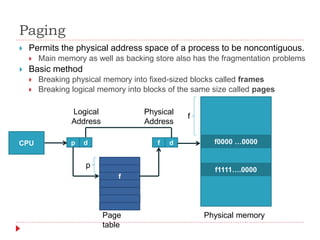
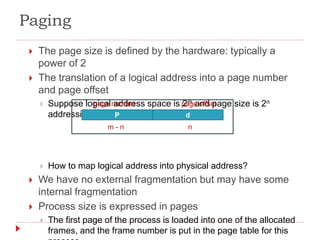
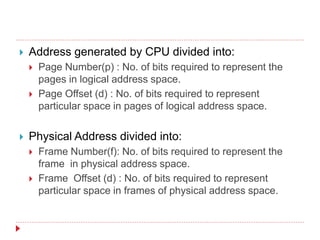
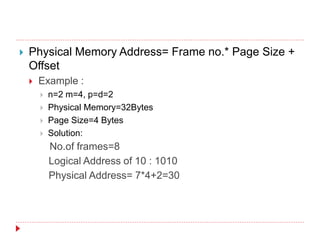
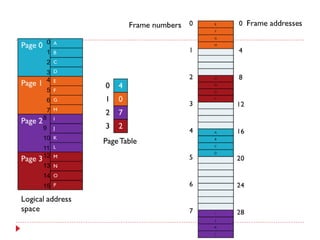
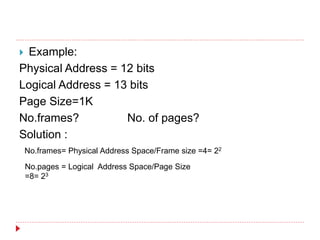
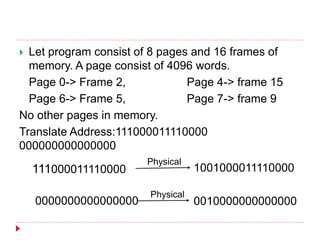
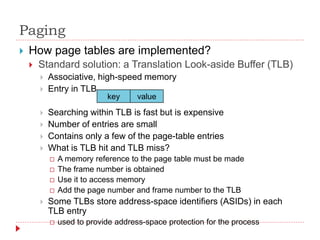
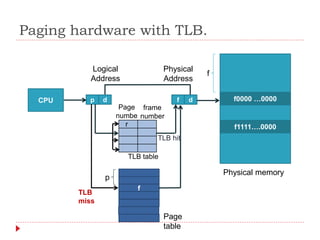
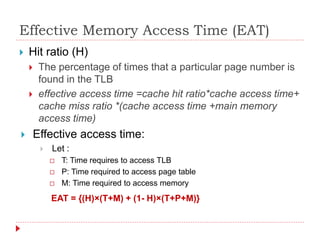
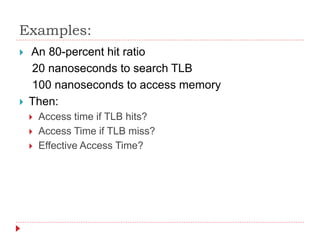
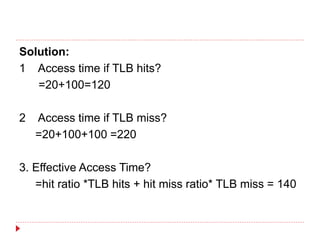
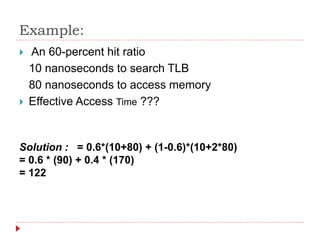
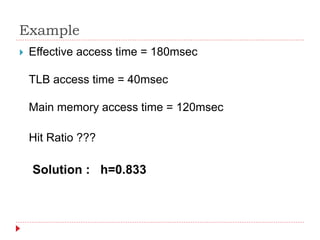
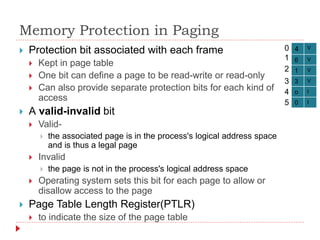
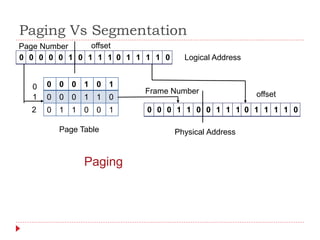
Main Memory Management techniques include paging and segmentation. Paging divides both logical and physical memory into fixed-size blocks called pages and frames respectively. The CPU address is divided into a page number and page offset. The page number is used to index a page table to map the logical page to a physical frame. A Translation Lookaside Buffer (TLB) is used to cache recent page table entries to speed up virtual to physical address translation and reduce memory accesses on TLB hits.