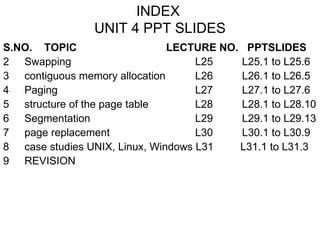
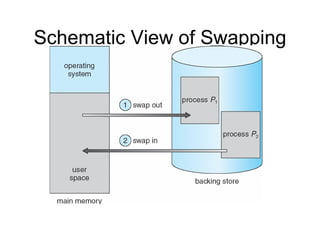
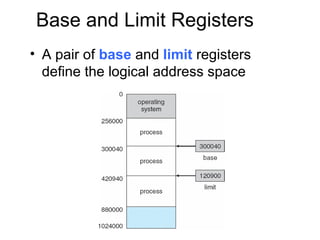
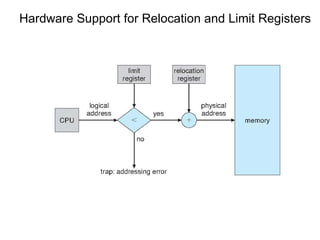
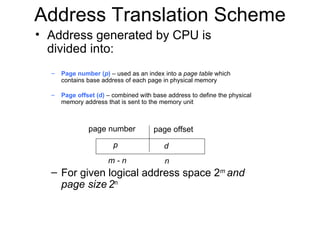
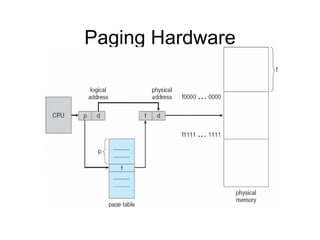
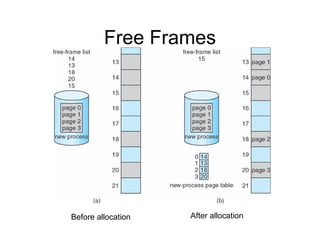
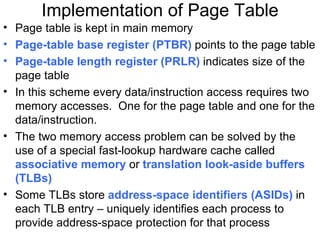
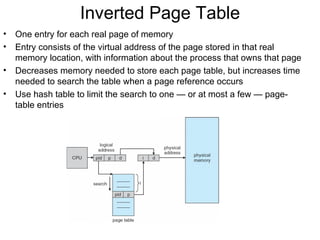
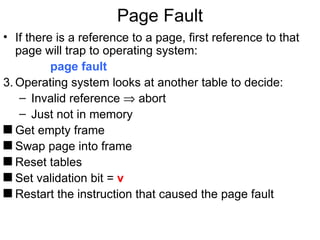
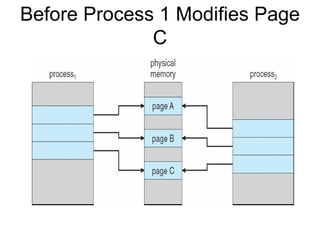
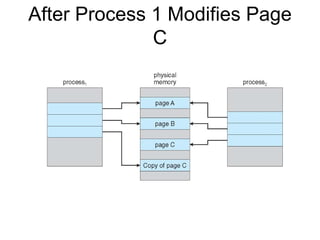
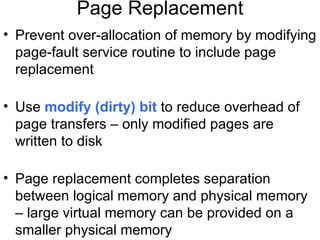
This document contains slides from a lecture on operating system concepts including swapping, contiguous memory allocation, paging, segmentation, and page replacement. It discusses key topics such as logical vs physical addresses, page tables, translation lookaside buffers, demand paging, and page faults. The document includes 10 slides with diagrams and explanations of these operating system memory management techniques.