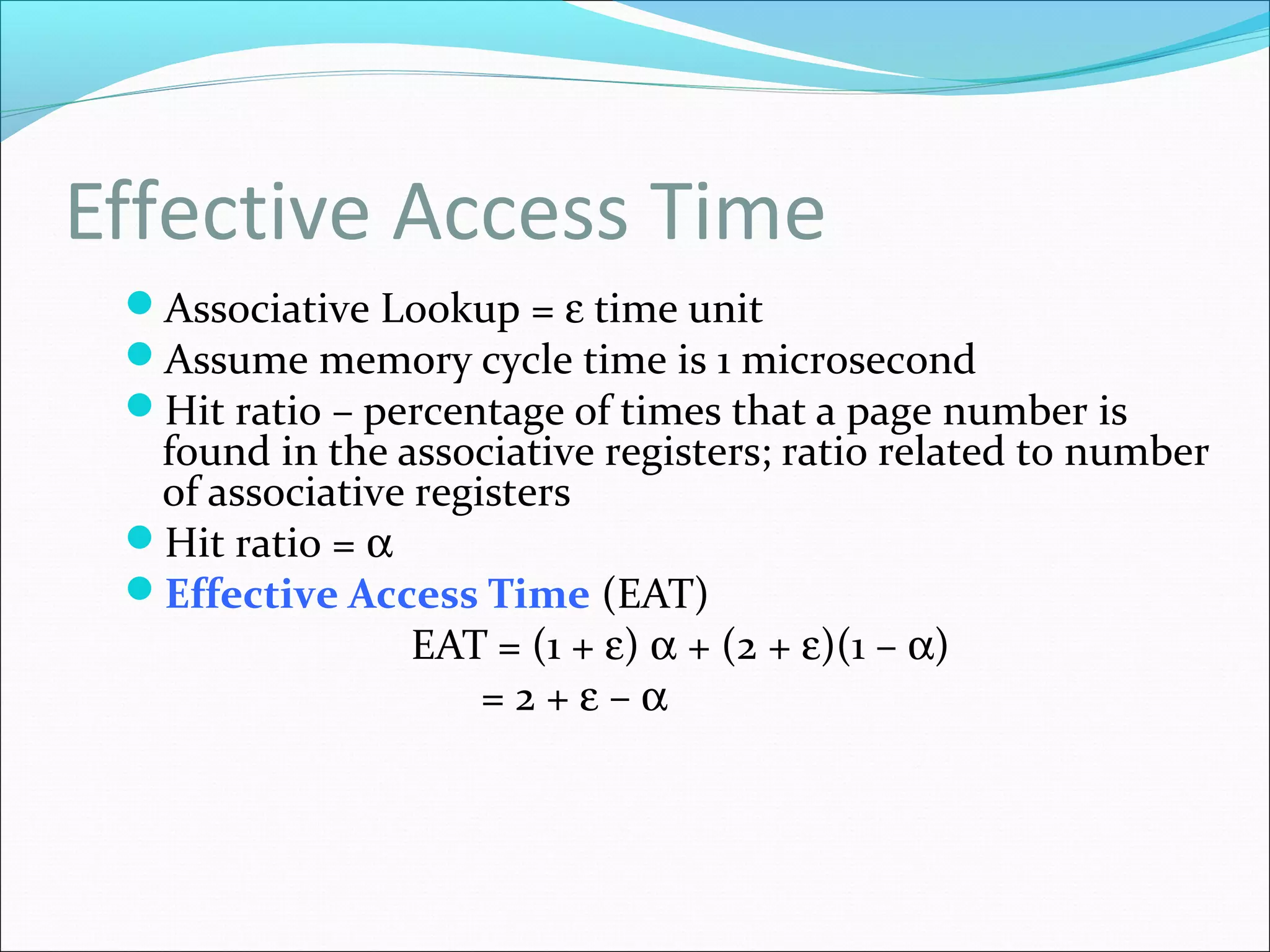
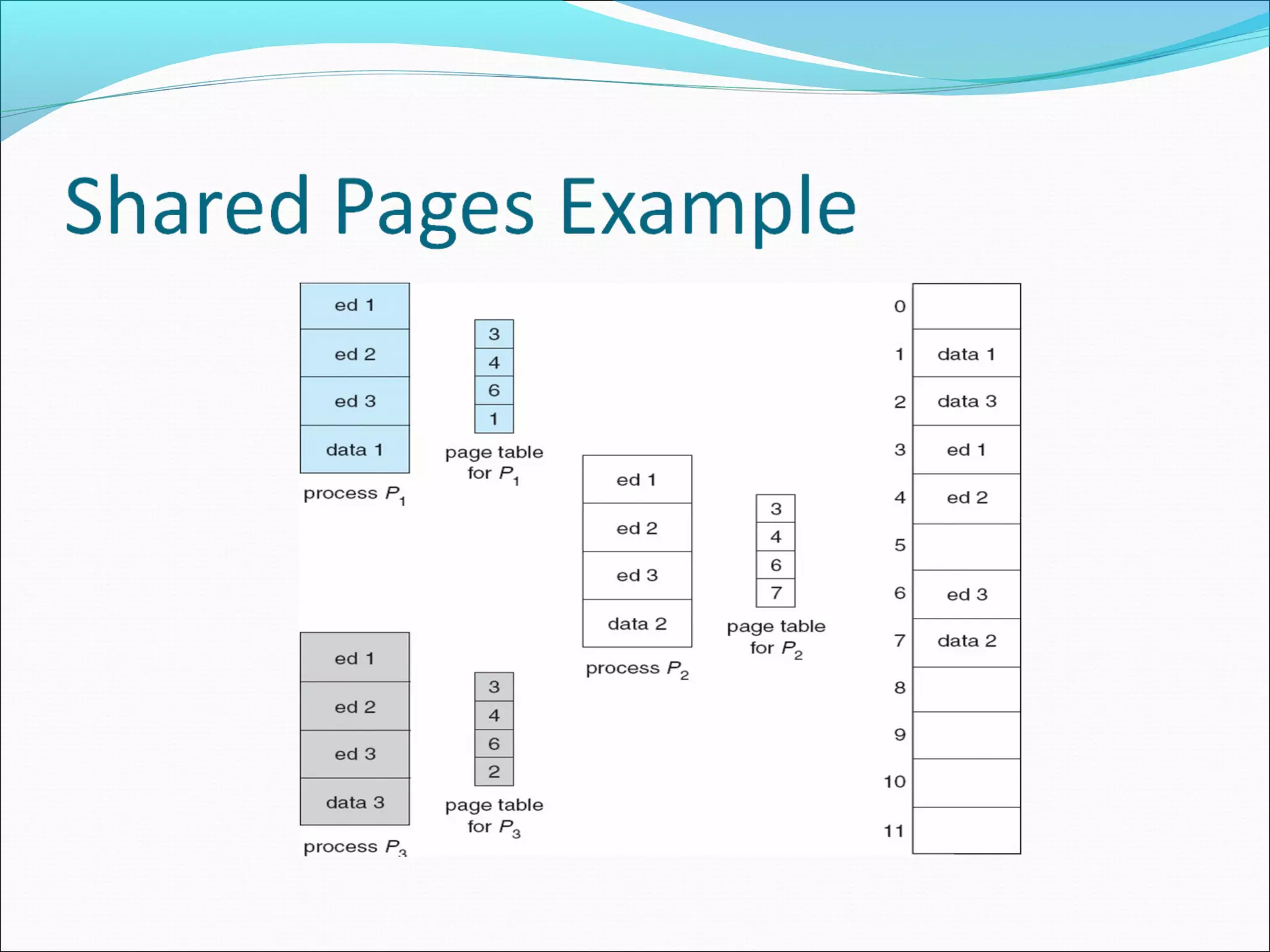
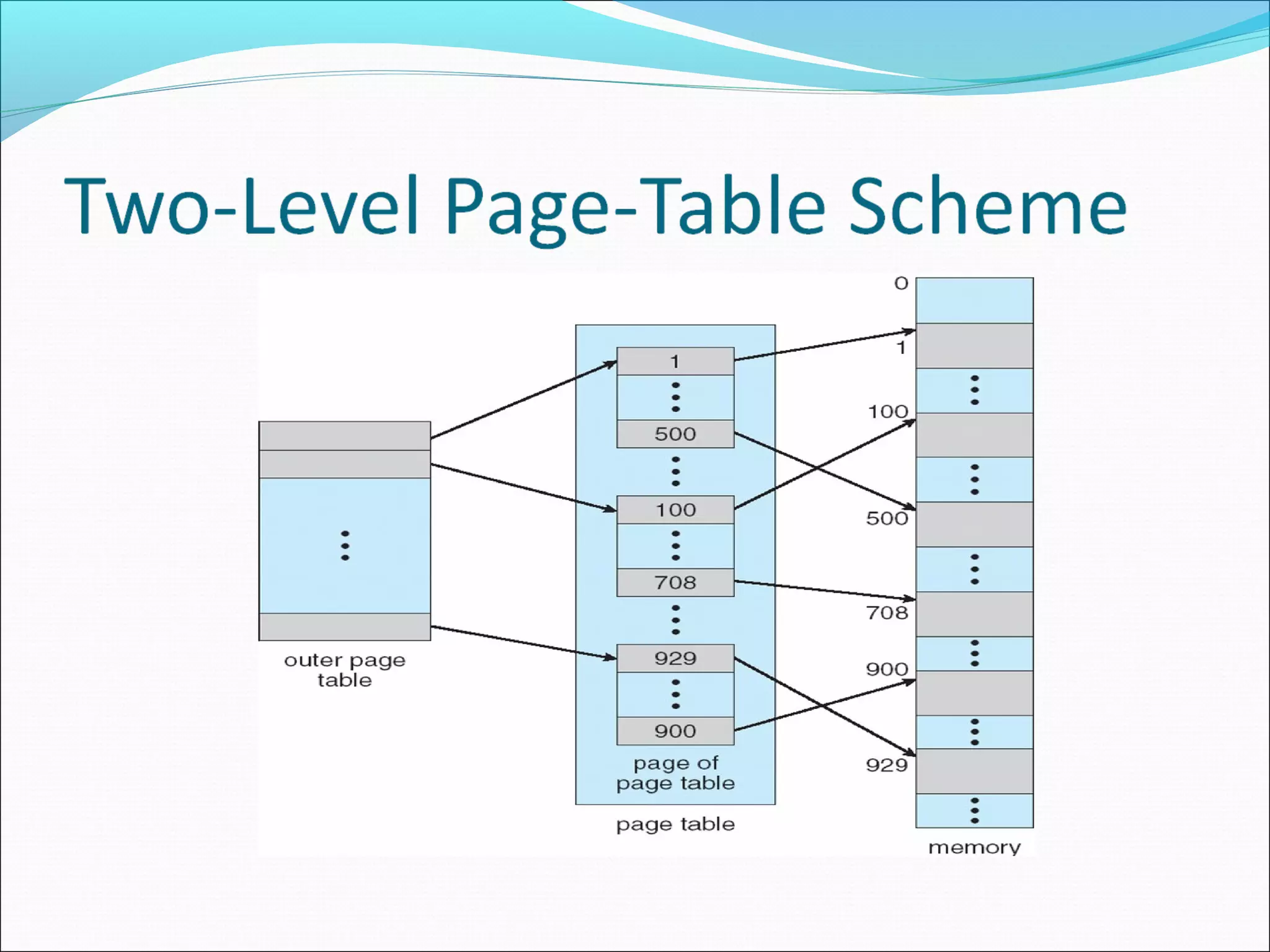
