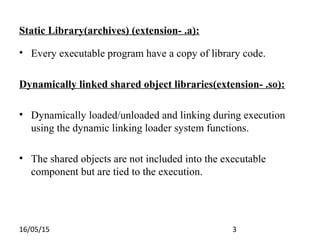
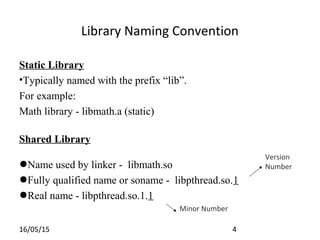
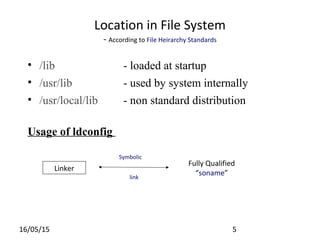
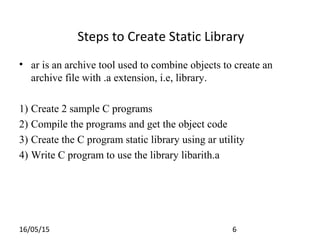
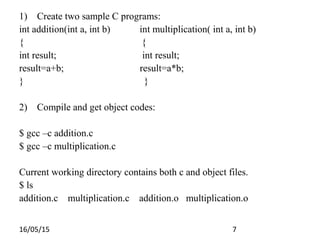
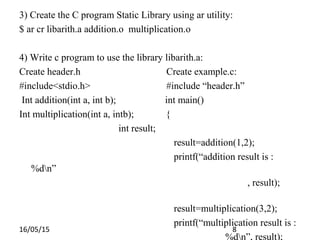
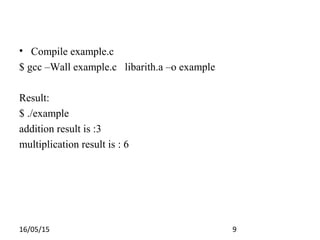
The document discusses libraries in programming, distinguishing between static libraries (with .a extension) and dynamic/shared libraries (.so). It describes the creation and use of these libraries using the 'ar' utility for static libraries and the process for developing shared libraries in C. Key steps include compiling source code, creating header files, linking the code, and executing programs with the libraries.
![16/05/15 13
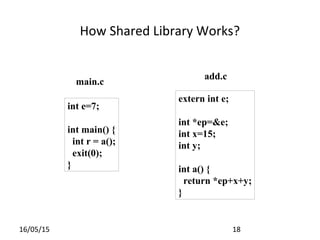
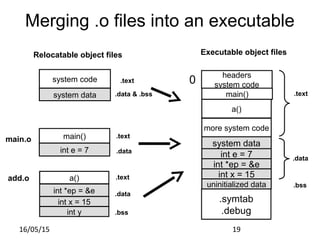
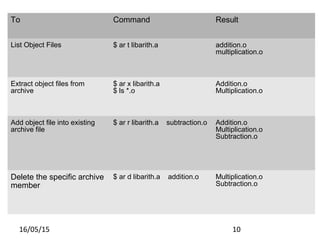
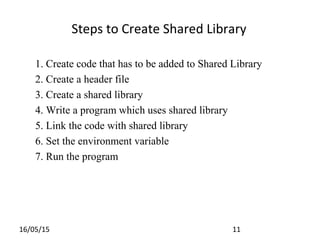
Step 3.
gcc –c –Wall – werror –fPIC shared.c
gcc –shared –o libshared.so shared.o
Step 4.
#include<stdio.h>
#include”shared.h”
int main(void)
{
unsigned int a=1;
unsigned int b=2;
unsigned int result =0;
result=add(a,b);
printf(“n the result is [%u]n”, result);
return 0;
}](https://image.slidesharecdn.com/librariesnew-150516122851-lva1-app6892/85/Libraries-13-320.jpg)
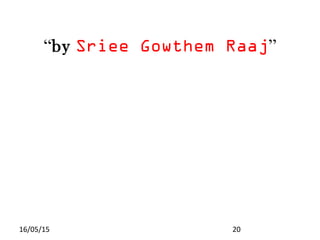
![16/05/15 14
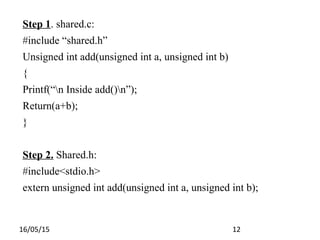
Step 5.
gcc –L/home/Desktop/practice/ -wall main.c –o main –lshared
Step 6.
export LD_LIBRARY_PATH=/home/desktop/practice:$
LD_LIBRARY_PATH
Step 7.
$ ./main
Inside add()
The result is [3]](https://image.slidesharecdn.com/librariesnew-150516122851-lva1-app6892/85/Libraries-14-320.jpg)