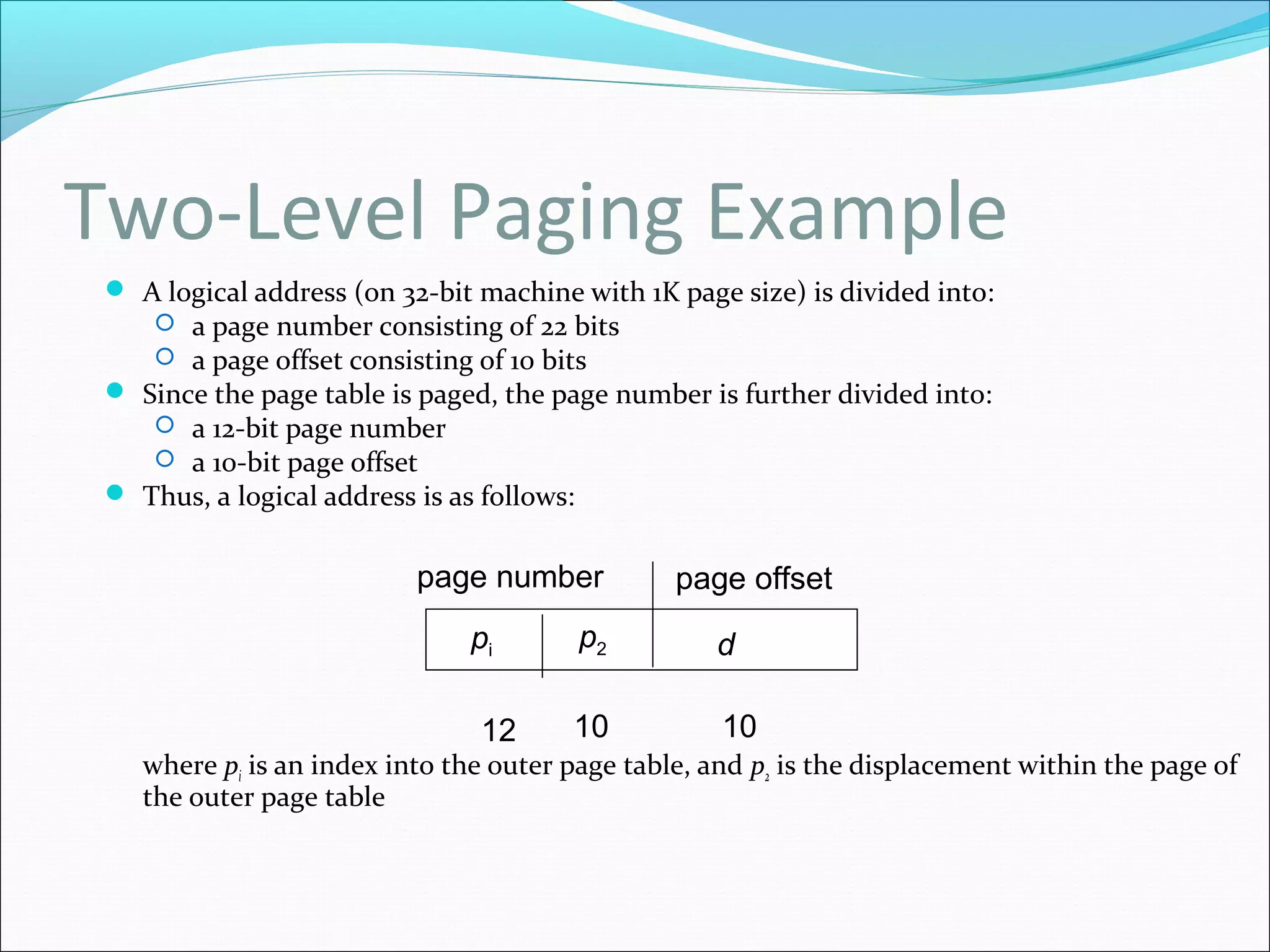
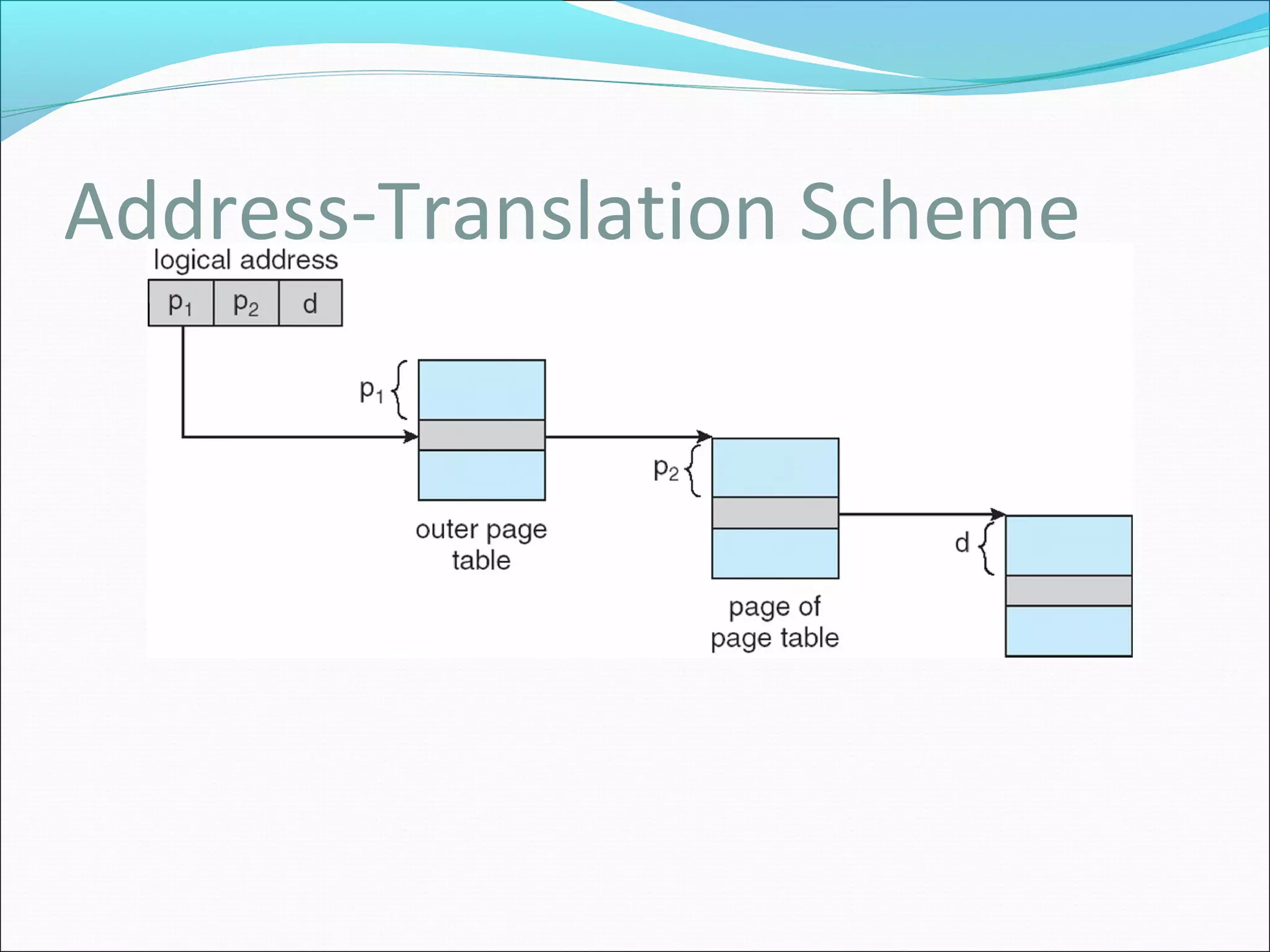
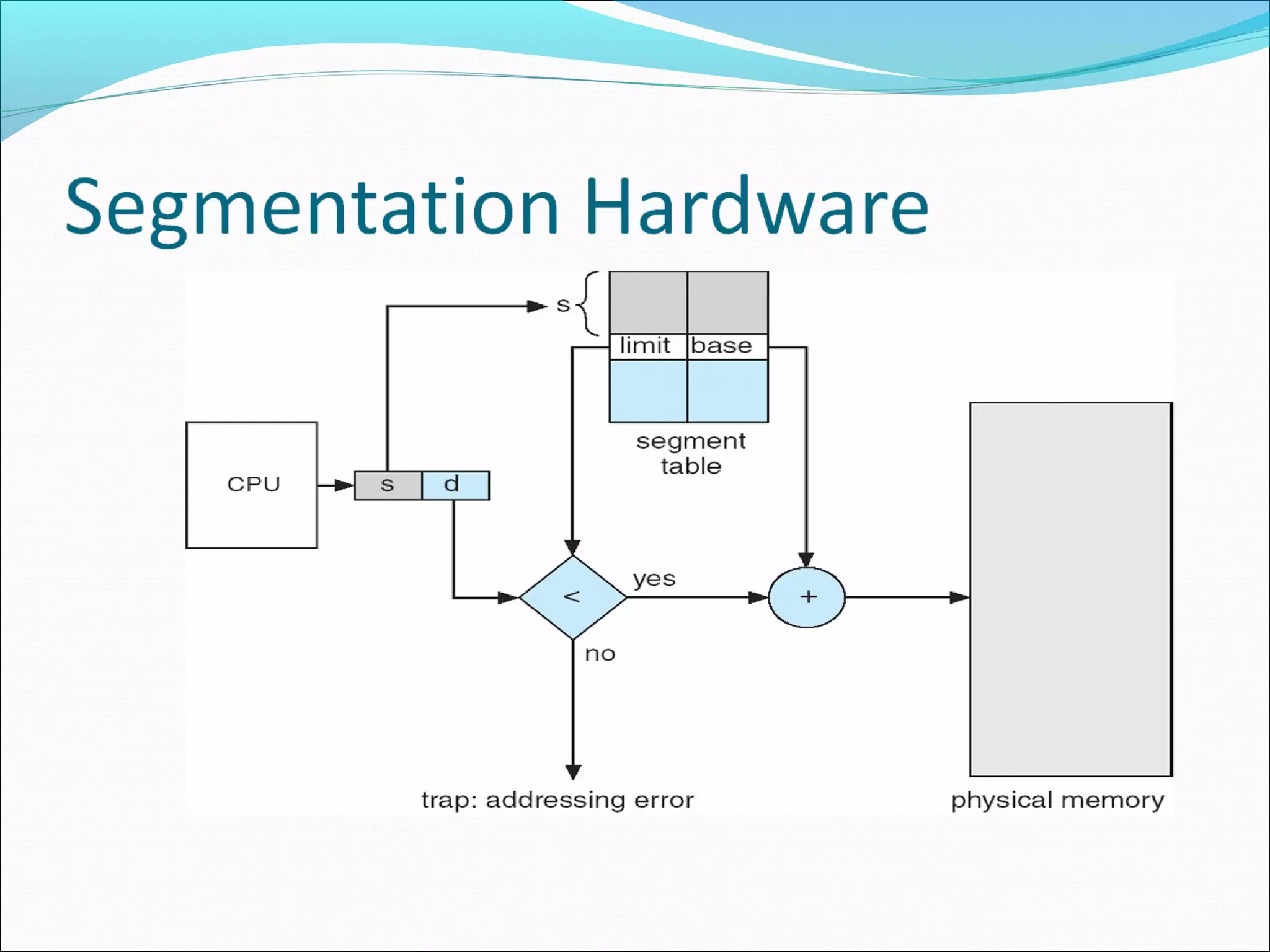
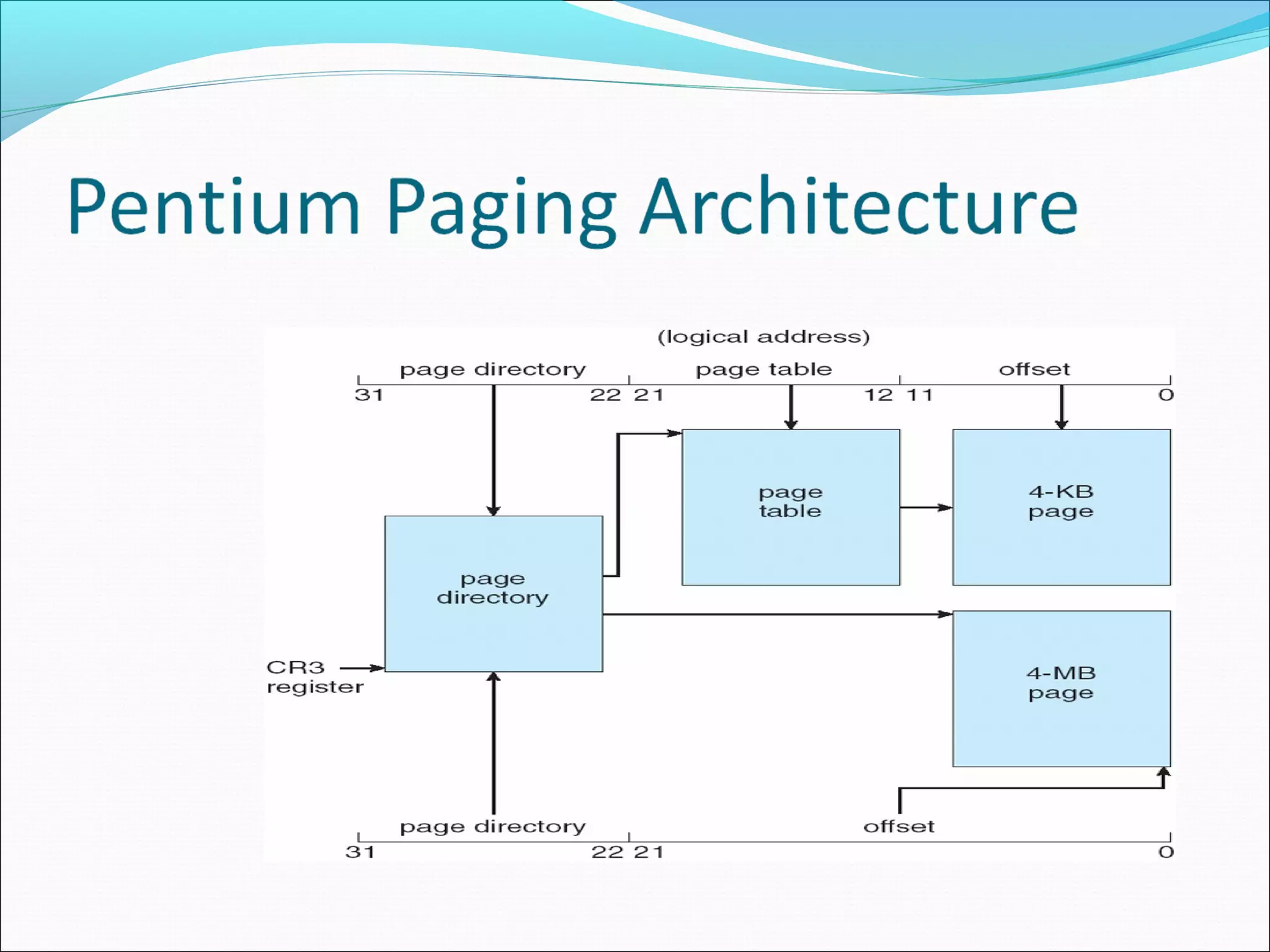
The document provides an extensive overview of memory management techniques, including swapping, contiguous memory allocation, paging, and segmentation. It covers key concepts such as logical vs. physical address spaces, address binding methods, dynamic loading, and linking, along with hardware implementation like the memory-management unit (MMU) and page tables. The Intel Pentium's architecture, which supports both segmentation and paging, is highlighted as an example of these principles in action.